Microsoft has now made it possible for you to add protection against Potentially Unwanted Programs (PUPs) or Potentially Unwanted Applications (PUA) to your Windows Defender on Windows 11/10. You need to edit the Group Policy, Registry or use PowerShell.
This feature has been announced by Microsoft exclusively for Enterprise users only, but with a little bit of work, you can make it work on your Windows 11/10 PCs too.
The Potentially Unwanted Application protection feature is available only for enterprise customers. If you are already one of Microsoft’s existing enterprise customers, you need to opt-in to enable and use PUA protection. PUA protection updates are included as part of the existing definition updates and cloud protection for Microsoft’s enterprise customers, says Microsoft.
Potential Unwanted Application (PUA) or PUPs is a threat classification based on reputation and research-driven identification. They are typically Crapware or Bundleware, and such software that you really do not want on your system, and which could potentially do more harm than good. You can protect yourself from PUA or PUPs by deploying an antimalware policy. This protection policy setting is disabled by default.
Read: Windows will block Unwanted Software based on these criteria.
Turn On Potentially Unwanted Programs Protection in Windows 11/10
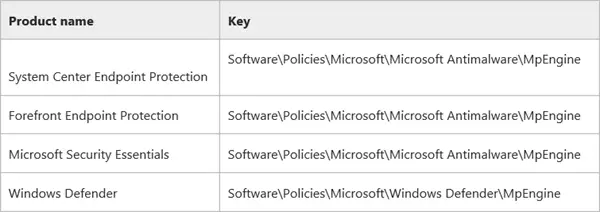
To do this, you will have to modify the Windows Registry. The registry key varies according to your product version, and is different for System Center Endpoint Protection, Forefront Endpoint Protection, Microsoft Security Essentials or Windows Defender, as shown in the above image.
PUA protection will quarantine the PUP file and prevent them from running if it meets one of the following conditions:
- The file is being scanned from the browser
- The file has Mark of the Web set
- The file is in the %downloads% folder
- Or if the file in the %temp% folder.
Before you begin, you should know that Windows 10 now allows you to disable or enable protection against Potentially Unwanted Applications (PUA) using Windows Security.
Using Group Policy
- Open gpedit.msc and navigate to the following setting:
- Computer configuration > Administrative templates > Windows components > Windows Defender Antivirus.
- Double-click Configure protection for potentially unwanted applications.
- Select Enabled to enable PUA protection.
- In Options, select Block to block potentially unwanted applications, or select Audit Mode to test how the setting will work in your environment.
- Select OK.
Restart your system.
Using Registry
To make Windows Defender protect you against Potentially Unwanted Programs, Run regedit to open the Registry Editor and navigate to the following key:
HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows Defender
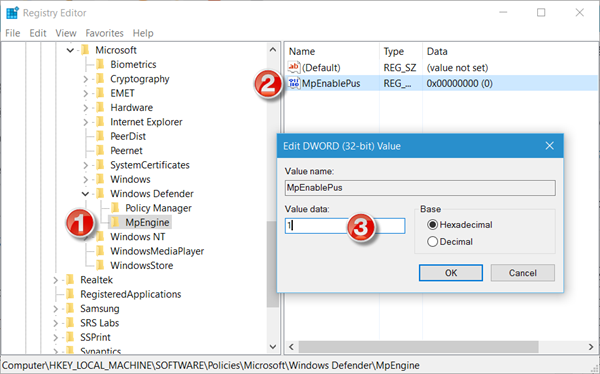
Here, right-click on Windows Defender and select New > Key > Name it MpEngine.
Now right-click on MpEngine and select New > DWORD (32-bit) Value > Name it MpEnablePus and give it a value 1.
- With a value of 0 which is the default, Potentially Unwanted Application protection is disabled
- With a value of 1 Potentially Unwanted Application protection is enabled. The applications with unwanted behavior will be blocked at download and install-time.
Restart your Windows computer.
Using PowerShell
You can also use a PowerShell cmdlet to configure the PUA protection feature. Use the following command:
Set-MpPreference -PUAProtection <PUAProtectionType>
Options for <PUAProtectionType>:
- Set the value for this cmdlet to Enabled to turn the feature on.
- Set it to AuditMode to only detect but not block the PUAs.
- Set it to Disabled to turn off PUA protection,
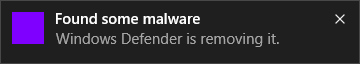
In Windows 10, the following dialog box will be displayed, when a PUP file is blocked:
If you wish to make sure the PUA feature has been enabled and is working properly, you may visit amtso.org click on the Download the Potentially Unwanted Application test file link, and check if it is automatically blocked from being downloaded or run.
You can manage Quarantined items and remove or restore files from Quarantine in Windows Defender.
TIP: If you think that a program developed by you has been wrongfully identified as PUA, you can submit the file here.
Related read: Enable Potentially Unwanted Application (PUA) protection in Edge browser.
This post shows how you can harden Windows Defender protection to the highest levels on Windows by changing a few Group Policy settings.
