DNS stands for Domain Name System, and this helps a browser in figuring out the IP address of a website so that it can load it on your computer. DNS cache is a file on your or your ISP’s computer that contains a list of IP addresses of regularly used websites. This article explains what is DNS cache poisoning and DNS spoofing.

DNS Cache Poisoning
Every time a user types a website URL in his or her browser, the browser contacts a local file (DNS Cache) to see if there is an entry to resolve the IP address of the website. The browser needs the IP address of the websites so that it can connect to the website. It cannot simply use the URL to directly connect to the website. It has to be resolved into a proper IPv4 or IPv6 IP address. If the record is there, the web browser will use it; else it will go to a DNS server to get the IP address. This is called DNS lookup.
A DNS cache is created on your computer or your ISP’s DNS server computer so that the amount of time spent in querying the DNS of a URL is reduced. Basically, DNS caches are small files that contain the IP address of different websites that are frequently used on a computer or network. Before contacting DNS servers, computers on a network contact the local server to see if there is an entry in the DNS cache. If there is one, the computers will use it; else the server will contact a DNS server and fetch the IP address. Then it will update the local DNS cache with the latest IP address for the website.
Each entry in a DNS cache has a time limit set, depending upon operating systems and the accuracy of DNS resolutions. After the period expires, the computer or server containing the DNS cache will contact the DNS server and update the entry so that the information is correct.
However, there are people who can poison the DNS cache for criminal activity.
Poisoning the cache means changing the real values of URLs. For example, cybercriminals can create a website that looks like say, xyz.com and enter its DNS record in your DNS cache. Thus, when you type xyz.com in the address bar of the browser, the latter will pick up the IP address of the fake website and take you there, instead of the real website. This is called Pharming. Using this method, cybercriminals can phish out your login credentials and other information such as card details, social security numbers, phone numbers, and more for identity theft. DNS poisoning is also done to inject malware into your computer or network. Once you land on a fake website using a poisoned DNS cache, the criminals can do anything they want.
Sometimes, instead of the local cache, criminals can also set up fake DNS servers so that when queried, they can give out fake IP addresses. This is high-level DNS poisoning and corrupts most of the DNS caches in a particular area thereby affecting many more users.
Read about: Comodo Secure DNS | OpenDNS | Google Public DNS | Yandex Secure DNS | Angel DNS.
DNS Cache Spoofing
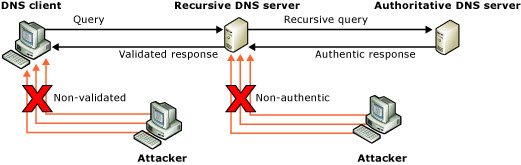
DNS spoofing is a type of attack that involves impersonation of DNS server responses in order to introduce false information. In a spoofing attack, a malicious user attempts to guess that a DNS client or server has sent a DNS query and is waiting for a DNS response. A successful spoofing attack will insert a fake DNS response into the DNS server’s cache, a process known as cache poisoning. A spoofed DNS server has no way of verifying that DNS data is authentic, and will reply from its cache using the fake information.
DNS Cache Spoofing sounds similar to DNS Cache Poisoning, but there is a small difference. DNS Cache Spoofing is a set of methods used to poison a DNS cache. This could be a forced entry to a computer network’s server to modify and manipulate the DNS cache. This could be setting up a fake DNS server so that fake responses are sent out when queried. There are many ways to poison a DNS cache, and one of the common ways is DNS Cache Spoofing.
Read: How to find out if your computer’s DNS settings have been compromised using ipconfig.
DNS Cache Poisoning – Prevention
There are not many methods available to prevent DNS Cache poisoning. The best method is to scale up your security systems so that no attacker can compromise your network and manipulate the local DNS cache. Use a good firewall that can detect DNS cache poisoning attacks. Clearing the DNS cache frequently is also an option some of you may consider.
Other than scaling up security systems, admins should update their firmware and software to keep the security systems current. Operating systems should be patched with the latest updates. There should not be any third-party outgoing link. The server should be the only interface between the network and the Internet and should be behind a good firewall.
The trust relations of servers in the network should be moved up higher so that they do not ask just any server for DNS resolutions. That way, only the servers with genuine certificates would be able to communicate with the network server while resolving DNS servers.
The period of each entry in the DNS cache should be short so that DNS records are fetched more frequently and are updated. This may mean longer time periods of connecting to websites (at times) but will reduce the chances of using a poisoned cache.
DNS Cache Locking should be configured to 90% or greater on your Windows system. Cache locking in Windows Server allows you to control whether or not information in the DNS cache can be overwritten. See TechNet for more on this.
Use the DNS Socket Pool as it enables a DNS server to use source port randomization when issuing DNS queries. This provides enhanced security against cache poisoning attacks, says TechNet.
Domain Name System Security Extensions (DNSSEC) is a suite of extensions for Windows Server that add security to the DNS protocol. You can read more about this here.
There are two tools that may interest you: F-Secure Router Checker will check for DNS hijacking, and WhiteHat Security Tool monitors DNS hijackings.
What is DNS Spoofing and DNS Hijacking?
DNS Spoofing and DNS Hijacking are two different terms. DNS Spoofing is the method used to poison the DNS cache. In DNS Spoofing, hackers try to insert a fake DNS response into the DNS server cache. Hackers use DNS Spoofing to redirect users to fake malicious websites in order to gain sensitive information, like credit card details. DNS Hijacking is an attempt to take control of the DNS Server of the client.
What is an example of DNS Spoofing?
Suppose you are visiting your bank’s website. The attacker could change the IP Address of the targeted website causing you to redirect to the fake website. This fake website is created by the hacker and it looks identical to the original website. Now, when you enter your banking details on that website, that information will be visible to the hacker.
Now read: What is DNS Hijacking?
Observation and comments are welcome.