We have covered Ransomware frequently in the past – how to prevent it, what to do if attacked, and how it is affecting computer security globally. Today we take a look at the incidence of Ransomware in India. How prevalent it is and is the Indian government and corporate India ready to face this new cyber threat.
Ransomware has come to India in force, but India is yet to wake fully up to the problem. It better do so soon, as cybercriminals are now targeting the Indian Government servers, small businesses, the Indian banking sector – and even individuals.
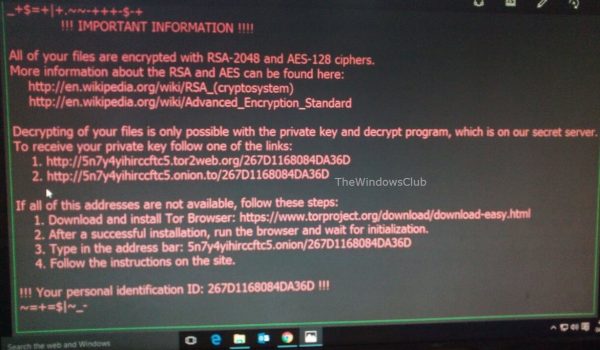
To-date malware has not really majorly created havoc in our lives. We have our antivirus software and we are reasonably protected. But this one is a different genre. Ransomware will silently get into your computer, lock all your files and data and demand a ransom to unlock it and make it usable. If this happens, you could well have a disaster on your hands – unless of course, you have backed up your data safely.
Read: Cyber hygiene is generally poor in India; Most hit by Ransomware!
Incidence of Ransomware in India

India is 5th largest target for Ransomware in the world
The problem of ransomware entered India several months back, and if reports are to be believed, India is already the 5th-most attacked country in the world and the 3rd-most attacked in Asia. Not expecting to be hit so hard, folks are slowly waking up from sleep to find out that ransomware is already spreading out fast – especially within the government and banking institutions.
“Ransomware attacks are high in India and it is one the top five countries that has most infections,” says Vitaly Kamluk, Head of APAC Global Research and Analysis Team, Kaspersky Lab.
The US-based Symantec Corporation says that India is now receiving ransomware attacks at a rate of 65,000 per annum. This translates to approximately 170 ransomware attacks a day.
FireEye, another US-based security firm observed that ransomware detections in India rocketed by a factor of 292 in February 2016 over November 2015.
Most of the ransomware attacks in India are crypto-ransomware. This is an attack where all the data of connected devices are encrypted so that the user cannot use them until they pay up money as directed by the cyber attackers.
In India, over 11,000 users were attacked by TeslaCrypt ransomware during the period of March-May 2016 and ranked 1st in the list of countries attacked by it in that period. TeslaCrypt has now been shut down, and its master decryptor key released on the Internet for all. During the same period, around 600 users were attacked by Locky ransomware and ranked 4th in the list of countries attacked by this ransomware during that time. Android ransomware named Lockdroid is also making its presence felt in the Android OS smartphone segment. Samas too has hit India. WannaCrypt ransomware has impacted India too.
State-wise, Karnataka tops the list of ransomware infections, and the other percentages are as follows:
- Karnataka – 36.58 %
- Tamil Nadu – 16.72 %
- Maharashtra – 10.86 %
- Delhi – 10.00 %
- West Bengal -6.70 %
- Uttar Pradesh – 5.33 %
- Telangana – 4.54 %
- Kerala – 3.87 %
- Gujarat – 2.35 %
- Haryana – 1.96 %
The attacks that go unreported are anybody’s guess!
Microsoft recently published a data mentioning how many machines (users) were affected by ransomware attacks across the world. It was found that the United States was on the top of ransomware attacks; followed by Italy and Canada. In this list, India stood at number 16.
According to statistics released by Symantec, the main targets other than the India government servers are entities based on Internet of Things and the ones using Android smartphones. Along with Lockdroid, FLocker, mobile lock-screen ransomware is also threatening Android-powered Smart TVs, says Trend Micro. Wearables could well be the next category to be targetted.
