Domain Name System or the DNS system is an Internet service that converts domain names into numerical Internet protocol (IP) addresses. These numerical IP addresses are used by computers to connect with each other.
When you type a domain name in the address bar of your browser, your computer contacts DNS servers. It then finds out the IP address for that website. Once this is done, your computer then uses this IP address to connect to the website.
DNSChanger
The German Federal Office for Information Security has recently advised computer users to check in the DNS server settings on their computers or home networks had been hijacked. This comes as a follow-up to the successful botnet takedown led by the FBI. The Ghost-Klick DNSChanger botnet had infested around 4 million computers in more than 100 countries. This Trojan redirected requests of infected computers to malicious websites by altering the address of the DNS server, reports the blog.eset.com.
For example, in such a case you may type www.thewindowsclub.com and want to visit this site, but you might suddenly find yourself landing on some other site instead! This is because of DNS Cache Poisoning and Spoofing.
While all the malicious DNS servers were replaced with correctly operating systems during the takedown, it might be a good time as any, to see if your PC has indeed been compromised.
To do so you can visit grc.com. On this website, you can check whether the DNS Settings of your home network or your computer have been changed or manipulated. You can check here if your computer is compromised by this malware that changes DNS settings on your computer or your home network. If you believe that you have been victimized you can also check and report your IP here to the FBI.
The botnet altered the DNS settings of computer users and pointed them to malicious sites. The malicious DNS servers would give fake, malicious answers, alter user searches, and promote fake and dangerous products. Because every web search starts with DNS, the malware showed users an altered version of the Internet. This scam netted the hackers over $14 million, according to the FBI.
How to find out if your computer is infected by DNSChanger
If you want to find out if your DNS settings have been compromised, you can do so as follows:
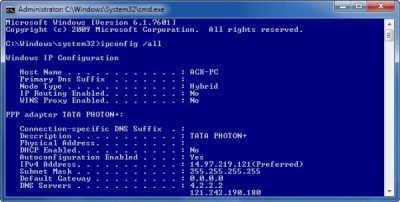
Open CMD and in the prompt windows type ipconfig /all and hit Enter.
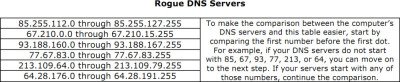
Now look for entries starting “DNS Servers…” This shows the IP addresses for your DNS servers in the format ddd.ddd.ddd.ddd, where ddd is a digit between 0 and 225. Make a note of the IP addresses for the DNS servers. Check them against the numbers mentioned in the following table containing known rogue IP addresses. If it is present, then your computer is using rogue DNS.
If your computer is configured to use one or more of the rogue DNS servers, it may be infected with DNSChanger malware. It might then be a good idea to back up your files and run a full scan on your Windows computer with your antivirus software.
DNSChanger Removal Tool
You can use the DNSChanger Removal Tool to fix this problem.
Incidentally, if your computer is still infected with the rogue DNS, you will not be able to surf the Internet after 9th July 2012. This is because these replacement DNS servers will be shut down on that day.
How do I know if my DNS has been changed?
To know if your DNS setting has been changed or not, you have two options. First, you can use the Command Prompt to run the ipconfig /all command. Second, you can open the Network Connections panel to check if the DNS setting has been changed on your computer or not.
How do I find my DNS for rogue?
To find if rough DNSChanger has changed your DNS settings or not, you can follow the aforementioned steps. As said, there are two ways to know about it. If you want to check only, you can use the ipconfig /all command in the Command Prompt or the Windows Terminal to get things done.
Take a look at the F-Secure Router Checker – It checks for DNS Hijacking.
These links may also interest you: