WannaCry Ransomware, also known by the names WannaCrypt, WanaCrypt0r or Wcrypt is a ransomware which targets Windows operating systems. Discovered on 12th May 2017, WannaCrypt was used in a large Cyber-attack and has since infected more than 230,000 Windows PCs in 150 countries. now.
What is WannaCry ransomware

WannaCrypt initial hits include UK’s National Health Service, the Spanish telecommunications firm Telefónica, and the logistics firm FedEx. Such was the scale of the ransomware campaign that it caused chaos across hospitals in the United Kingdom. Many of them had to be shut down triggering operations closure on short notice, while the staff were forced to use pen and paper for their work with systems being locked by Ransomware.
How does WannaCry ransomware get into your computer
As evident from its worldwide attacks, WannaCrypt first gains access to the computer system via an email attachment and thereafter can spread rapidly through LAN. The ransomware can encrypt your systems hard disk and attempts to exploit the SMB vulnerability to spread to random computers on the Internet via TCP port and between computers on the same network.
Who created WannaCry
There are no confirmed reports on who has created WannaCrypt although WanaCrypt0r 2.0 looks to be the 2nd attempt made by its authors. Its predecessor, Ransomware WeCry, was discovered back in February this year and demanded 0.1 Bitcoin for unlocking.
Currently, the attackers are reportedly using Microsoft Windows exploit Eternal Blue which was allegedly created by the NSA. These tools have been reportedly stolen and leaked by a group called Shadow Brokers.
How does WannaCry spread
This Ransomware spreads by using a vulnerability in implementations of Server Message Block (SMB) in Windows systems. This exploit is named as EternalBlue which was reportedly stolen and misused by a group called Shadow Brokers.
Interestingly, EternalBlue is a hacking weapon developed by NSA to gain access and command the computers running Microsoft Windows. It was specifically designed for the America’s military intelligence unit to get an access to the computers used by the terrorists.
WannaCrypt creates an entry vector in machines still unpatched even after the fix had become available. WannaCrypt targets all Windows versions that were not patched for MS-17-010, which Microsoft released in March 2017 for Windows Vista, Windows Server 2008, Windows 7, Windows Server 2008 R2, Windows 8.1, Windows RT 8.1, Windows Server 2012, Windows Server 2012 R2, Windows 10 and Windows Server 2016.
The common infection pattern includes:
- Arrival through social engineering emails designed to trick users to run the malware and activate the worm-spreading functionality with the SMB exploit. Reports say that the malware is being delivered in an infected Microsoft Word file that is sent in an email, disguised as a job offer, an invoice, or another relevant document.
- Infection through SMB exploit when an unpatched computer can be addressed in other infected machines
WannaCry is a Trojan dropper
Exhibiting properties that of a dropper Trojan, WannaCry, tries to connect the domain hxxp://www[.]iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea[.]com, using the API InternetOpenUrlA():
However, if the connection is successful, the threat does not infect the system further with ransomware or try to exploit other systems to spread; it simply stops execution. It’s only when the connection fails, the dropper proceeds to drop the ransomware and creates a service on the system.
Hence, blocking the domain with firewall either at ISP or enterprise network level will cause the ransomware to continue spreading and encrypting files.
This was exactly how a security researcher actually stopped the WannaCry Ransomware outbreak! This researcher feels that the goal of this domain check was for the ransomware to check whether it was being run in a Sandbox. However, another security researcher felt that the domain check is not proxy-aware.
When Executed, WannaCrypt creates the following registry keys:
- HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\\<random string> = “<malware working directory>\tasksche.exe”
- HKLM\SOFTWARE\WanaCrypt0r\\wd = “<malware working directory>”
It changes the wallpaper to a ransom message by modifying the following registry key:
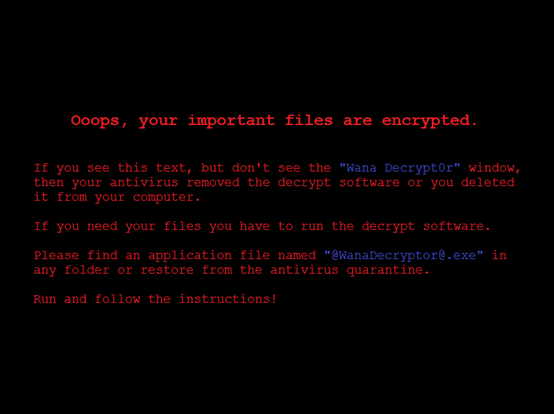
- HKCU\Control Panel\Desktop\Wallpaper: “<malware working directory>\@[email protected]”
The ransom asked against the decryption key starts with $300 Bitcoin which increases after every few hours.
