Windows Sandbox is a great tool for testing out some applications and utilities in an isolated environment. But many times, a user looks out to create a custom environment to test out various software and services. This was one of the pros of Virtual Machines over the Windows Sandbox environment. But Microsoft has been actively listening to the user feedback and have added support to create custom configuration environments for Windows Sandbox.
Configure and use Windows Sandbox
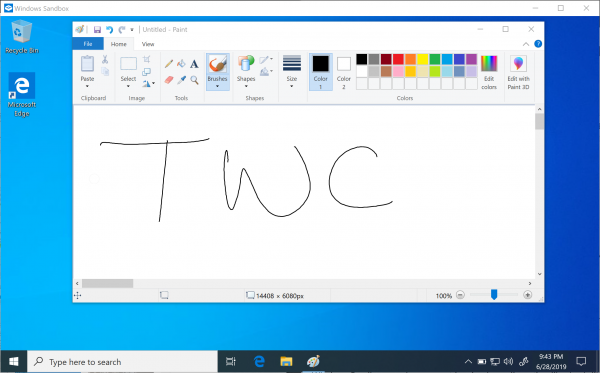
Create custom configuration environments for Windows Sandbox
The configuration files for Windows Sandbox environment are in XML formatting. The Windows Sandbox environment reads them as a .WSB file. Currently, only the following four configurations are supported by Windows Sandbox:
- vGPU (Virtualized GPU).
- Networking.
- Shared folders.
- Startup script.
The mechanism of function for these WSB files goes as:
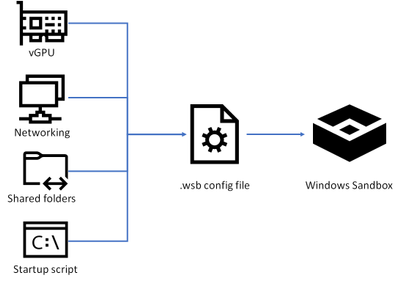
This will give users greater control over the isolated environment in Windows Sandbox.
You will have to create or open these WSB files using Notepad or Visual Studio Code.
This is how the configurations for the mentioned aspects are to be done.
1] vGPU
The syntax for the vGPU aspect of Windows Sandbox is given as:
<vGpu>VALUE</VGpu>
And the supported values for this aspect are:
- Disable: This value can be used to disable the vGPU support in the Sandbox.
- Default: This value can be used to maintain the default and current value of vGPU support.
Microsoft notes,
Enabling virtualized GPU can potentially increase the attack surface of the sandbox.
2] Networking
The syntax for the networking aspect of Windows Sandbox is given as:
<Networking>VALUE</Networking>
And the supported values for this aspect are:
- Disable: This value can be used to disable the networking support in the Sandbox.
- Default: This value can be used to maintain the default and current value of networking support.
Microsoft notes,
Enabling networking can expose untrusted applications to your internal network.
3] Shared folders
The syntax for the Shared folders aspect of Windows Sandbox is given as:
<MappedFolder>
<HostFolder>PATH OF THE HOST FOLDER</HostFolder>
<ReadOnly>VALUE</ReadOnly>
</MappedFolder>
And the supported subaspects for this aspect are:
- HostFolder: Specifies the folder on the host machine to share to the sandbox. Note that the folder must already exist the host, or the container will fail to start if the folder is not found.
- ReadOnly: If true, enforces read-only access to the shared folder from within the container. Supported values: true/false.
Microsoft notes,
Files and folders mapped in from the host can be compromised by apps in the Sandbox or potentially affect the host.
4] LogonCommand
The syntax for the LogonCommand aspect of Windows Sandbox is given as:
<LogonCommand>
<Command>COMMAND TO BE INVOKED ON STARTUP</Command>
</LogonCommand>
And the supported subaspects for this aspect are:
- Command: It will be an executable script that will be executed on the startup.
Microsoft notes,
Although very simple commands will work (launching an executable or script), more complicated scenarios involving multiple steps should be placed into a script file. This script file may be mapped into the container via a shared folder, and then executed via the LogonCommand directive.
Example
Microsoft has given a proper example of a customized Windows Sandbox environment with vGPU and Networking being disabled, Read Only access to the shared Downloads folder, and the Downloads folder will be launched on startup.
The code goes by:
<Configuration>
<VGpu>Disable</VGpu>
<Networking>Disable</Networking>
<MappedFolders>
<MappedFolder>
<HostFolder>C:\Users\Public\Downloads</HostFolder>
<ReadOnly>true</ReadOnly>
</MappedFolder>
</MappedFolders>
<LogonCommand>
<Command>explorer.exe C:\users\WDAGUtilityAccount\Desktop\Downloads</Command>
</LogonCommand>
</Configuration>
Alternatively, you can download this file directly from our servers and try it out by yourself.
The best part about this feature is that it is available to use on Windows 10 1903 May 2019 Update and newer. This means that, if you are running Windows 10 build 18342or newer, you will be able to make use of this feature without any issues.
You can learn more about this feature at Microsoft.