Penguin Proxy is a Peer to Peer (P2P) network that can hide your IP address when connecting to any website. As of creating this post, the makers of PenguinProxy have built apps compatible with Windows 10, Linux, and macOS respectively. Also, it is available as browser extensions too. This Penguin Proxy review checks the proxy apps instead of just the browser extensions and documents our experience with the Penguin Proxy VPN.
PenguinProxy review
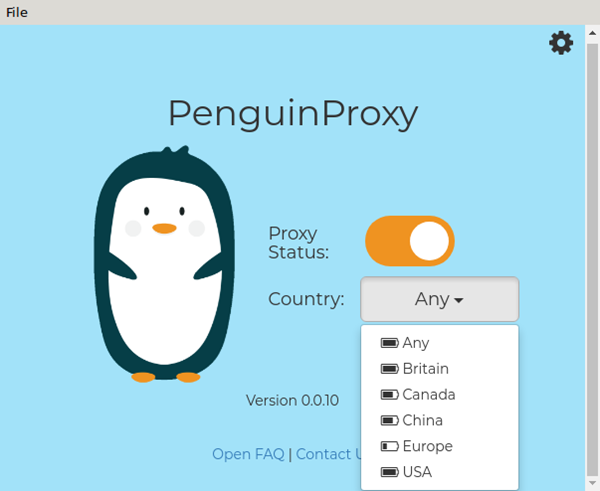
The Penguin Proxy browser extensions can only secure your browsers’ communication with any website you are visiting. To use it:
- Download the installer and run the exe
- Simply install the browser extension to your browser
As of now, browser extensions are available to Chrome and Firefox only. An app is better if you are using a different browser or if you frequently switch between/among browsers.
The P2P (peer to peer) model helps you only with changing the proxy’s IP address. The makers of Penguin Proxy claim they do not even store logs of what you do while using the proxy.
Is it a VPN or Proxy?
It is, in fact, a Proxy software with a bit of VPN. It does not encrypt the data to and from your computer. It depends on the HTTPS connection of web pages. You already know the difference between HTTP and HTTPS. The latter is securer compared to HTTP. In other words, instead of encrypting the data packets itself, the proxy uses the raw data encrypted by HTTPS EVERYWHERE facility that comes with almost all browsers.
I wouldn’t call it a Virtual Private Network at this stage. It is, according to my experience, a simple proxy with all the benefits of a VPN.
How Penguin Proxy works
The working part of the Penguin Proxy is borrowed from The Onion Router (TOR). While people use TOR, the data packets from their computers go from one peer computer to another in a way that the website (HTTP/S) and other protocols cannot get your real IP address already.
The proxy works somewhat like Windows Update using P2P computers to provide operating system updates (unless you turned it off). With Penguin too, you have to download a piece of software to your computer. The makers of Proxy Penguin call it client software.
The same piece of software is used on all computers that use Penguin Proxy. It means that the data packets of other users on the Penguin network can use your computer to receive and forward data packets just as TOR does. In the case of TOR, the route is too long so that the Internet Service Providers and whoever wants to tap into your computer do not receive your IP address. Same way, the computers on Penguin Proxy are related to each other for ‘helping in upholding your privacy’.
That part also turns into – “Your computer Internet data usage may go up because your computer is accepting the data packets of other users and forwarding them to another node (computer)’.
Pros and Cons of Penguin Proxy
The positive features of Penguin Proxy are:
- Low system resource usage
- Third party encryption (as of January 19, 2019, it employs HTTPS EVERYWHERE)
- Fast but at some cost (see cons)
- May increase your Internet charges
As far as the negative factors are concerned:
- HTTPS EVERYWHERE – Should incorporate its own encryption
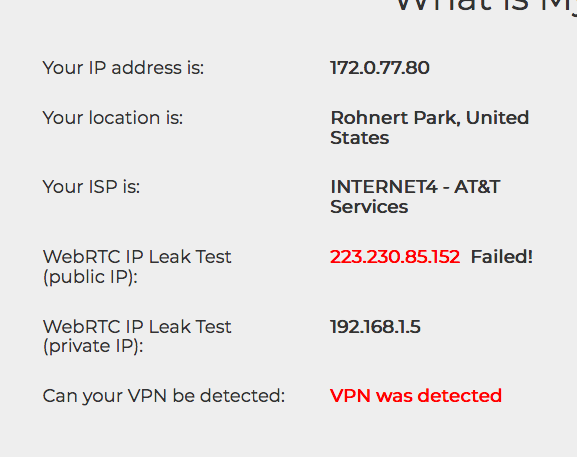
- Nor a VPN really – Websites can tell that you are using a proxy or VPN; when I visited What is My IP Address website, while my IP was changed to US, the results retained “VPN detected” label (See image above)
Should you use it? If you need to watch region-restricted websites, PenguinProxy is good. But it doesn’t support any protocol other than HTTP/HTTPS. That means you cannot use for things as important as war reporting. Other apps that use more than just HTTP/S protocol, will give away your IP address when used outside of the browser. You can download it here.
Any users here? Your experience?