When more code or data is entered into a system buffer than the system was designed to handle, a program security vulnerability known as a Buffer Overflow comes up, by which the excess data overwrites the adjacent memory section of the system; therefore, in such a system, this occurrence creates an influence. Additionally, this concept is both straightforward and highly complex. But let us start with the more specific element, buffer. Computers use buffers to store data to facilitate your actions when running a program or performing any other task. When streaming on apps like Spotify, you may be curious as to why your music continues playing for a short period after your network has been disconnected or your connection drops. This is because a code was written along with the software to save a portion of data (the music you are playing) in a memory area of your computer called a buffer.
What is Buffer Overflow Attack in cyber security
Buffer Overflow Attacks occur as a result of excess data being input into a system memory buffer. Moreover, when the memory buffer’s capacity has been reached, the music will stop playing. To avoid overwriting other data in your computer’s memory, some programs simply set a limit on how much should be stored in the buffer. However, if you enter more data than the buffer can handle, it may result in various problems on the device running the program or, more likely, a crash. Furthermore, this extra input has the potential to set off a lot of other processes in the system, which could either be based on the desire of the initiator, and this is what Buffer Overflow attack is. This is what Buffer overflows, and buffer overflow attacks are, and there are a variety of causes for them, all of which will be covered in this article.
How do attackers make use of Buffer Overflow vulnerability?
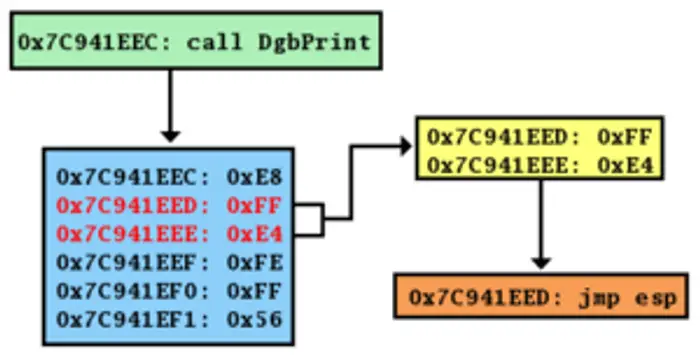
The buffer overflow vulnerability causes buffer overflow attacks, as was previously mentioned. Depending on the circumstances surrounding the flaw, attackers can take advantage of a system’s vulnerability to a buffer overflow in a number of ways. To put it another way, an attacker will generally add more data to a system in order to overwrite existing data in the system memory or at a returning address.
And so, the input causes their intended command to be executed, which they can utilize to their advantage or make your system generally unstable. The attacker’s primary goal is typically to hijack a program or make it malfunction.
Read: How to report Bug, Issue, or Vulnerability to Microsoft
What causes Buffer Overflow attack?
When faced with a buffer overflow attack, it is essential to know what may be causing the problem. The attack can either be due to a loophole from the programmer’s end or a hacker using the fact that there aren’t limiting parameters to control what could be input into a particular system.
In general, leaving these vulnerabilities and not fixing them up is the basic factor that causes buffer overflow attacks. Besides, if your system doesn’t have a programmed limit of what it should take, you’ll definitely be facing a buffer overflow attack.
Read: What is Replay Attack and how do you prevent it?
Types of Buffer Overflow attack
Buffer overflow attacks can be categorized based on the location of the buffer being targeted or affected by the attacker’s input. Generally, we’ve categorized buffer overflow attacks into:
1] Stack-based buffer overflow attack
The stack-based buffer overflow occurs when an attacker explicitly aims his input toward the stack section of the memory. This is the most common type of buffer overflow attack and the easier one. The excess input overruns the stack memory and hands the program’s control to the attacker.
2] Heap-based buffer overflow attack
This type of buffer overflow attack is aimed at another part of a system memory called Heap. This means an attack overwrites data at the heap side of the buffer. Heap-based buffer overflow attack is more brutal compared to the former.
How to prevent Buffer Overflow Attack
Using a programming language that is resistant to the attack is the most effective technique to prevent buffer overflow. C and C++ are highly susceptible to this attack as they don’t have built-in run time-bound checking features like programming languages such as Python, C#, and Java. Additionally, even though buffer overflow faults might occasionally be challenging to locate, it is still advised to review your application and hunt for vulnerabilities carefully.
The following are some methods to stop buffer overflow attacks:
- Keep devices patched
- OS runtime protection
- Use safe programming languages like Java, Python, and C#
- Address space randomization
- Manually testing for buffer overflow
Developers should be aware of the buffer overflow attack since it informs them of important concerns to assess when developing a system. Furthermore, it will make you more secure from hacker attacks. The most thorough discussion of buffer flow attacks has been provided in this post for your benefit, so please read the entire piece carefully.
Is Buffer Overflow a DoS attack?
Buffer overflow is the most common DoS attack that occurs. The attack happens when more data is input into a system’s memory buffer and, as a result, overwriting data in the nearby memory region.
Leave a Reply