In Windows 7 and Windows Vista, if a program does not have elevated permissions to write to C:\Program Files or C:\Windows folder, Windows lets the program think it is writing there. However, it redirects the action to a Virtual Store under the AppData store in your User folder. Usually, INI files, data files, templates are redirected in such a manner. In this post, I will explain about File Virtualization and Compatibility Files toolbar button in Windows 7.
File Virtualization in Windows 7
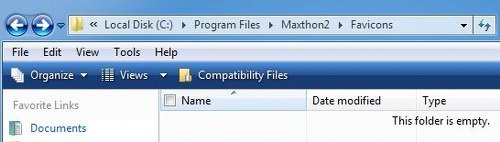
To take an example, I use the Maxthon browser. Its favicons are meant to be stored in the following location:
C:\Program Files\Maxthon2\Favicons
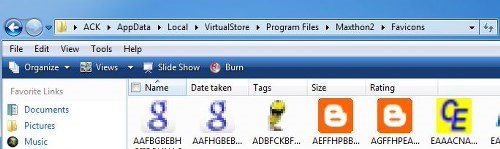
However, they get stored in the following folder:
C:\Users\Username\AppData\Local\VirtualStore\Program Files\Maxthon2\Favicons
Compatibility Files toolbar button
So if you open the first folder, you will see it as empty. But if you click on the Compatibility Files tab, immediately the latter folder is opened, and you see all the favicons there.
It is called File Virtualization.
It is one of the security features that are not evident in Windows. The feature provides an application, a virtual store where it can read and write without compromising the system. For instance, if you have an app that tries to write to System32, then, Windows creates a virtual System32 in the user’s profile that the application can use.
Internet Explorer running in Protected Mode makes use of this functionality. It places a file in the virtual startup folder when you visit a web page rather than the actual Startup folder so that it does not execute upon the next boot.
It makes it possible to run applications as a standard user, even when the applications require Administrator rights. In short, Windows redirects, such application writes from specified secured areas to the virtual store under the user’s profile. It is something similar to Registry Virtualization.
dfsdfdsf
dfsddsfd
dfsfdssdf
dsffddsf
dfsfdsf
dsffdsdf
dsffddfd
dfsdfsdffds
dsffdfds
sdfdsdfsdf
fgfdgf
dfssdfdfs
dfsdfdfdsf
dsfdd
dfsdsfd
fdsdfdsff
dfsdffdsfds
dfsfsdfds
dsffsfddf
rererwewew
gdfdsffds
sfdsdffd
sddfdsf
sffsdds
dfsfsdfsdfds
dsfffdsfsd
fdsfsdffsd
sdfsdffdfsd
dfssfdff
sfdsdffds
sfdfdfsd
dfsfdfds
sdffsdfd
ggfgdf
fgfdgfdfd
fdgffd
dgfdfdgd
