If a code loading from the default heap or stack is detected by DEP or Data Execution Prevention, an exception is raised. It happens since the behavior is indicative of malicious code (legitimate code does not generally load in this manner). This way DEP protects the browser against attacks rendered, for example, via buffer overflow and similar type vulnerabilities.
Although a valuable feature, DEP can sometimes be the cause of certain system issues and error messages. So, if you would like to disable Data Execution Prevention for the Internet Explorer browser only, here is how you can do it :
Disable Data Execution Prevention DEP for Internet Explorer
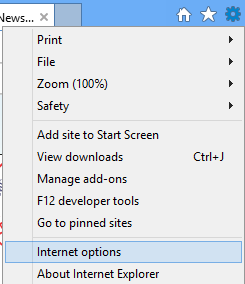
Open Internet Explorer and go to ‘Tools’. The icon appears as a small gear-shaped icon at the extreme top-right corner of Internet Explorer screen. Click open ‘Tools’ and from the displayed options, select ‘Internet Options’.
Next, click on ‘Advanced’ tab and scroll down until you find the ‘Security’ option. Un-check on Enable memory protection to help mitigate online attacks.
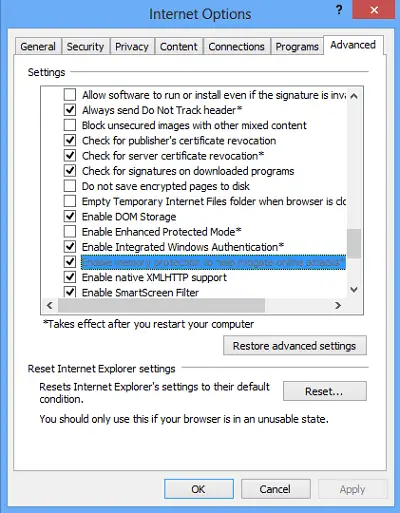
Click Apply / OK. This will disable Data Execution Prevention for Internet Explorer.
To enable Data Execution Prevention, check the check-box instead, click Apply and Exit.
Want to have a look at these posts too?
