Securing Windows XP after Microsoft ends support in April 2014 is not going to be an easy job. In fact, it’s going to be nearly impossible! StatCounter says Windows XP market share is around 19% whereas NetApplication says it is around 29%. Both have their own methodology of calculating this. Given the ground realities where a bulk still uses Windows XP and considering the fact that there are many still many home users from various parts of the world, who just would not be able to afford to upgrade to a newer version of the Windows operating system, securing their computers is going to a big challenge!

Windows XP holds around 20% of the operating system market share. And this is the global figure. In Africa, Windows XP still commands a market share of around 33%. In Asia its 27%! In India it is around 30%, whereas in China it is 51%! That’s like literally hundreds of millions of computers still running Windows XP!
Microsoft wants this figure to come down to around 10% globally by the time it ends its support in April 2014. But, although the figure may (or may not) come down, the figures in developing countries will continue to be high. There will still be those users, in some countries, who will predominantly still be using this outdated operating system.
When Microsoft ends support for Windows XP, it will stop releasing security and other updates for it. It will even stop supporting Microsoft Security Essentials on Windows XP. And once Microsoft stops providing security patches and updates to Windows XP SP3 and Microsoft Security Essentials, it will become an open playground for hackers and malware pushers. It will effectively have a zero-day vulnerability in perpetuity! You can read more about the risks of staying with Windows XP after End Of Support.
Although Microsoft will stop supporting Windows XP, there will be many software companies who will continue to support it. Several security companies like have already announced their intentions to continue supporting their antivirus and security software for Windows XP. But it is indeed a question – how long would other software companies want to support a platform that is practical for all purposes, dead in the water. Of course one cannot discount the fact that in case of an outbreak, Microsoft might just be compelled to release some security updates under public pressure – but that’s another question.
Secure Windows XP after End Of Support
This post is meant to try and help those from such countries, where the usage of Windows XP would still be high and for those users who would be constrained to use it simply because they may not be able to afford to upgrade, by suggesting some steps they can take! It will attempt to list some steps which a Windows XP home user could take to minimize risks and mitigate their potential security problems.
1] Use third-party Internet Security Suite
Given the fact that Microsoft will stop supporting Microsoft Security Essentials its best, you switch to free security software. Recent news suggests that they will stop updating MSE & MRT after June 2015. A Firewall can block threats that your antivirus may miss. Not only that, but it can also prevent hackers from breaking into your computer! Since Microsoft will stop updating Windows XP components, its firewall too will remain unpatched. So it will be imperative that you install a good firewall too, apart from antivirus software. While you can always go in for some free AntiVirus software and free Firewall software, I’d recommend that you install a free, but fully integrated Internet Security Suite, which could offer multi-layered protection. There are many security companies that have committed themselves to support their security software on Windows XP beyond the end of life.
2] Take backups regularly religiously
Take backups regularly religiously! You have no option! Should something go wrong, you will have the option of going back. Use any of these free Imaging, Backup and Recovery Software which will work on Windows XP. What would happen if you needed to reinstall Windows XP on your computer? Would you be able to activate it? Would Microsoft’s activation servers for Windows XP activation still work? There are several such questions, which cannot be answered at the moment. So create an image of your Windows XP and maybe even back up the Activation Token files.
3] Keep your installed software up-to-date
A Software Update Checker will scan your computer for installed software. You will thus be protected from vulnerabilities in these software. Run their scans regularly.
4] Use an alternative web browser
Since Internet Explorer too will not get updates, it might be time to drop IE and move to an alternative browser like Firefox or Chrome.
5] Use alternative software instead of built-in software
Like for browsers, start using alternative media players, compression tools, Windows Explorer alternatives, email clients and such, since these components too will not be receiving updates. You can see a bunch of free Windows software here.
6] Never click on unknown links or download attachments from unknown sources
This is important! Email is a common vector used by malware to get on your computer. So never ever click on any link which you may think looks suspicious. Even if you have a 1% doubt – DON’T! The same holds true for attachments too. You can surely download attachments you are expecting from friends, relatives & associates, but be very careful of the mail forwards which you may receive even from your friends. A small rule to remember in such scenarios: If in doubt – DONT!
