Hi. I am Creeper. Catch me if you can. It was the ’50s! Back then, computers were big. Programmers used punching cards. One such programmer – Bob Thomas – experimented with self-replicating programs and created the Creeper. Fortunately, the worm could not self-replicate, but it did affect users of ARPAnet (one of the first computer networks’ community). From there, began a journey into the most dangerous realms of the Internet.
Let us check out the evolution of malware after taking a quick look at the difference between a worm and a virus.
Worm vs Virus
A Worm is basically a program that can self-replicate across computers and other types of digital devices. A Virus needs to be attached to something like an application and needs a trigger, such as the execution of that application, to work for whatever intention it was created. In other words, worms are independent and can replicate without the need for any triggers. They can be downloaded with other programs. They can affect your computers bypassing through Flash drives. A virus uses plenty more methods in addition to the two mentioned here, to get into a computer and infect it. It requires some action to be taken by the user before it becomes active and does the work for which it is programmed.
These days, we do not hear about worms explicitly. We have a common word called Virus and even a more generic one – Malware. Since these days, the intentions of worms and viruses, plus other types of software like Spyware, etc. are malicious or bad, they are collectively called Malware. Unlike the beginning, where malware was the result of curiosity and experimentation, and the intention was merely to irritate, cause mischief or havoc, these days’ viruses are full programs that are intended to steal or destroy data. The intentions are bad as the industry creates malware for their benefits at your costs.
History and Evolution of Malware and Viruses
The first Internet Worm and a great deal of MS-DOS viruses were harmless to both the user and the computer. They were designed to be annoying and let the world know about their creator’s existence. But with the passage of time, things changed. Today’s malware writers exploit their creations to use infected machines and then steal banking credentials, send spam messages, or leverage their revenue by advertisement click fraud. Corporate espionage also brings constant revenue, as malware opens backdoors into the organization’s network.
Although WinVer 1.4 was said to be the first Windows virus, the first malware to be introduced to the world was the Creeper. It was not a malware by definition though. It simply displayed a message which would irritate users and as a result, the first anti-virus software was born. It was named Reaper and it was made to counter Creeper. There are different arguments saying this cannot be called malware as it could not replicate or cause damage to computers, but still, many accept Bob Thomas and his Creeper as the beginning of what later turned into a multi-billion industry of malware. Bob could not have even imagined that.
Anyway, the next malware was said to be Brain. It was developed by two Pakistan-based people in 1986. By this time, the general public too had fans of computers and there were many hobby groups and communities that were run using computers. The target of Brain was these communities. It targeted the boot sector of computers via a 5 1/4 inch floppy disks and showed just a message. It, too, was not intended to steal data or cause data loss in any way. It also gave the phone number of the malware developers – Basit and Amjad – so that people could ask them for help to remove the malware.
The first reference to a worm that caused damage (presumed to be because of a bug in the worm code) was Morris’ worm. It was developed by Robert Morris, a student at Carnell University. Again, as with the Creeper, people argued this was the first worm – as it could replicate. “Worms need to replicate else they are not worms”, people argue. This infected more than 5000 computers in the USA and caused damage between 100,000 and 10,000,000. The exact damage could not be estimated.
The biggest turn in the history of malware or its evolution was the LoveLetter worm. By that time, most organizations had computers working on MS-DOS or other similar operating systems. It was the year 2000 and the LoveLetters that contained an infected attachment which when, downloaded, infected the email program and sent a copy of the worm to people in recipients’ address book. Not only that, it overwrote certain file types with rubbish. By the time it was discovered as not being a prank and a serious threat, the damage was done. However, it educated people about malware and that people out there are not all good – but bad ones too who would want to play with the data they had on their computers.
A need for anti-virus software on every computer was stressed and was implemented slowly. Of course, those were small codes that kept on updating themselves as and when new worms or viruses are discovered.
The year 2001 saw the emergence of Red Code, a malware that targeted Microsoft IIS based systems. Normal antivirus could not find it as it was resident in the active memory of the computer. The worm could be detected only in transit. Traditional antivirus failed and the need arose for better ones that can scan all parts of a computer where such malware can reside: boot sector, memory, hard disks, application files, etc.
