A French security researcher Adrien Guinet has found a way to decrypt WannaCrypt Ransomware encrypted files by retrieving the encryption key used by the WannaCrypt ransomware. But currently, this tool has only been tested on and known to work under Windows XP only, but may work for Windows Vista, Windows 7 and Windows 8 as well. It will however not work on Windows 10.
Under favorable conditions, WannaKey and WanaKiwi, two decryption tools can help decrypt WannaCrypt or WannaCry Ransomware encrypted files by retrieving the encryption key used by the ransomware.
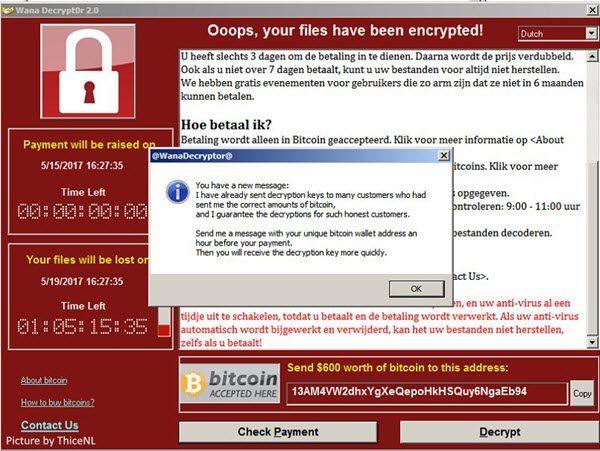
WannaCry Ransomware Decryptor Tool
WannaKey works by searching for the RSA private keys that are used by Wannarypt in the wcry.exe process. Wcry.exe is the process that generates the RSA private key. The main issue is that the ransomware does not erase the prime numbers from memory before freeing the associated memory.
However, there is a catch. This tool will work only if you have not rebooted the computer system after being infected and is the associated memory has not been allocated to some other process.
Says its author,
This is not really a mistake from the ransomware authors, as they properly use the Windows Crypto API. Indeed, for what I’ve tested, under Windows 10, CryptReleaseContext does clean up the memory (and so this recovery technique won’t work). It can work under Windows XP because, in this version, CryptReleaseContext does not do the cleanup.
You can use this tool to decrypt your files.
There is also another tool called WanaKiwi that is based on Adrien’s findings and it is available for download from Github.
WanaKiwi also recreates the .dky files expect from the ransomware by the attackers, which makes it compatible with the ransomware itself too. This also prevents the WannaCry to encrypt further files.
It has been tested on Windows XP, Windows XP as well as Windows 7 and you can read more about this here.
TIP: There are some free Vaccinator & Vulnerability Scanner Tools for WannaCry Ransomware available too.
