Imagine … The FBI checked your computer and browsing traffic. It now has details of all sites you visited and what you did using your computer. And it knows more laws than you ever thought existed. When you open your browser, instead of your homepage, you get a notice from the FBI saying you violated so and so laws. Further, you have to pay a fine of $350 to avoid jail. That does look genuine, right? It is not, however. It is just the FBI Ransomware that is still doing rounds, and you can do little to remove the ransomware virus. I managed to get a copy of the browser screen lock of the FBI malware. Click on the image below to enlarge it.
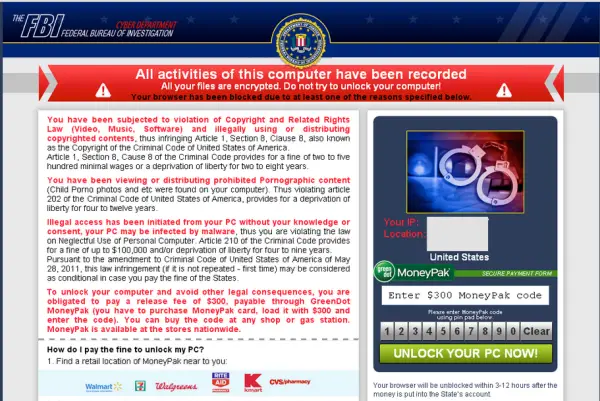
FBI Ransomware
The ransomware has had many preys. It has been successful in getting people to pay up the $350 it demands as fine for your supposedly “illegal” browsing habits. And, it does not stop there. It demands an additional fee of $450 to remove your “criminal” records from its database so that you are not fined again. What would you do in such circumstances? Panic, and pay off the additional money too?
Many have done that, and many will continue to do so until it occurs to them that they could get a confirmation from the local police station that the FBI is indeed asking for criminal browsing and record deletion fee. Else, simply write to the FBI asking you got such a message and ask whether it is indeed true.
How to Identify Ransomware
Ransomware and phishing malware have always counted on the fear of law and society within individuals. You might have noticed you get mail from Microsoft, Yahoo, and other biggies in your Outlook that promise you direct placements. When you take a closer look at the email ID, it has nothing to do with the companies and thus, reveals that it is a phishing attempt.
For example, I often receive emails from different subdomains of wisdomjobs.com with names of bigger corporations: [email protected] is not Microsoft and can NEVER be as Microsoft has its own widely used domain called microsoft.com. Likewise, something like [email protected] will NEVER be PayPal as the main domain is not PayPal as evident from the email ID.
In the case of FBI ransomware, you can just check the address in the browser’s address bar. Find out the last word just before .com/.net/.org etc. You will notice that the first two subdomains are FBI and GOV while the others are different domains that are not even remotely related to – forget FBI, – any of the federal or state agencies.
Who is Behind FBI Ransomware
The cybercrime cell is investigating from what I know. What makes it hard is that it won’t accept the general methods of paying by credit cards directly to the agency or state units. You pay to different accounts and in most cases, you have to pay the money in parts. That is, you paid $350 to account number XYZ, $200 to acct number ABC, and the balance to another account. All these accounts are fake and are emptied, closed as soon as money is transferred. Thus, the scope of narrowing down the search of this FBI ransomware racket/gang goes down. As of now, no one except the people involved in running the gang, know about who is operating it. Whoever it is, the person is pretty smart to keep the cyber police on their toes.
Remove FBI Ransomware
As of now, the only sure-shot method to eliminate the FBI ransomware virus is to clean format your system drive and reinstall the operating system. That done, increase your Firewall protection by using a hardware firewall as far as possible. These days, all modems and routers come with firewall firmware. Log into your router/modem page and enable the firewall. You may then decide whether or not to use an additional software firewall.
I am told using image backups of the system does not work. That is, if you are infected with this malware and you go restore an older system image, it does not provide any relief. If you have heard or used any effective method to eliminate the FBI ransomware virus, please share with us for the benefit of all.
HitmanPro.Alert is a free Ransomware Protection & Browser Intrusion Detection Tool. CryptoPrevent is another handy tool that provides your computer a shield against Cryptolocker or any other kind of ransomware. Anvi Rescue Disk for Windows will assist in ransomware removal. HitmanPro.Kickstart will help remove Ransomware.
