If you are looking for a way to decrypt files encrypted by Ransomware then this complete list of Ransomware decrypt & removal tools will help you unlock files encrypted or locked by ransomware on your Windows computer. Ransomware threats are on the rise, and every other day we get to read about it – whether it is WannaCrypt, Petya or Locky ransomware. This class of malware seems to be the favorite now as it is very profitable – lock down users’ files and data and then demand money to unlock them.
While there are some basic steps one can take to prevent ransomware, including making use of some free anti-ransomware software, it can still happen that you end up being a victim of some ransomware.
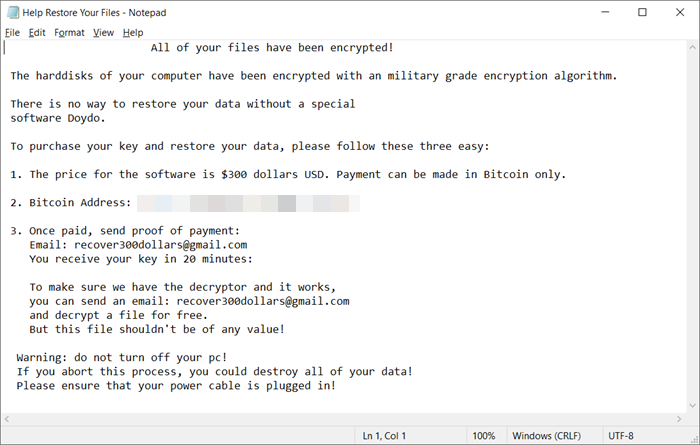
Well, what does one do after a Ransomware attack on your Windows computer?
Can you decrypt ransomware?
If a Ransomware Decryption Tool is available for the malware that has locked down your files then the chances are very high that you will be able to decrypt and recover your files. If no such tool is available, then the best bet would be to use your backup files. If you decide to pay then the private key that they give you is almost always known to work and help decrypt the files.
Ransomware Decryption Tools
First of all, identify the Ransomware which has infected your computer. For this, you may use a free online service called ID Ransomware
If you are able to identify the ransomware, check if a ransomware decrypt tool is available for your type of ransomware. Currently, the following decryptor tools are available.
You may go through the entire list or press Ctrl+F and search for a specific ransomware name.
Before you use these tools, use any good antivirus software or ransomware removal tool to remove the ransomware. Only then should you use these ransomware file decryptor tools. However, if you have moved your encrypted files to another isolated secure system, you directly use these tools.
1] Decrypter for HydraCrypt and UmbreCrypt Ransomware: HydraCrypt and UmbreCrypt are the two new Ransomware variants from the CrypBoss Ransomware family. Once successful in breaching your PC security, HydraCrypt and UmbreCrypt can lock your computer and deny access to your own files.
2] CryptoLocker Decryption Tool : This free Decryptlocker or CryptoLocker Decryption online tool from FireEye and Fox-IT to decrypt the Cryptolocker encrypted files. UPDATE: The site appears to have been taken down.
3] Petya ransomware decrypt tool & password generator: PETYA ransomware is one of the most recent online threats for PC users. It is a malware which overwrites the MBR (Master Boot Record) of your PC and leaves it unbootable and also disallows restarting the PC in Safe Mode.
4] Operation Global III Ransomware Decryption Tool: This ransomware attacks your system and then displays a leaving the user with no choice but to pay the ransom amount. All your encrypted file extensions are changed to .EXE and are infected with malicious codes.
5] Unlock files locked by Decrypt Protect ransomware using this tool from Emsisoft.
6] Emsisoft has released several decryptor tools for ransomware. This list currently includes ransomware decryption tools for:
AutoLocky, Aurora, Nemucod, DMALocker2, HydraCrypt, UmbreCrypt, DMALocker, CrypBoss, Gomasom, LeChiffre, KeyBTC, Radamant, CryptInfinite, PClock, CryptoDefense, Harasom, Xorist, 777, BadBlock, DApocalypse, ApocalypseVM, Stampado, Fabiansomware, Philadelphia, FenixLocker, Al-Namrood, Globe, OzozaLocker, Globe2, NMoreira or XRatTeam or XPan, OpenToYou or OpenToDecrypt, GlobeImposter, MRCR, Globe3, Marlboro, OpenToYou, CryptON, Damage, Cry9, Cry128, Amnesia, Amnesia2, NemucodAES, BigBobRoss, PewCrypt, CryptoPokemon, ZQ Ransomware, MegaLocker, JSWorm 2.0, GetCrypt, Ims00rry, ZeroFks, JSWorm 4.0, WannaCryFake, Avest,Muhstik, HildaCrypt, STOP Djvu, Stop Puma, Paradise, Jigsaw, Hakbit, TurkStatik, ChernoLocker, Ransomwared, KokoKrypt, JavaLocker, RedRum, Zorab, SpartCrypt, CheckMail7, Crypt32, Cyborg, Ziggy, Avaddon, SynAck, Ragnatok.