Then came Win32/Ninda which was a threat to Networks. It used network backdoors to spread and affected hundreds of thousands of computers and web servers. Many websites were compromised and provided as a source for further infections. By this time, Internet usage was in full swing. It is said the malware initiated around the attacks of Sept 11, 2001. Antivirus vendors went back to their drawing boards to create antivirus that could also monitor network ports, especially Port 80 – the one used to connect to the Internet and detection of other open or closed ports that they need(ed) to hide from the networks.
People were also educated about the possibilities of Spyware, Adware, etc and the collective term, Malware, was subsequently coined. You can read the difference between Virus, Trojan, Worm, Adware, Rootkit, etc, here.
Over the last two decades, both malware and anti-malware programs have become complex. Phishing became part of the Internet soon and antivirus had to scan complete emails – including the contents – to make sure there are no malicious URLs, etc.
We can say that in the last decade, especially, had seen a tremendous rise in dreaded virus problems, as well as good improvements in the antimalware solutions. There are many free antivirus software and free Internet Security Suites, that act as well as the paid options. One now needed to take an integrated approach to fight malware, and hence Firewalls, Heuristics, etc, were also made a part of the arsenal.
There are competing claims for the innovator of the first antivirus product. Possibly the first publicly documented removal of a computer virus in the wild was performed by Bernd Fix in 1987. By the end of 1990, there were a number of anti-virus products available.
Infographic
BitDefender has prepared this wonderful and very informative Infographic on the timeline and history of computer viruses starting 1970. The history of malware is rife with incidents that allowed viruses to morph from innocent pranks to advanced military weapons.
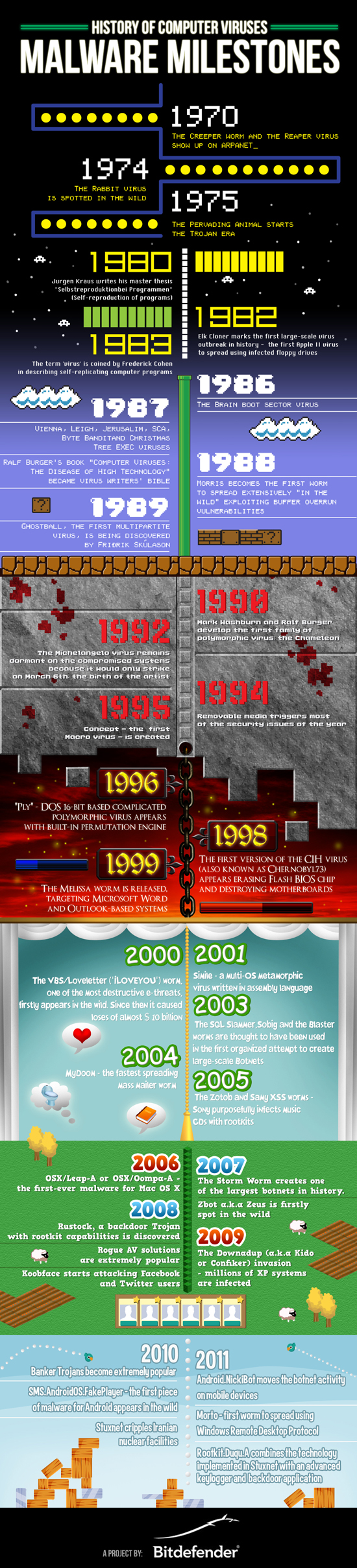
If you’d like to find out more about how malware grew in time, download this PDF copy of the Malware History whitepaper from BitDefender. There is also a lot of information at Microsoft, on the evolution of malware and malware trends.
Ransomware, Rogue software, Rootkits, Botnets, RATs, Malvertising, Phishing, Drive-by-download attacks, Online Identity Theft, are all here to stay now. New technologies that have emerged or are emerging, including but not limited to BYOD and the Internet of Things will be attacked. Malware has also started focusing on Social Media. While good security software will help you stay protected, it is equally important to carry out safe Internet and Browsing practices.