At times, rather than using the theory of logic and reasoning, we follow our gut instinct to understand things instinctively. Hacking is one such instance where this principle may be followed. Hackers can get access to your devices in surprising ways and manifest themselves into different avatars that we might not be aware of. IRC Clients, Trojans, and Backdoors are some of the malicious programs that are used to hack computers. The least we can do is look for possible indicators suggesting we might have been hacked and then look for some quick action against it. Here’s how you can know if your Windows computer has been hacked.
How do I know if my computer has been hacked?
You know that your computer has been hacked and compromised if you see the following signs:
- Your online passwords or settings have been changed
- Your computer’s local account passwords have been changed, or you see new User Accounts
- You see strange posts ‘made by you’ in your social feeds. Or maybe your ‘Friends’ are receiving inappropriate messages, allegedly from you.
- Your friends are reporting receiving strange spam or emails from you.
- You find that new programs or toolbars have been installed on your computer.
- You receive messages from fake antivirus or other rogue software
- Your Internet speed has become sluggish and slow
- There is a marked increase in Network activity.
- Your Firewall is busy blocking several outward connection requests
- Your security software has been disabled.
- The home page or default browser search engine has been hijacked
- Your mouse moves automatically to make selections
- You start getting calls from your Bank, Credit Card company, Online Store about non-payment, dip in the bank balance, unexpected outstanding balances or purchases.
Let us take a look at some of these signs in detail, in no specific order.
Change in online passwords
If you notice one or more of your online passwords have changed suddenly, you’ve more than likely been hacked. Here, usually what occurs is that the victim unknowingly responds to an authentic-looking Phishing email that purportedly claimed to be from the service ending up with the changed password. The hacker collects the log-on information, logs on, changes the password, and uses the service to steal money from the victim or the victim’s acquaintances. See how you can avoid Phishing Scams and Attacks and take steps to prevent your Online Identity Theft.
As a damage control action, you can immediately notify all your contacts about the account compromised. Second, immediately contact the online service to report the compromised account. Most online services are aware of this sort of maliciousness and have the requisite strength and expertise to restore things to normalcy and get the account back under your control with a new password. You can recover hacked Microsoft Accounts, Google Accounts, Facebook account, Twitter account, etc., using their properly laid down procedure.
Amount missing from your bank account
In the event of misfortune, you can lose all your money if a hacker gets access to your personal information (Credit Card, Online Banking details, etc.). To avoid this, turn on transaction alerts that send text alerts to you when something unusual is happening. Many financial institutions allow you to set thresholds on transaction amounts, and if the threshold is exceeded or it goes to a foreign country, you’ll be warned. It would be a good idea to follow these Online Banking Tips.
Fake antivirus messages
Fake antivirus warning messages are among the surest signs that your system has been compromised. Clicking No or Cancel to stop the fake virus scan yields no benefit since the damage is already done. These programs, often make use of unpatched software like the Java Runtime Environment to exploit your system. One such common message is – Your computer has been compromised or hacked!
Frequent random popups
This problem is mostly associated with your browsers and indicates you have unwanted software or malware installed on your computer since websites do not generally generate harmful pop-ups.
Redirected Internet searches or home page
It’s a well-known fact that most hackers make their living by redirecting your browser to an address other than the one you want to visit. That’s certainly because hackers get paid by getting your clicks to appear on someone else’s website, often those who don’t know that the clicks to their site are from malicious redirection.
You can often spot or pinpoint this type of malware by simply typing a few related, very common words into the search bar of popular search engines and checking to see whether the results relevant to your search appear or not. The traffic sent and returned will always be distinctly different on a compromised computer vs. an uncompromised computer.
Is your PC acting as a Botnet Node?
Botnets are networks of compromised computers, controlled by remote attackers to perform such illicit tasks as sending spam or attacking other computers. Maybe your computer has been compromised and is acting as a Node.
TIP: Before you proceed, you might want to read our post – Why would someone want to hack my computer?
Read: How to check if someone is remotely accessing your computer
What to do if your computer has been hacked?
