Windows 11/10 uses XTS-AES 128-bit by default for operating system drives as well as fixed data drives – and AES-CBC 128-bit by default for removable data drives. In this post, we will show you how to set a default encryption method (XTS-AES or AES-CBC) and cipher strength (128-bit or 256-bit) you want to be used by BitLocker in Windows 11/10.
Windows introduced a new disk encryption mode (XTS-AES). This mode provides additional integrity support – but is not compatible with older versions of Windows. You can opt to use disk encryption Compatible mode (AES-CBC) that is compatible with older versions of Windows. If you’re encrypting a removable drive that you’re going to use on an older version of Windows, you should use AES-CBC. Both BitLocker Drive Encryption modes above support using 128-bit or 256-bit cipher strength.
How do I enable BitLocker encryption in Windows?
To enable BitLocker encryption in Windows, open the Control Panel and select ‘System and Security’. Click on ‘BitLocker Drive Encryption’ and choose the drive you wish to encrypt. Press ‘Turn on BitLocker’ and follow the prompts to set up a password and back up your recovery key.
Change BitLocker Encryption method & Cipher Strength
The BitLocker encryption method and Cipher strength you set as default is only applied when you turn on BitLocker for a drive. Any changes you make will not affect a drive already encrypted by BitLocker unless you turn off Bitlocker for the drive and turn on BitLocker for it again.
Note: You must be signed in as an Administrator to be able to choose drive encryption method and cipher strength.
Open the Local Group Policy Editor and on the left pane of Local Group Policy Editor, navigate to the following location:
Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption.
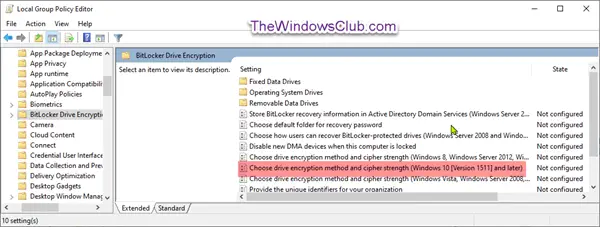
On the right pane of BitLocker Drive Encryption, double-click Choose drive encryption method and cipher strength (Windows 10 (Version 1511) and later) policy to edit it.
This policy setting allows you to configure the algorithm and cipher strength used by BitLocker Drive Encryption. This policy setting is applied when you turn on BitLocker. Changing the encryption method has no effect if the drive is already encrypted, or if encryption is in progress.
If you enable this policy setting you will be able to configure an encryption algorithm and key cipher strength for fixed data drives, operating system drives, and removable data drives individually. For fixed and operating system drives, we recommend that you use the XTS-AES algorithm. For removable drives, you should use AES-CBC 128-bit or AES-CBC 256-bit if the drive will be used in other devices that are not running Windows 10 (Version 1511).
If you disable or do not configure this policy setting, BitLocker will use AES with the same bit strength (128-bit or 256-bit) as the “Choose drive encryption method and cipher strength (Windows Vista, Windows Server 2008, Windows 7)” and “Choose drive encryption method and cipher strength” policy settings (in that order), if they are set. If none of the policies are set, BitLocker will use the default encryption method of XTS-AES 128-bit or the encryption method specified by the setup script.”
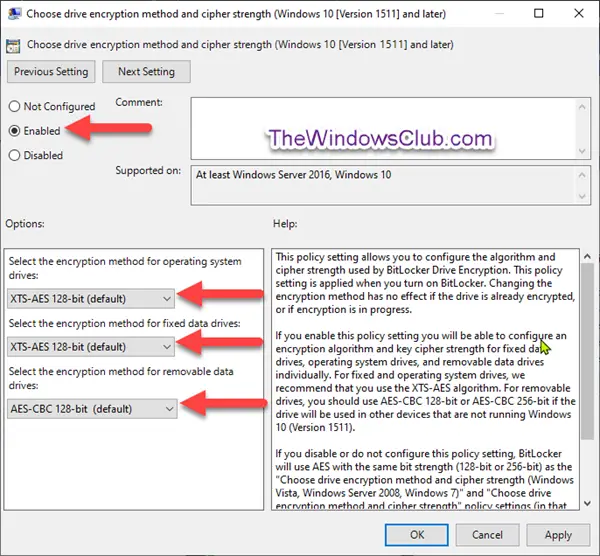
As shown in the screenshot above, do the following;
To Use Default BitLocker Drive Encryption Method and Cipher Strength
- Select the radio button for Not Configured or Disabled, click OK. You can now exit the Group Policy editor.
To Choose BitLocker Drive Encryption Method and Cipher Strength
- Select the radio button for Enabled, select the encryption method you want for operating system drives, fixed data drives, and removable data drives, click OK.
You can now exit Group Policy Editor.
How to enable 256-bit Bitlocker encryption in Windows 11?
BitLocker supports 256-bit encryption. By default, it uses AES with a 128-bit key, but you can configure it to use AES-256 for enhanced security through Group Policy settings as explained in this post. This option provides a higher level of encryption strength.
How do I check for AES 256 encryption?
To check for AES-256 encryption, examine the software or service documentation for encryption standards. Look for ‘256-bit encryption’ in security settings or contact customer support. For files, use cryptographic tools that confirm encryption algorithms, like OpenSSL commands. Always ensure you’re using a trusted, updated platform for accurately verifying AES-256 encryption.
How do I enable full disk encryption in Windows?
To enable full disk encryption in Windows, access your system settings by clicking the Start button and navigating to Settings > Update & Security > Device encryption. If the Device encryption option is visible, click “Turn on” to activate it. Ensure your Windows version supports this feature, as it may not be available on all editions.
BitLocker Drive Encryption is only available in Windows Pro, Windows Enterprise, and Windows Education editions.
Leave a Reply