File extensions infected by WannaCrypt
WannaCrypt searches the whole computer for any file with any of the following file name extensions: .123, .jpeg , .rb , .602 , .jpg , .rtf , .doc , .js , .sch , .3dm , .jsp , .sh , .3ds , .key , .sldm , .3g2 , .lay , .sldm , .3gp , .lay6 , .sldx , .7z , .ldf , .slk , .accdb , .m3u , .sln , .aes , .m4u , .snt , .ai , .max , .sql , .ARC , .mdb , .sqlite3 , .asc , .mdf , .sqlitedb , .asf , .mid , .stc , .asm , .mkv , .std , .asp , .mml , .sti , .avi , .mov , .stw , .backup , .mp3 , .suo , .bak , .mp4 , .svg , .bat , .mpeg , .swf , .bmp , .mpg , .sxc , .brd , .msg , .sxd , .bz2 , .myd , .sxi , .c , .myi , .sxm , .cgm , .nef , .sxw , .class , .odb , .tar , .cmd , .odg , .tbk , .cpp , .odp , .tgz , .crt , .ods , .tif , .cs , .odt , .tiff , .csr , .onetoc2 , .txt , .csv , .ost , .uop , .db , .otg , .uot , .dbf , .otp , .vb , .dch , .ots , .vbs , .der” , .ott , .vcd , .dif , .p12 , .vdi , .dip , .PAQ , .vmdk , .djvu , .pas , .vmx , .docb , .pdf , .vob , .docm , .pem , .vsd , .docx , .pfx , .vsdx , .dot , .php , .wav , .dotm , .pl , .wb2 , .dotx , .png , .wk1 , .dwg , .pot , .wks , .edb , .potm , .wma , .eml , .potx , .wmv , .fla , .ppam , .xlc , .flv , .pps , .xlm , .frm , .ppsm , .xls , .gif , .ppsx , .xlsb , .gpg , .ppt , .xlsm , .gz , .pptm , .xlsx , .h , .pptx , .xlt , .hwp , .ps1 , .xltm , .ibd , .psd , .xltx , .iso , .pst , .xlw , .jar , .rar , .zip , .java , .raw
It then renames them by appending “.WNCRY” to the file name
WannaCry has rapid spreading capability
The worm functionality in WannaCry allows it to infect unpatched Windows machines in the local network. At the same time, it also executes massive scanning on Internet IP addresses to find and infect other vulnerable PCs. This activity results in large SMB traffic data coming from the infected host, and can be easily tracked by SecOps personnel.
Once WannaCry successfully infects a vulnerable machine, it uses it to hop to infect other PCs. The cycle further continues, as the scanning routing discovers unpatched computers.
How to protect against WannaCry
- Microsoft recommends upgrading to Windows 10 as it equipped with latest features and proactive mitigations.
- Install the security update MS17-010 released by Microsoft. The company has also released security patches for unsupported Windows versions like Windows XP, Windows Server 2003, etc.
- Windows users are advised to be extremely wary of Phishing email and be very careful while opening the email attachments or clicking on web-links.
- Make backups and keep them securely
- Windows Defender Antivirus detects this threat as Ransom:Win32/WannaCrypt so enable and update and run Windows Defender Antivirus to detect this ransomware.
- Make use of some Anti-WannaCry Ransomware Tools.
- EternalBlue Vulnerability Checker is a free tool that checks if your Windows computer is vulnerable to EternalBlue exploit.
- Disable SMB1 with the steps documented at KB2696547.
- Consider adding a rule on your router or firewall to block incoming SMB traffic on port 445
- Enterprise users may use Device Guard to lock down devices and provide kernel-level virtualization-based security, allowing only trusted applications to run.
To know more on this topic read the Technet blog.
WannaCrypt may have been stopped for now, but you may expect a newer variant to strike more furiously, so stay safe and secure.
What is WannaCry, and how does it work?
WannaCry is a ransomware that targets Windows computers and locks down files until users pay the ransom. It was first discovered back in 2017, and it is still active. Like any other ransomware, it infects your PC and encrypts your files at once so that you do not gain access to any file.
How does the WannaCry ransomware attack work?
WannaCry ransomware mainly spreads through Server Message Block (SMB) in Windows systems. That said, any Windows computer is vulnerable to this ransomware until a certain precaution is taken. To learn more about the workflow of this ransomware, it is recommended to go through the entire article.
Microsoft Azure customers may want to read Microsoft’s advice on how to avert WannaCrypt Ransomware Threat.
UPDATE: WannaCry Ransomware Decryptors are available. Under favorable conditions, WannaKey and WanaKiwi, two decryption tools can help decrypt WannaCrypt or WannaCry Ransomware encrypted files by retrieving the encryption key used by the ransomware.