1] If you feel that your Windows PC may have been hijacked, you should disconnect from the Internet and boot into Safe Mode and run a full deep scan of your antivirus software. If your security software has been disabled, use a good on-demand antivirus scanner. and run it from an external disk or USB.
2] You may also use specialized tools like Norton Power Eraser, an anti-hacker software, or one of these Botnet Removal Tools.
2] You can remove bogus toolbars from the browser using a good Browser Hijacker Removal software.
3] Open your Control Panel and uninstall programs that may look suspicious in nature.
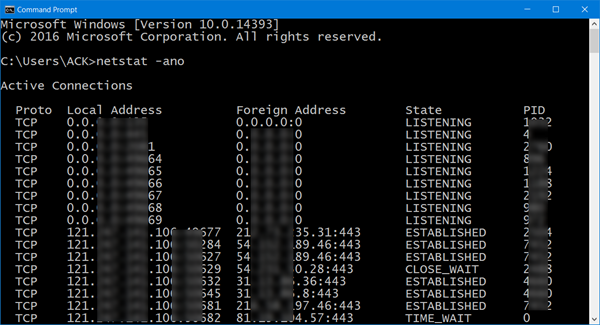
4] When you are connected to the Internet, open a Command Prompt, type the following command, and hit Enter:
netstat –ano
- -a parameter lists all the computer’s connections & listening ports
- -n parameter displays addresses & port numbers
- -o parameter outputs the process ID responsible for the connection.
An IT administrator can monitor your open Ports and the system’s network activity with a glance.
Check for any suspicious connection. Please note down that any connection that says – ‘Established’ and the PID number and ensure that all such connections are valid connections. If need be, press Ctrl+Shift+Esc to bring up the Task Manager. Then, navigate the mouse cursor to ‘Processes’ tab and hit the ‘View’ tab, select columns, and check the Process Identifier PID column. Instantly, the complete list of PID numbers will be displayed. Look for the number you noted down moments ago in the CMD window. If in doubt, terminate the process.
5] Install a bandwidth monitoring tool so that you can keep an eye on your usage. Use Packet Sniffing Tools intercept and log network traffic.
Keep your operating system and installed software updated at all times so as to close all software vulnerabilities and use a good security software. It is essential to keep yourself aware of these developments since, in today’s threatscape, no antivirus software offers 100% peace of mind. To combat this, antimalware programs that monitor program behaviors – Heuristics – to catch previously unrecognized malware should be used. Other programs that use virtualized environments, VPNs, anti-hacker software, and network traffic detection software can also be deployed for use.
6] Make use of Detekt, a free anti-surveillance software for Windows.
Here are some tips that will help you keep Hackers out of your Windows computer.
If you need more help, please go through this Malware Removal Guide. You may also like to read this post titled, how do you tell if your computer has a virus.
Nice post! From time to time it is nice to see articles like this that teach us and/or remind us how to walk on the safe side of things.
Thanks!
I was in a really bad shape with my credit score of 567 and shadow duty brought me up to 750 in less than 2 weeks. please don’t get caught up with those scammers out there shadowdataduty@gmail.com he is real folks.
How about Mac?
im being hacked
:P
I got this email on my spam. Whats the possibility that I am hacked?
I represent a group of hackers called Anonymous Hacker Team
The other day we got access to your working and home pc and found on them information that could spoil your life and position in society.
If you do not want us to use it against you and send it out to all of your contacts in mail and friends on facebook.
Possibility is very low. It could be an empty threat mail. Change your online passwords, scan your computer with two different antivirus software and then forget about this issue. That is what I would have done.
So, I go to my administrative account on day and somehow my entire family is in my administrative account. I also notice they have asked me some odd questions about things they would not know that are in my account. Of course, when i confront them they blame me when it is them in my computer’s admin act, not the other way around. Can someone please explain to me exactly how they got into my computer’s admin account. They are all screaming at me that I am a hacker. I am a 66 year old disabled woman who has absolutely no idea how to hack into other people’s accounts and computers but they believe I do. I would very much appreciate any explanation of this situation as I am very weary of being yelled at and accused of doing things I did not do.