The Internet population in India as of June 2016 end, is around 462 million people. With such a large user base that does not even take Online Privacy, let alone Ransomware seriously, it is all gold for the cyber-criminal.
Ransomware attack targets in India – Government, Banks, and More
Three Bank & a Pharma company were hit by Lechiffre ransomware
In January 2016, several IT admins received an email. Four of them – three working in different banks and one working in a pharmaceutical company took the bait and infected their systems and encrypted their files using Lechiffre ransomware. Once this happened, the four received an email, demanding that they hand over 1 BitCoin (INR 30,000 or USD 400 approximately) for each PC, if they wanted to unlock their company data.
Two Business houses reported having paid $ 5 million
In May 2016, two large Indian houses were reported to have paid around $5 million, after they found that their systems were compromised. The Ransomware said to be operating from the Middle East, threatened to leak information to the Indian government if the ransom wasn’t delivered. Both paid up. This was reported in the Indian press.
Maharashtra Government hit – Lost data on 150+ computers
The Revenue Department of the Govt. of Maharashtra – one of the biggest states in India – was attacked in May 2016. The attack crippled more than 150 computers, and they have not yet been recovered as of the time of writing this post. The report stated that the Locky ransomware struck the main server, propagated to other computers on the network, and was asking payments in virtual online currencies like Bitcoins.
Read: Indian Forest Department falls victim to Ransomware attack.
Banks and Small Businesses
Several other businesses are still running Windows XP, even after the end of support. These firms are at high risk of being hacked and injected with ransomware. Microsoft has urged that companies should migrate to Windows 10, but the call goes unheard. Possibly they are averse to spending money to upgrade their operating system, their software as well as their hardware to newer versions.
I have noticed that some Bank ATMs are still using Windows XP. They have not yet started upgrading despite the RBI urging them to upgrade at least to Windows 7. They say the cost would be too high, and the consumers won’t pay for transactions. If reports are to be believed, banks are working on replacing cards with Chip and PIN. That won’t help them in preventing a simple hacking attack, let alone dealing with ransomware.
Now let us take a look at the kind of damage Ransomware could inflict of government schemes.
Damage to Government’s Ambitious Schemes – Destroying Digital India
With the government change in May 2014, two new schemes were announced:
- E-governance
- Smart Cities
You already know that e-governance means servers and mirrors running round the clock. Online complaints, online registrations, and even online direct debits for people. Cyber-criminals won’t think twice before encrypting the data of such people. As the government wants them to benefit, if their IDs and bank details etc. are destroyed, it could be a huge mess – completely derailing the system.
Smart Cities concepts are based completely on the Internet of Things. All things in a smart city are connected to each other and also to a central point that connects them to other smart cities. The new government is working hard on the smart cities concept. Many times, I have seen computers still running the outdated Windows XP in government offices! In such cases, it would be easy for a cybercriminal to take control of an entire city.
If we look at the whole picture, the threat of ransomware in India is high, partly because of the ostrich mentality and partly because institutions don’t want to invest more in cybersecurity. Folks are still using outdated operating systems and are not very alert when it comes to clicking on web links and do not even take the basic precautions while opening email attachments.
India is on the road to economic progress and as a result, the ferocity & frequency of ransomware attacks are expected to increase exponentially. I guess it will take a couple of harsh attacks before organizations & the government realize the gravity of the situation and move towards safeguarding their digital assets.
The best way to protect yourself and prevent Ransomware attacks is to regularly back up your data to a different location, use a good anti-ransomware software, a fully updated modern operating system, ensure that all your installed software, especially your security software & browser are updated to the latest version, and exercise caution while clicking on any web link or opening email attachments.
Nevertheless, if you do happen to have the misfortune of being infected with ransomware, then this post will tell you what to do after a Ransomware attack.
UPDATES:
1] Ransomware comes too close for comfort! A screenshot of my friend’s (Pune, India) computer whose Windows 10 system was hijacked by the Cerber ransomware! He has no backups – so he has to either kiss goodbye to all his business data or pay up!
2] The WannaCrypt Ransomware has come to India too. Stay alert folks!
If you want to learn more, read this post titled Ransomware Attacks & FAQ.