You can get them all for free on their official website along with detailed usage guides.
7] Cisco also offers a free Decryption Tool for TeslaCrypt Ransomware Victims. This TeslaCrypt Decryption Tool is an open-source command-line utility for decrypting TeslaCrypt ransomware encrypted files so users’ files can be returned to their original state. Read more on it here.
8] Cisco Talos has released PyLocky ransomware decryptor tool. This decryptor is intended to decrypt the files for those victims affected by the ransomware PyLocky.
9] TeslaCrack is available on GitHub. It will help you decrypt files that were encrypted with the latest version of the TeslaCrypt ransomware.
10] Trend Micro AntiRansomware Tool will help you take back ownership of your computer by removing the ransomware on infected computers. To use this tool, enter Safe Mode with Networking. Download the Anti-Ransomware software and save it to your desktop. Next double-click on it to install it. Once it has been installed, restart your computer and go to the normal mode where the screen is locked by the ransomware. Now trigger the Anti-Ransomware software by pressing the following keys: Left CTRL+ALT+T+I. Run the Scan, Clean and then Reboot your computer. This tool is useful in cases of ICE Ransomware infections.
11] Trend Micro Ransomware Screen Unlocker Tool will give you access to a ransomware blocked computer.
12] Trend Micro Ransomware File Decryptor tool will attempt to decrypt files encrypted by certain Ransomware families like CryptXXX, Crysis, DemoTool, DXXD, TeslaCrypt, SNSLocker, AutoLocky, BadBlock, 777, XORIST, Teamxrat/Xpan, XORBAT, CERBER, Stampado, Nemucod, Chimera, LECHIFFRE, MirCop, Jigsaw, Globe/Purge, V2:, V3:, etc.
13] HitmanPro.Kickstart is a free Ransomware Removal Tool that will help you rescue a ransomed PC. It lets you start your computer from a USB flash drive to remove malware that has ransomed or locked your computer and does not allow you to access it.
14] Shade Ransomware Decryption Tool will help decrypt files with the following extensions: .xtbl, .ytbl, .breaking_bad, .heisenberg. Go get it from McAfee Intel.
15] McAfee Ransomware Recover is a tool and a platform that not only unlock user files, applications, databases, and other encrypted files but is also available for the security community.
16] AVG has also released ransomware decrypt tools for the following ransomware:
Apocalypse, Bart ransomware, BadBlock, Crypt888, Legion, SZFLocker, TeslaCrypt.
Go get them all here.
17] Check Point has released a Cerber Ransomware Decryption Tool. It is an online tool where you have to upload a file. UPDATE: This Cerber Ransomware Decryption Tool has been rendered ineffective. Merry X-Mas Decryptor from CheckPoint can decrypt files encrypted by the Merry X-Mas ransomware. BarRax decryptor tool is designed to decrypt files encrypted by BarRax. Available at CheckPoint.
18] The decryption keys for the NoobCrypt ransomware have been posted on Twitter. Use these unlock keys ZdZ8EcvP95ki6NWR2j or lsakhBVLIKAHg if your computer gets infected.
19] Bitdefender has released the following ransomware decryption tools: Bart Ransomware Decryptor | Linux.Encoder.3 | Darkside Ransomware Decryption Tool | Linux.Encoder.1 | BTCWare | GandCrab Decryptor | Annabelle Decryptor. | LockerGoga ransomware – Download – Details at nomoreransom.org.
20] The CoinVault decryption tool decrypts files encrypted by Coinvault and Bitcryptor. ChimeraDecryptor tool is designed to decrypt files encrypted by Chimera. Get them all from NoMoreransome.org.
