The CryptoLocker ransomware has been in the news recently. It is malware that uses email attachments as a vector to spread. It arrives as an executable file disguised as a PDF file, packed into a zip attachment. When it is opened, it encrypts the user’s data on all the local hard drives of the system. While there may be several other tools and security software that may help protect you from the CryptoLocker ransomware, one good free anti-ransomware tool which comes to my attention was HitmanPro.Alert.
While having a fully updated operating system, browser along with an antivirus or security software is generally more than enough to protect any Windows computer, if you are looking for an additional layer to security you may want to check out HitmanPro.Alert.
HitmanPro.Alert Review
HitmanPro.Alert is a free browser integrity & intrusion detection tool that alerts users when online banking and financial transactions are no longer safe. The latest version HitmanPro.Alert 2.5 also contains a new feature, called CryptoGuard that monitors your file system for suspicious operations. When suspicious behavior is detected, the malicious code is neutralized, and your files remain safe from harm.
HitmanPro.Alert focuses on keeping your system safe from banking trojans. HitmanPro.Alert will instantly detect over 99% of all known and new banking Trojans & Man-in-the-Browser malware and automatically inform users when critical system functions are diverted to untrusted programs. When you bank or shop online or remotely connect to your office, cybercriminals try to target the vulnerabilities in your browser, plug-ins and operating system and silently infect your computer. HitmanPro.Alert will immediately alert you if it detects any intrusions.
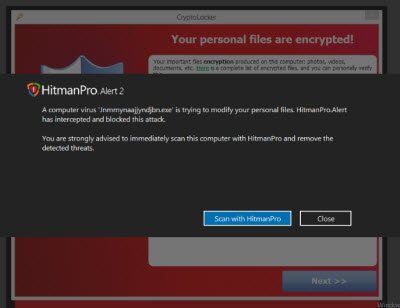
The newly introduced CryptoGuard works silently in the background at the file system level, keeping track of processes modifying your personal files – without requiring any user interaction. ThusHitmanPro’s CryptoGuard can protect you against the CryptoLocker ransomware, which encrypts your personal files and demands a ransom fee to be paid in order to regain access to your files. The moment any attempt is made to change the status of the files, you will be alerted. It works at the file system level and does not conflict with a full disk encryption software like BitLocker, TrueCrypt, etc.
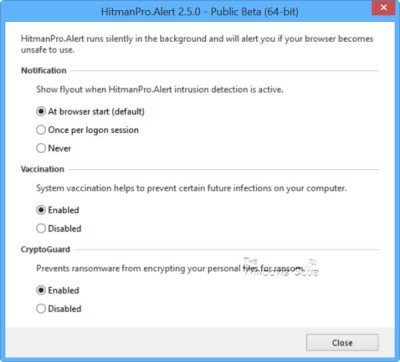
Once you have downloaded and installed HitmanPro.Alert, you will find that it sports a clean simple interface. Clicking on the Settings button will open the settings box, where you can configure the options.
If you open the Program Folder, you will see a single small hmpalert application file. The tool runs a HitmanPro.Alert service in the background which utilizes near-nil resources. The description for this service reads as Web browser intrusion detection, real-time and forensics-based, watching for banking trojans and Man-in-the-Browser attacks.
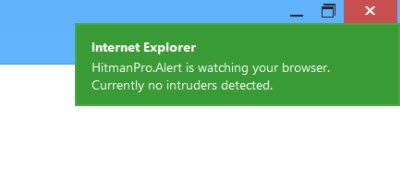
Now every time you open your browser, you will see a small notification for a few seconds saying that HitmanPro.Alert is watching your browser.
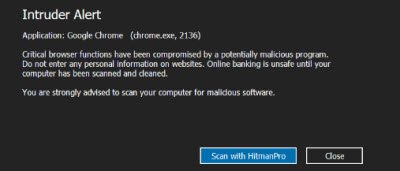
If any browser intrusion is detected, you will receive an alert.
When CryptoGuard intercepts an attack on your personal files, it presents you with an Alert message. When the above alert is displayed, the malicious process is neutralized. It can no longer harm your files.
HitmanPro.Alert will not help you remove the malware should your computer get infected. You will have to use a security scanner software to remove it. What this tool does, is that it instantly alerts you if it detected malware activities when you are browsing & try to disable it – and this can be especially useful if you are carrying out sensitive financial or banking transactions. The vaccination feature makes most sandbox-aware malware disable itself. It can protect you against CryptoLocker Ransomware and financial trojans like Zeus, Shylock, SpyEye, Sinowal, Ice-IX, Citadel, Cridex, Carberp, Tinba and many more.
HitmanPro.Alert supports almost all browsers and runs on all the recent versions of Windows,. You can download it from here. Do note that HitmanPro.Alert 2.5 is currently in beta.
CryptoPrevent is another handy tool that provides your computer a shield against Cryptolocker or any other kind of ransomware. HitmanPro.Kickstart from the same publishers will help remove Ransomware. CryptoLocker Tripwire stops Server service and VSS as soon as it detects CryptoLocker ransomware on a Windows system. This post on how to prevent Ransomware will suggest steps to take to stay protected and offer links to ransomware removal tools.
The CryptoLocker Decryption Tool may help you decrypt your Cryptolocker encrypted file.