Microsoft automatically encrypts your new Windows device and stores the Windows 11/10 Device Encryption Key on OneDrive, when you sign in using your Microsoft Account. This post talks of why Microsoft does this. We will also see how to delete this encryption key and generate your own key, without having to share it with Microsoft.
Windows Device Encryption Key saved to OneDrive
If you bought a new Windows 11/10 computer and signed in using your Microsoft account, your device will be encrypted by Windows and the encryption key will be stored automatically on OneDrive. This is nothing new, actually and has been around since Windows 8, but certain questions relating to its security have been raised recently.
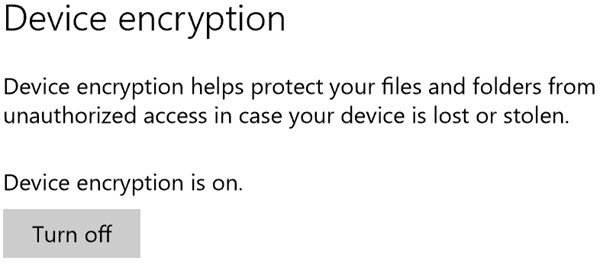
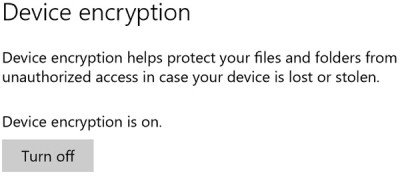
For this feature to be available, your hardware must support connected standby that meets with the Windows Hardware Certification Kit (HCK) requirements for TPM and SecureBoot on ConnectedStandby systems. If your device supports this feature, you will see the setting under Settings > System > About. Here you can turn off or turn on Device Encryption.
Disk or Device Encryption in Windows 11/10 is a very good feature that is turned on by default on Windows 10. What this feature does is that it encrypts your device and then stores the encryption key to OneDrive, in your Microsoft Account.
Device encryption is enabled automatically so that the device is always protected, says TechNet. The following list outlines the way this is accomplished:
- When a clean install of Windows 8.1/10 is completed the computer is prepared for first use. As part of this preparation, device encryption is initialized on the operating system drive and fixed data drives on the computer with a clear key.
- If the device is not domain-joined a Microsoft Account that has been granted administrative privileges on the device is required. When the administrator uses a Microsoft account to sign in, the clear key is removed, a recovery key is uploaded to an online Microsoft account and the TPM protector is created. Should a device require the recovery key, the user will be guided to use an alternate device and navigate to a recovery key access URL to retrieve the recovery key using their Microsoft Account credentials.
- If the user signs in using a domain account, the clear key is not removed until the user joins the device to a domain and the recovery key is successfully backed up to Active Directory Domain Services.
So this is different from BitLocker, where you are required to start Bitlocker and follow a procedure, whereas all this is done automatically without the computer user’s knowledge or interference. When you turn on BitLocker you’re forced to make a backup of your recovery key, but you get three options: Save it in your Microsoft account, save it to a USB stick, or print it.
Says a researcher:
As soon as your recovery key leaves your computer, you have no way of knowing its fate. A hacker could have already hacked your Microsoft account and can make a copy of your recovery key before you have time to delete it. Or Microsoft itself could get hacked, or could have hired a rogue employee with access to user data. Or a law enforcement or spy agency could send Microsoft a request for all data in your account, which would legally compel it to hand over your recovery key, which it could do even if the first thing you do after setting up your computer is delete it.
In response, Microsoft has this to say:
When a device goes into recovery mode, and the user doesn’t have access to the recovery key, the data on the drive will become permanently inaccessible. Based on the possibility of this outcome and a broad survey of customer feedback we chose to automatically backup the user recovery key. The recovery key requires physical access to the user device and is not useful without it.
Thus, Microsoft decided to automatically backup encryption keys to their servers to ensure that users do not lose their data if the device enters Recovery mode, and they do not have access to the recovery key.
So you see that in order for this feature to be exploited, an attacker must be able to both gain access to both, the backed-up encryption key as well as gain physical access to your computer device. Since this looks like a very rare possibility, I would think that there is no need to get paranoid about this. Just make sure that you have fully protected your Microsoft Account, and leave the device encryption settings at their defaults.
Nevertheless, if you would like to remove this encryption key from Microsoft’s servers, here is how you can do it.
How to remove the encryption key
There is no way to prevent a new Windows device from uploading your recovery key the first time you log in to your Microsoft account., but you can delete the uploaded key.
If you do not want Microsoft to store your encryption key to the cloud, you will have to visit this OneDrive page and delete the key. Then you will have to turn off Disk encryption feature. Mind you, if you do this, you will not be able to use this built-in data protection feature in case your computer is lost or stolen.
When you delete your recovery key from your account on this website, it gets deleted immediately, and copies stored on its backup drives also get deleted shortly thereafter as well.
The recovery key password is deleted right away from the customer’s online profile. As the drives that are used for failover and backup are sync’d up with the latest data the keys are removed, says Microsoft.
How to generate your own encryption key
Windows 10 Pro and Enterprise users can generate new encryption keys that are never sent to Microsoft. For that, you will have to first turn off BitLocker to decrypt the disk, and then turn on BitLocker again.
When doing this, you will be asked where you want to back up the BitLocker Drive Encryption Recovery Key. This key will not get shared with Microsoft, but make sure you keep it safe, because if you lose it, you may lose access to all your encrypted data.