dggdff
fdggdfgd
weawewqwe
qwqe
qeqwewq
wqwweq
wqeqewwq
qqwewq
qwewwe
weqwewwq
wqewqw
wqwweewew
gfgfgfdg
gdgdgfd
gfggfggf
sdfsdffdsfsd
fdsfsdfdsfds
dfssdffdfds
dfsfdfddsf
sdfererewerw
ersrsrffds
fdsfdfdsfds
hgfgdf
dgdfgfd
dfggfgfd
gfdsdffds
dfssdfdfs
sdfdsfdds
fsddsdsf
fdsfdsddsf
fdsdfsdsdf
sdfdfddsf
dsfdfdfds
fdsffsddfs
dfsdffdsdsf
fgfdggf
sdfdsddsf
dfssdfdfsd
dsfdfsfdsd
dsfdffsddsf
dsffdsdffds
sddfsfsdfsd
sdfdsdfdsdf
sfdsdfdsdsfd
dsfdsdfsdf
vxvccvxvccv
vcxvcxvvcx
vcxcvcxvx
vvcxvvc
vxcvcvxvc
cvxvcxvcvcx
vcxvvccvx
xcvvcvxcvxc
vxcvxcvcx
vxcxvcvxcv
cvxvcvcxvcvcx
vxccvcvxcvcx
cvxvcxvc
ffdddfdfsfd
cxxcy
cxyxccyx
cxxycxxy
ycxcxcx
cxcxcxy
xxy<xxyxy<yx<
xycxcxycxxc
dcdsadss
dsdasdssda
dasdsadsdsa
dadsddsadas
dsadsdsa
dsasdadsds
ssdasdds
saddsadsasd
dasdasdas
sddddads
asdddsda
dassasd
sadssadasd
sdasdadsa
asddsaasd
dassaddsasd
asdsdasdasda
asddsads
dassdasd
dsasdasad
dsaasdsad
dasdsadsa
sdasaddas
dasdssad
xyxyx
ccxcy
yxccx
adsasdsadsa
dassddas
sfddsdfd
dsfdfsds
dfsfsdsd
dsdfsdsdfs
dsdfssfd
sdfdfsdsdf
fsdsdfdsdf
dsdfsdfdsf
sdfsfdfssdf
fdssdfsdffds
cyxycxy
cssdasdas
dassadsad
sadasdassad
sdaasdsdads
sadassadsad
asdsadsadsa
sdasdaasd
sdasaddsa
dsadsasda
asdsadsda
gdgdggf
gfdggfd
yxccxyx
dsdadsdsa
xyxxcxcyy
yxccyxcxcxy
xxycxcxcx
cxycxyxccxcx
vbnbnvnbvb
sxyyccxcxy
hhfhghg
hfh
hhghghg
hfghhgf
hgfghgh
fhggfgfh
hfhghg
hhgghgf
jjhhjjh
zuztuzt
kjhkhjkkj
jkhhkjkhhj
khhkjkjk
jkhhjkj
kjkhjkjh
ghghfhg
hggfhgfg
ghhfh
hgfghf
kjhjkkjk
ghfggfg
gfhggf
nbnbnbv
vbbnbvvb
ghjhjjhgjh
zuuzztu
hjhhgjhjgj
uttzuztt
utzuztu
uiuziizuiuzi
zttuuztut
jghfhffh
kjhjhhjggjh
ztzzttrrz
jhgjhjgjhgjgh
retrtretre
dasdsadsdas
yxxyxxyxy
adsaddasdsds
ddasdsadsadsa
dsadsadsdas
eewqeqqw
dfdf
dfsdfds
dfsdfsdfds
dfsfdsdsf
fdsdfsdfs
sdasdasda
dfasafs
sdadsadsa
gfgfgfgf
trtrtrrt
ztzzr
uzuuzuz
uzzutzu
uutzuzuz
zutuzz
uztzuz
zuuztut
mnbmnnbm
jjhjghjhjhg
ghjjhgjhg
vyxccccxcyyc
cycxx
ccyxxyx
cvcvcvcvc
cxcyc
xy<<xy<xxy<
yxycx
bvbbbvb
vccvxc
vcyvcvcy
ffdfdsfdfd
hgfhf
ztrztztrr
uuzztut
dsasaddsa
fdffds
dsdasda
zzrzr
iiuizuizui
ziuziuiuz
qeqewew
rerewre
tretet
uztzut
iuiuziiu
uttuztuu
werrwererew
dsaddsdsa
gdgggd
hgfhgfhf
zuutuzuzt
iuuiizuizu
iuziuiuiuzighjhg
fsdfsdsdfd
gfdggf
gfdg
tetter
wwerewwe
izuiuiuz
opoiuooioiu
uziuuizuziiz
tzuztz
mbnmnbmnbmnb
bvnbvbvb
cvbbvccb
fhfhgfhg
yxccycx
sasadsadsa
ewerrerwew
ssdaweqwqew
trtrwrerw
zttztztrztztr
poiopopo