The Windows Registry is a directory that stores settings and options for the operating system for Microsoft Windows. It contains information and settings for all the hardware, operating system software, most non-operating system software, users, preferences of the PC, etc. This post talks about Windows Registry Basics.

Whenever a user makes changes to Control Panel settings, file associations, system policies, or most installed software, the changes are reflected and stored in the registry. The registry also provides a window into the operation of the kernel, exposing runtime information such as performance counters and currently active hardware.
The Windows registry was introduced to tidy up the profusion of per-program INI files that had previously been used to store configuration settings for Windows programs. These files tended to be scattered all over the system, which made them difficult to track.
Read: When do changes to the Registry get saved?
Windows Registry Basics explained
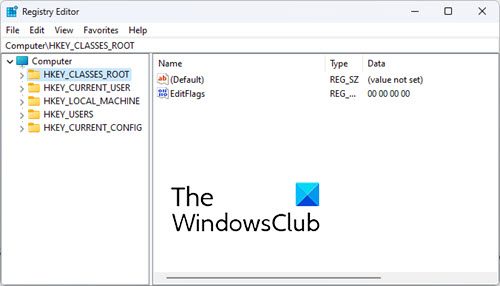
The Registry consists of the following 5 Root Keys:
- HKEY_CLASSES_ROOT
- HKEY_CURRENT_USER
- HKEY_LOCAL_MACHINE
- HKEY_USERS
- HKEY_CURRENT_CONFIG.
Root Keys contain SubKeys. Subkeys may contain subkeys of their own too and contain at least one value, called as its Default Value. A key with all its subkeys and values is called as a Hive.
The Registry is located on the Disk in the system32/config folder as several separate Hive files. These Hive files are then read into memory every time Windows starts or when the User logs on. To see where the Hives are physically stored, see:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\HiveList
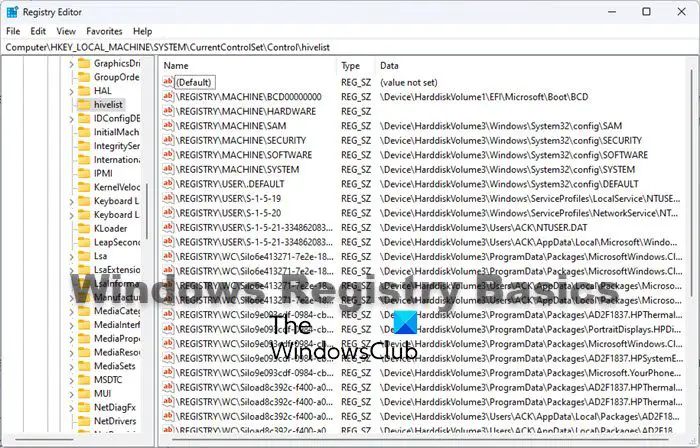
You can read more about the location of Windows Registry files.
The Registry uses the following data types:
- REG_SZ : The SZ indicates a zero-terminated string. This is a variable-length string that can contain Unicode as well as ANSI characters.
- REG_BINARY : It contains binary data. 0’s & 1’s.
- REG_DWORD : This data type is a Double Word. It is a 32-bit numeric value and can hold any number from 0 to 232.
- REG_QWORD : This data type is a Quadruple Word. It is a 64-bit numeric value.
- REG_MULTI_SZ : This data type contains a group of zero-terminated strings assigned to a single value.
- REG_EXPAND_SZ : This data type is a zero-terminated string containing an unexpanded reference to an environment variable, like say, %SystemRoot%.
Registry Virtualization in Windows
Starting with Windows Vista, along with File Virtualization, the Registry too, has been Virtualized, and hence unlike Windows XP, does not tend to suffer from bloat. The same has been continued in Windows 7.
In Windows Vista and later, the UAC utilizes the Registry Virtualization Feature, to redirect attempts to write to subkeys of
HKEY_LOCAL_MACHINE\Software
When an application attempts to write to this hive, Windows instead, writes it, to a per-user location,
HKEY_CLASSES_ROOT\VirtualStore\Machine\Software
This is done discreetly. No one gets to know that this is happening!
This is, in short, Registry Virtualization, and it is a useful Security feature.
Incidentally, mention must also be made of another new technology underlying Windows Vista and later: The Kernel Transaction Manager, which enables the Transactional Registry. This feature enables a sort of a Registry rollback. But it’s not implemented in Registry Editor. Instead, this feature is designed for use by developers who need to create robust applications using transactional processing.
Read: How to create a Registry Key in Windows.
Registry Editor
The primary tool in Windows 11/10 for working directly with the registry is Registry Editor. To access it, simply type regedit in Vista’s Start Menu Search Bar and hit Enter!
You have to be doubly careful when working with the Registry, as there is no confirmation prompt or a click OK to save prompt. Changes made are directly incorporated.
You can read more about Windows Registry Editor Tips & Features. Users can now use the Address Bar to jump directly to any registry key.
Mention must specifically be made of the
HKEY_LOCAL_MACHINE\System\CurrentControlSet
hive, as the keys in this particular location, are so essential for Windows to start, that its backup is maintained, which you can restore when necessary, simply by booting in Safe Mode and selecting Last Known Good Configuration in earlier Windows versions.
