As scores of people and corporations are lining up their devices on their individual networks, the volume of personal and confidential information shared on it has grown to an all-time high. In the pursuit of this information, attackers have taken a renewed interest in exfiltration from both individual and corporate environments. This, in turn, has widened the scope of organizations vulnerable to malware-driven cybercrime. That is, in addition to banks and credit unions that are subject to online banking fraud, other organizations that are susceptible to financial fraud include,
- Insurance companies
- Payment services
- Large e-commerce companies
- Airlines
Moreover, the anatomy of attack has grown more cohesive, and its distribution has become even more organized. Developers of the crimeware benefit from the sale or the lease of the crimeware to third parties who use it to perpetrate identity threats and account fraud. Today, the malware industry supplies all the components cybercriminals require to perpetrate malware-driven crimes like data theft, financial fraud, etc.
Computer Malware Industry
(Image courtesy IBM software ebook)
There are multiple variants of malware being discovered daily in the wild, capable of exploiting zero-day vulnerabilities. Some of them are designed with polymorphic capabilities. The technique circumvents signature-based detections and changes the filename on each subsequent infection to escape detection. This post looks at the two recent forms – Ransomware & Cryptojacking.
Ransomware
In simplest terms, Ransomware is a type of malware that prevents or limits users from accessing their system, either by locking the system’s screen or by locking the users’ files unless a ransom is paid. It has been around for several years but has assumed more importance now in the past couple of years.
One factor that can be attributed to the rise of this genus of malware is the expansion of the cryptocurrencies like Bitcoin. The modus operandi involves gaining access to a user’s device first, encrypting important documents/files with a key only known to the attacker. Then, demanding the transfer of funds through a currency such as Bitcoin or Moneypak in exchange for the decryption of the files. In all this, the attacker places a time limit on the user to comply with the attacker’s demands, following which all files are permanently deleted and, therefore, become untraceable and unrecoverable. Unfortunately, the most effective defense against these ransomware attacks, as with purely destructive malware, is regular, frequent backups of systems. Without a backup of a compromised system, the asset owner is at the mercy of the attacker.
Cryptojacking
Similarly, a new form of malware has emerged through malicious websites that exploit the process of “mining” cryptocurrencies using the processing power on the victim’s computer. It’s called Cryptojacking. It’s a relatively new technique that has taken off in recent months and is more advanced since it can generate money from victims without ever delivering malware to their systems.
What makes malware industry a billion-dollar industry?
With the growing influence of the Internet on the daily lives of people, commerce has shifted substantially from traditional business to online platform. As a result, consumers are purchasing and selling online at a rapid pace, while revealing their personal data and financial information across the wires. Because of this, the Internet, like other businesses, has established itself as a standard commercial business but has also become a breeding ground for crime. Nearly a third of users click on links in spam messages or malvertisements, slipping into large mainstream web pages. Of these, one in ten users is known to have purchased products advertised on these pages. The fact that users continue to make purchases makes it an attractive business. The spammers even have their own trade associations.
Malware is widely available for purchase, therefore providing a profitable way for criminals to commit cybercrime.
Many individuals, particularly youngsters, get lured into this dirty business owing to rich rewards obtained for stealing various types of information. A few examples are listed below.
| TYPES OF STOLEN INFORMATION | PRICE IN $ |
| Full identity information | $ 200 |
| Rich bank account credentials | $ 1000 |
| US Passport information | $ 1000 |
| US Social Security number | $ 100 |
These approximate prices may fluctuate in the marketplace depending on supply and demand criteria.
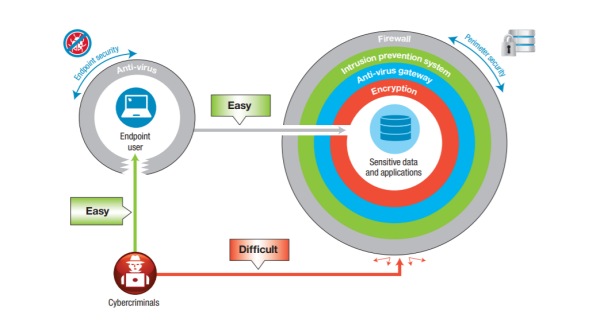
It’s often observed that most attacks don’t target the organization’s systems but rather the customer and employee endpoints. Why so? The reason behind this is that organizations invest substantially in multiple layers of security, such as-
- Firewalls
- Intrusion prevention systems
- Anti-virus gateways
In an attempt to filter out cybercriminals on the perimeter. On the other hand, for endpoint security, organizations have anti-virus software in place which often detects less than 40 percent of financial malware. As such, cybercriminals conduct malware-driven cybercrime, utilizing malware on user endpoints to commit financial fraud and steal sensitive data.
Also, if you know, the malware industry mainly runs Spam or Phishing malware which paid professional programmers write. At times, spam vendors even employ professional linguists to bypass filters and psychology graduates to spam victims. There’s no dearth of money! Talented employees can earn in the range of $200,000 plus, per year. It gets even more rewarding for remote root zero-days – $ 50-100,000.
Even the workload is smartly distributed. For instance, outsourcing the anti-detection code allows malware authors to concentrate on the payload.
Cyber-dacoity is on the rise and will reach gigantic proportions as time passes by!