21] Vindows Ransomware Decryption Tool will help decrypt files locked by Vindows Locker. Download it here.
22] Download Decryptor from BleepingComputer to decrypt 8lock8 ransomware encrypted files.
23] Decryptor for Crypren ransomware encrypted files is available here.
24] Decryptor for Crypt38 ransomware encrypted files is available here.
25] Decryptor for CryptInfinite or DecryptorMax is available here.
26] For CryptoHost, you can use this password generator created by Michael Gillespie. The file is hosted on Dropbox.
27] Decryptor for my-Little-Ransomware is available on Github.
28] CERT-PL has released one for CryptoMix Decryptor
29] Popcorn Decryptor Tool is available here.
30] Avast has released decryption tools for the following ransomware:
AES_NI, Alcatraz Locker, Apocalypse, AtomSilo & LockFile, Babuk, BadBlock, Bart, BigBobRoss, BTCWare, Crypt888, CryptoMix, CrySiS, EncrypTile, FindZip, Fonix, GandCrab, Globe, HiddenTear, Jigsaw, LambdaLocker, Legion, NoobCrypt, Stampado, SZFLocker, TeslaCrypt, Troldesh, Shade, XData.
Free Decryptors for Tortilla variant of Babuk ransomware and Black Basta ransomware are available here on avast.com. Get them all here.
31] ESET Crysis Decryptor is a free decryption tool for Crysis ransomware victims. Download it from Eset. It will also remove Dharma ransomware. They have also released a Decryptor for CryCryptor ransomware which is available on Github.
32] Kaspersky WindowsUnlocker can be useful if the Ransomware totally blocks access to your computer or even restrict access to select important functions, as it can clean up a ransomware-infected Registry.
33] RannohDecryptor from Kaspersky will help decrypt files encrypted by the Rannoh, AutoIt, Fury, Crybola, Cryakl, CryptXXX, CryptXXX v.2, CryptXXX v.3, MarsJoke, Polyglot, Dharma ransomware. Download it from here.
34] Kaspersky has also released several other decryptor tools like Rector Decryptor, Rakhni Decryptor, Wildfire Decryptor, Scraper Decryptor, Shade Decryptor, Scatter Decryptor, Xoris Decryptor, etc – go get them here. They will decrypt files encrypted by Rakhni, Agent.iih, Aura, Autoit, Pletor, Rotor, Lamer, Lortok, Cryptokluchen, Democry, Bitman, TeslaCrypt, and other ransomware.
35] Kaspersky Ransomware Decryptor will automatically decrypt all files for CoinVault and Bitcryptor victims. Get it here. It also helps in the case of Cryakl ransomware.
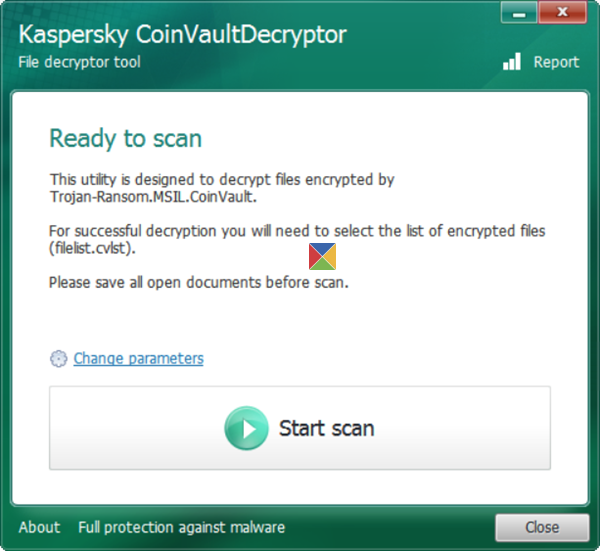
36] Visit the Kaspersky NoRansom web page to find out if they have released a decryption tool for your ransomware. Currently, the page shows the availability of WildfireDecryptor tool, ShadeDecryptor tool, RakhniDecryptor, RannohDecryptor tool and CoinVaultDecryptor tool. Also included are manual how-tos and other useful resources about ransomware. Intel McAfee has also made a Wildfire Decryptor.