You might want to read these posts too:
Hi … I’m also puzzled about the registry and have never understood how to maintain it or keep it from corrupting my system somehow.
I’ve recently had a very frustrating email exchange with Mihal Roman from Spamfighter. Besides being extremely arrogant and unhelpful, he basically said it was my fault for expecting too much from the software (and then he refused to provide a refund). Firstly he told me that they have no intention of fixing the bugs and various flaws in the antispam software, saying that this is how the software is intended to work and there’s no need to improve it or release any bug-fixes in the future. It’s good enough, he claimed. (I was complaining about spam emails that weren’t being blocked, despite my marking them as spam and adding their addresses and domains to the black list). He then said it’s perfectly OK for the Spamfighter software to use the registry to store and maintain the black and white lists.
Is that right?
It means that every time I receive email (and I get around 1,000 emails a day), Spamfighter is writing to the registry. And so far there are about 20,000 entries for all the black-listed emails that I’ve already imported.
Isn’t there a risk of corrupting the registry (particularly if there are outstanding bugs and security holes in the software that aren’t being maintained)? I would have thought that the registry needs to be backed up before any major changes (like installing new software). But if the registry is being used as a private database file for an application then almost anything could cause a serious system crash – maybe something as little as a power failure in the middle of receiving emails and/or marking an email as spam or not-spam.
Should I be worried? Should I uninstall Spamfighter?
While I have not used SpamFighter, it is among the better known anti-spam software available. Although I cannot say for sure, I guess they must be checking emaild IDs for sapm against their data bank from their servers or from those stored locally on your computer. And I am sure that like many other software, SpamFighter too must be creating entries in your Registry – and this is not necessarily bad.
To maintain your Registry, I would suggest you run a good freeware registry cleaner like say, CCleaner, once every month.
I think you could trust SpamFighter.
Thanks Anand, but I’m still a bit worried when you say “I have not used spamfighter” and creating entries in the registry “is not necessarily bad”.
I find spamfighter to be quite a sloppy piece of software, now that I have been using it for about a month. I’m getting the same obviously spam emails in my inbox consistently, despite marking it as spam, adding the domain to the blacklist, etc.
But when I see that several hundred entries are added to the registry every day, I can’t see how this can be safe.
What about a power failure? If spamfighter is more or less writing to the registry throughout the day, it could happen that a power failure causes the operation to be interrupted and possibly corrupting the registry.
Does it matter?
If the registry write gets interrupted, say, and the registry file becomes severely corrupted, will Windows still continue to restart and function? And are the corrupted entries easily fixable with CCleaner?
Or should I back up the registry several times a day in case I need to go back to a previous “whole” version of the registry in case of a system failure caused by spamfighter.
I tried to get a response from spamfighter technical support, but they consistently ignored my questions about the registry and the various bugs I discovered, except that I did get a couple of responses saying that this is how spamfighter is supposed to work and I’ve just got to accept the bugs and the false positives and negatives because it’s not gonna change.
After getting these either completely disinterested or smartalec responses, I got worried about how reliable and safe their software really is. It would cost them relatively little to fix the problems, but they just don’t want to. When a company starts to behave rudely and arrogantly towards its customers, then it’s time to move on… probably a sign that there’s serious internal conflicts and the business is about to fold… which also means the many customers will have purchased a half-finished product that quickly becomes obsolete. It seems that the subscription-based model is to pay for the running of their servers to keep track of spam email IDs as you suggest. What happens when these servers get switched off?
If you think it Is a “a sloppy piece of software” and are not comfortable using it, then it better to uninstall it. At least I would uninstall any software right away if I did not find any value in using it.
CCleaner or for that matter any registry cleaner, will help in removing broken or orphaned registry entries only, and not fix a corrupted Registry.
I’m curious about something here.. Can anyone tell me when MS first introduced the “REG_EXPAND_SZ” registry entry type?
I’m checking for potential compatibility issues with referencing other environment variables within the %PATH% variable itself. Been searching high and low for this, but I have yet to find a definitive answer.
It’s been around a long time.
A common problem I’ve seen is that environment variables stop expanding if the Path string is saved as a REG_SZ type versus the REG_EXPAND_SZ type it’s supposed to be.
This is probably not helpful to you years later, but for the benefit of others:
Not all software uses the Registry in a responsible manner. This does not automatically imply corruption, but it does imply bloat. The Registry really isn’t designed to be used to support tens of thousands of data entries for a particular piece of software. A better implementation would be to have a single entry that points to a private file that stores this information. It can and is used in this manner, but it shouldn’t be: it’s sloppy programing.
Registry corruption tends to happen when data in the Registry that references other parts of the Registry gets broken. For example, a class is defined, but other data supporting that class is removed. This is logical corruption. Physical damage to hive files can also corrupt data, but neither is usually catastrophic.
Most every Windows installation will have some degree of logical Registry corruption, but most of the time it goes unnoticed. The Registry is really closer to a simple file system, than a database as some people try to describe it. The same ills that can happen to file systems can happen to the Registry, too.
hallo Anand,
i would like to save as powrpoint files in .pptx by default. can you please suggest me what should i do?
thanks