Microarchitectural Data Sampling (MDS) is a CPU side vulnerability. According to Intel, its CPU has some loose points that can be exploited by hackers. This means taking control of the CPU to be able to read very short term data stored in CPU internal buffers. Let’s see how it works. We will also tell me how to find out if your system is affected from this ZombieLoad exploit.
MDS – Microarchitectural Data Sampling
Modern Intel processors employ data storage in its internal buffers, the data being sent to and from the processor’s cache. The internal buffers of processors are used to cut compute time. For this saving of processor time, data from processors is first stored in internal memory built into a processor like Intel. The data is of the format: TIME, DATA, and IF_VALID columns. It is to make sure if a piece of data is still valid at a given time. This is transferred to CPU cache for use with other firmware or any other software on the computer.
The microarchitectural data sampling (MDS) vulnerability is a method whereby hackers steal data from processor’s ultra-small buffers in real time. In each computer session, data is stored with filters (TIME, DATA, IF_VALID) into these mini-caches. They keep changing very fast that by the time it is stolen, its value (validity too) changes. Still, hackers can use the data even if the data inside processor filters/memory changes, allowing them to take control of the machine completely. It is not evident. Problems begin when the hacker obtains any encryption key or any other useful data from the mini buffers in the processor.
To rephrase the above, hackers can collect data even though the life of data stored is extremely short. As said earlier, data keeps on changing, so hackers have to be quick.
Risks from Microarchitectural Data Sampling (MDS)
Microarchitectural Data Sampling (MDS) might give away encryption keys and thereby gain control over files and folders. MDS might give away passwords too. If compromised, the computer can be bricked like in case of Ransomware.
Malicious actors can extract data from other programs and apps once they break into the processor memory. Obtaining the RAM data is not difficult once they have the encryption keys. Hackers use maliciously designed web pages or programs to gain access over processor information.
Worst of all is the inability of a compromised computer, not knowing that it has been compromised. MDS attack won’t leave anything in the log and doesn’t leave any footprint anywhere on the computer, or network, so chances of anyone detecting it are very less.
Types of MDS vulnerabilities
As of now, four variants of the microarchitecture are detected:
- Microarchitectural Load Port Data Sampling
- Microarchitectural Store Buffer Data Sampling
- Microarchitectural Fill Buffer Data Sampling, and
- Microarchitectural Data Sampling Uncacheable Sampling
This was the longest (one year) period for which a vulnerability was found and kept as a secret until all operating system manufacturers and others could develop a patch for their users.
Some users questioned why can’t they simply disable hyperthreading to protect against MDS. The answer is the disabling hyperthreading does not provide any kind of protection. Disabling hyperthreading will make the computers slow. Newer hardware is being built to counter the possible MDS attacks.
Is your computer vulnerable to MDS?
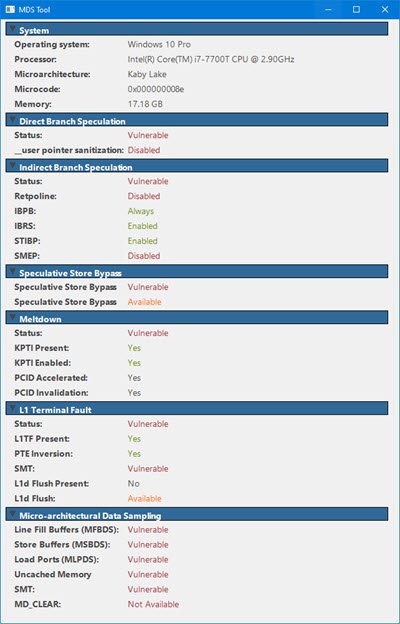
Verify whether your system is vulnerable. Download the MDS Tool from mdsattacks.com. You will get a lot of other information there.
How to protect computers from MDS?
Almost all operating systems have issued a patch which should be used in addition to the Intel microcode to keep the vulnerability away. On Windows OS, the Tuesday updates are said to have patched most computers. This, along with the Intel code that is being built into the operating system patches, should be sufficient to prevent microarchitectural sampling (MDS) from compromising your computers.
MDSAttacks website recommends disabling Simultaneous Multi-Threading (SMT), also known as Intel Hyper-Threading Technology, which significantly reduces the impact of MDS-based attacks without the cost of more complex mitigations. Intel has also provided CPU microcode updates, and recommendations for mitigation strategies for operating system (and hypervisor) software. We recommend you install the software updates provided by your operating system and/or hypervisor vendor.
Keep your computer(s) updated. Update your BIOS and download the latest device driver for your processor from the Intel website.
This vulnerability has been patched by Microsoft for their Windows line of operating systems. macOS too received a patch on May 15th, 2019. Linux has prepared the patches but needs to be downloaded separately for Microarchitecture Data Sampling (MDS).
Leave a Reply