If you want to turn off or disable hardware-based encryption on removable drives while using BitLocker, you can follow this guide. It is possible to use software-based encryption instead of hardware-based encryption on BitLocker removable drives with the help of this guide. You can enable this setting using Local Group Policy Editor and Registry Editor.
Disable Hardware-based encryption on BitLocker Removable drives
To disable hardware-based encryption on removable drives in Windows 11/10 using Group Policy Editor, follow these steps:
- Press Win+R to open the Run prompt.
- Type gpedit.msc and hit the Enter button.
- Navigate to Removable Data Drivesin Computer Configuration.
- Double-click on the Configure use of hardware-based encryption for removable data drives setting.
- Select the Disabled option.
- Click the OK button.
Let’s learn more about these steps in detail.
At first, you have to open the Local Group Policy Editor. To do that, press Win+R to display the Run prompt, type gpedit.msc, and hit the Enter button.
Then, navigate to this path:
Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption > Removable Data Drives
In the Removable Data Drives folder, you can see a setting named Configure use of hardware-based encryption for removable data drives. You need to double-click on this setting on the right-hand side and choose the Disabled option.
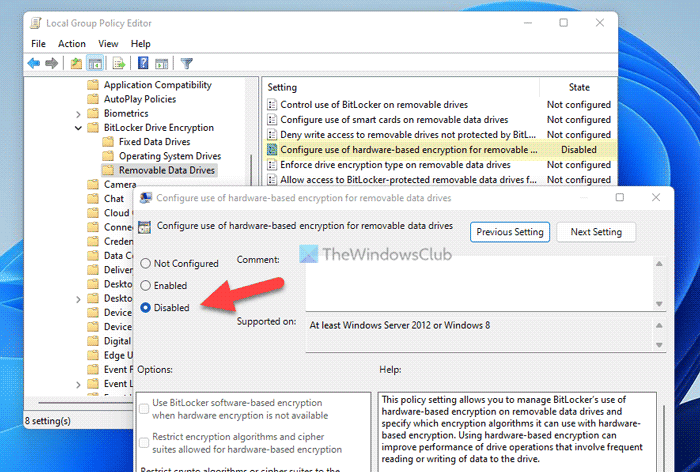
Once done, click the OK button. From now onwards, the hardware-based encryption will be disabled for removable data drives while using BitLocker. However, there is another option that allows users to opt for software-based encryption only when hardware encryption is not available.
To enable that setting, you need to choose the Enabled option instead of the Disabled option. Then, tick the Use BitLocker software-based encryption when hardware encryption is not available checkbox.
How to disable hardware-based encryption on removable drives using Registry
To disable hardware-based encryption on removable drives using Registry, follow these steps:
- Search for registry editor and click the search result.
- Click the Yes button.
- Navigate to Microsoft in HKLM.
- Right-click on Microsoft > New > Key and set the name as FVE.
- Right-click on FVE > New > DWORD (32-bit) Value.
- Name it as RDVHardwareEncryption.
- Repeat these steps to create another REG_DWORD value named RDVAllowSoftwareEncryptionFailover.
- Do it again and name it as RDVRestrictHardwareEncryptionAlgorithms.
- Close all windows and restart your computer.
To learn more about these steps, keep reading.
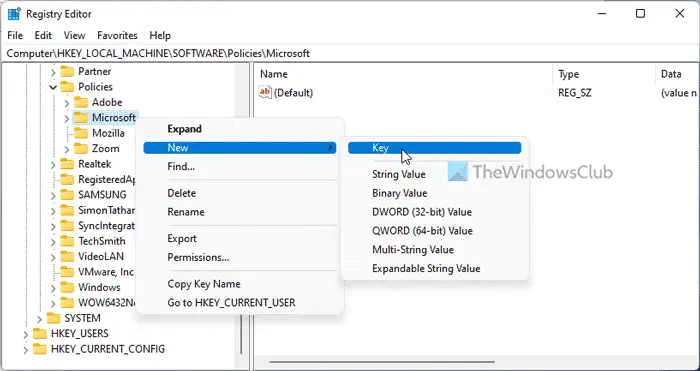
In order to use the Registry Editor method, you need to open it first. For that, you can search for registry editor in the Taskbar search box and click on the search result. Then, click the Yes button in the UAC prompt.
Next, navigate to this path:
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft
Right-click on the Microsoft key, select New > Key, and name it FVE.
Then, right-click on FVE > New > DWORD (32-bit) Value and name it as RDVHardwareEncryption.
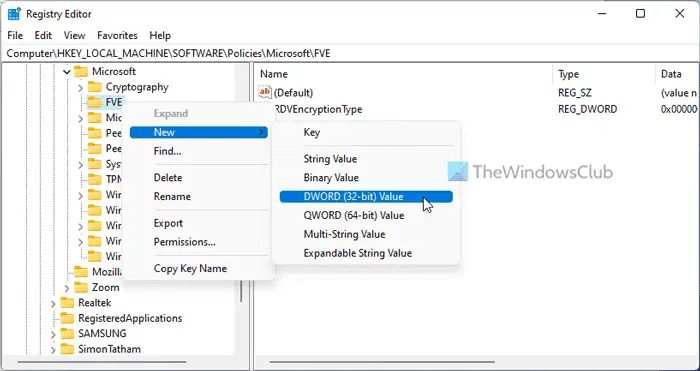
By default, it has a Value data of 0, and you need to keep that.
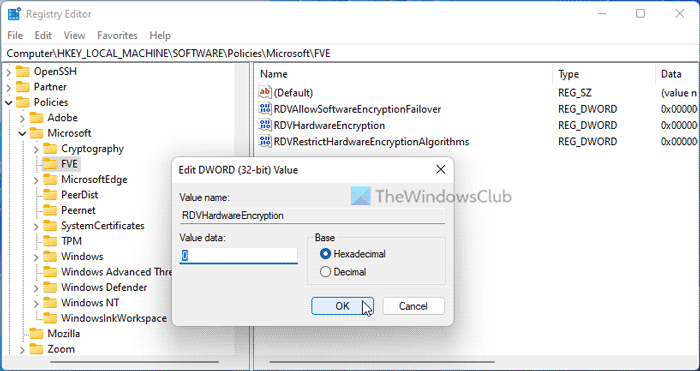
Next, you need to create two more REG_DWORD values:
- RDVAllowSoftwareEncryptionFailover
- RDVRestrictHardwareEncryptionAlgorithms
As usual, keep the Value data as 0. Finally, close all windows and restart your computer.
Read: Check BitLocker Drive Encryption Status for Drive using Command Prompt or PowerShell
How do I disable hardware encryption?
To disable hardware encryption on removable drives in Windows 11/10, you need to use Local Group Policy Editor or Registry Editor. For that, open the Removable Data Drives section and double-click on the Configure use of hardware-based encryption for removable data drives setting. Then, choose the Disabled option.
What is hardware disk encryption?
Hardware disk encryption is a kind of encryption available in Windows computers that basically converts the data into a different code. Thus, users or any other program cannot read the unreadable code without decrypting it first. You can enable or disable such settings with the help of GPEDIT and REGEDIT.
That’s all! Hope it helped.
Read: Turn On or Off Auto-unlock for BitLocker Encrypted Data Drives.
Leave a Reply