7] Make Windows XP show file-extension
It is also a good idea from a security point of view, to show file extensions. When you do this, the file names will always appear with their extensions like .doc, .pdf, .txt, etc. This will help you in seeing the real extensions of the files and thus make it a bit more difficult for malware to disguise itself and get on your computer.
8] Use an additional On-demand antivirus scanner
There may be times of doubt, where you might want a second opinion. At such times you may use these on-demand antivirus scanners. In fact, make it a practice to use it once a week at least.
9] Clear you Internet Cache frequently
Temporary Internet Files folder in Windows XP is a sure-shot breeding ground for malware downloaded from the Internet. Set your browser to clear the cache on every exit.
10] Take Windows XP offline
This could probably the best thing to do, ie if you can do it. Use Windows XP for all your offline work and don’t connect to the Internet. But yes, you will still have to take care when you plug in a friend’s USB or external drive!
11] Lockdown your Windows XP machine
Use a software like TimeFreeze, RollBack XP or Returnil System Safe, which returns your OS to a prior state every time you reboot.
12] Take care while connecting a USB
USB’s are a common vector for passing on malware. So avoid or be extra careful when connecting someone else’s USB drives. Disable AutoPlay for removable devices. Restrict access to USB drives if you can. Manage & secure your USB and USB Drives.
13] Use a Standard User Account
Don’t use the Administrator Account when using your Windows XP computer for working or browsing the Internet. Use a non-admin Standard User Account to do so. (Thanks for this one Ron).
14] Use DropMyRights
Windows XP users must now install the free DropMyRights program. This tool will lower a user’s privilege level and make surfing more secure. It will make browsing a little more secure, since it runs selected programs, like browsers, in a restricted environment, with lower rights, even when logged on to Windows XP as an Administrator. This tool is not needed on Windows Vista and later, but it can be very useful for Windows XP users – especially now.
15] Harden Windows XP security by tweaking it
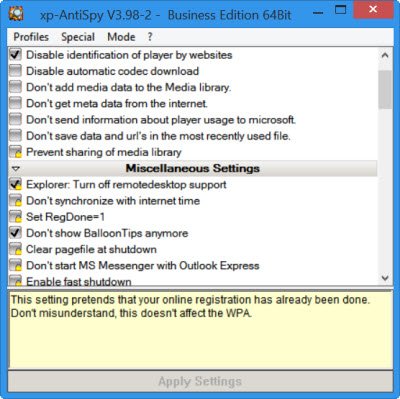
XP-AntiSpy is a little utility that lets you disable some built-in features and harden Windows XP security. XPY is another such tool Do check them out and use one of them to disable features like Remote Desktop, etc, easily.
16] Block bad websites
If you plan to continue using Internet Explorer, add bad sites to the Internet Explorer Restricted Site Zone. You can use ZonedOut to manage it and add a list of ‘bad’ sites from SpywareWarrior. You can also use SpywareBlaster’s innoculate feature to achieve the same. You can also add a list of bad websites to your Hosts File and block them. The list of bad websites from mvps.org is worth considering, and you can use HostsMan to manage your Hosts File. If you block bad websites, the chances of your Windows XP getting infected with malware are further reduced.
17] Change DNS Server
Change your DNS Settings. Use OpenDNS or something similar to prevent your computer from visiting bad malicious websites.
Enterprise users of Windows XP would do well to consider a migration to a recent Windows version, if possible. If you have an option, and can, then use Windows Server 2003 R2 instead of Windows XP. Windows Server 2003 R2 is basically Windows XP Server since they are both based on the same kernel. So whatever works on Windows XP only, will also work on Windows Server 2003 R2. While Windows XP end of support happens in April 2014, for Windows Server 2003 R2, the date is July 2015. So that still gives you some more breathing space. Running Windows XP in a Virtual Machine is also an option that may work and make sense, while support is still available for Windows Server 2003. Windows XP Enterprise customers, through the Microsoft Premium Support Services will also be eligible to get security hotfixes and direct technical support throughout the life of their contract.
Taking all these steps will not secure your Windows XP – no way! Don’t get a false sense of security! But its the best one can do under the situation. I would strongly urge you to upgrade to Windows 10 – and if that is not possible, move over to some free open-source operating system. Do also read our post on Windows XP End of Life recommendations – What next!?
Let me know if you have any more ideas about how to secure Windows in general.