RakhniDecryptor will help decrypt files encrypted by Dharma, Crysis, Chimera, Rakhni, Agent.iih, Aura, Autoit, Pletor, Rotor, Lamer, Lortok, Cryptokluchen, Democry, Bitman (TeslaCrypt) version 3 and 4 ransomware.
37] Malwarebytes has released a Telecrypt Ransomware Decrypter Tool to decrypt files infected with the Telecrypt Ransomware. Download it here.
38] Michael Gillespie, a ransomware researcher has released these ransomware decryptor tools:
Aurora Ransomware Decrypter, FilesLocker Ransomware Decrypter, InsaneCrypt Decryptor for desuCrypt Ransomware, GIBON Ransomware Decryptor, Striked Ransomware Decrypter, DCry Ransomware Decrypter, BitKangaroo Decrypter, BTCWare Ransomware Decrypter, Crypt38 Ransomware Decrypter, BitStak Ransomware Decrypter, Alpha Ransomware Decryptor, Unlock92 Ransomware Decrypter, Hidden Tear Ransomware Decrypter, Hidden Tear Brute Forcer Ransomware decryptor, PowerWare Locky Ransomware Decrypter, GhostCrypt Ransomware Decrypter, MicroCopy Ransomware Decryptor, Jigsaw Ransomware Decrypter, STOP Decrypter.
Plus he has also released the following useful tools:
- StupidDecryptor decrypts files encrypted by various screen-lockers that are fairly easy to decrypt
- RansomNoteCleaner can be used to scan a ransomware victim’s computer for leftover ransom notes and delete them
- CryptoSearch cleans up your computer of encrypted files and ransom notes from a ransomware infection.
39] Master Key for TeslaCrypt ransomware has been released. Tesladecrypt from Intel will decrypt TeslaCrypt encrypted files with the following extensions: .mp3, .micro, .xxx, and .ttt.
40] BTCWareDecrypter will decrypt files encrypted by BTCWare Ransomware. Get it here.
41] 360 Ransomware Decryption Tool can decrypt files locked by over 80 ransomware including GandCrab, Petya, Gryphon, GoldenEye and WannaCry ransomware.
42] Under favorable conditions, WannaKey and WanaKiwi, two WannaCrypt decryption tools can help decrypt WannaCrypt or WannaCry Ransomware encrypted files by retrieving the encryption key used by the ransomware.
43] Crysis Decrypting Tools have been developed by Eset as well as Avast.
44] The ransomware decryptor tool from QuickHeal will decrypt files locked by the following ransomware –
Troldesh Ransomware [.xtbl], Crysis Ransomware [.CrySiS], Cryptxxx Ransomware [.crypt], Ninja Ransomware [@aol.com$.777], Apocalypse Ransomware [.encrypted], Nemucod Ransomware [.crypted], ODC Ransomware [.odcodc], LeChiffre Ransomware [.LeChiffre], Globe1 Ransomware [.hnyear], Globe2 Ransomware [.blt], Globe3 Ransomware [.decrypt2017], DeriaLock Ransomware [.deria], Opentoyou Ransomware [[email protected]], Globe3 Ransomware [.globe & .happydayzz], Troldesh Ransomware [.dharma], Troldesh Ransomware [.wallet], Troldesh Ransomware [.onion], Satan DBGer Ransomware [.dbger]. STOP Djvu Ransomware, GandCrab Ransomware.
Download it here.
45] Ransomware Removal & Response Kit is not a tool, but a compilation of guides and various resources relating to dealing with ransomware, that can prove to be of help. It is a 500 MB download. Read more about it here.
46] Generally speaking, Anvi Rescue Disk can come to your rescue as it can help you uninstall & remove Ransomware.
How long does it take to decrypt ransomware?
This depends on the availability of the Ransomware Decryption Tool. It could range from a few days to a few weeks. If you decide to pay then the private key that they give you is almost always known to work and help decrypt the files right away.
Which tool is used for decrypting files?
For decrypting files, tools from Avast, Emsisoft and Trend Micro are highly effective. Emsisoft and Avast provide solutions for various ransomware, while Trend Micro focuses on restoring files encrypted by over 27 ransomware families. Always choose reputable decryption software to ensure data safety and recovery.
All the best!
If you have any more free ransomware decryptor tools to add, please do so in the comments section, linking to their official home or download page.
This post talks a little more about Ransomware Attacks & other FAQ.