Cryptojacking or malicious cryptomining is a new trick used to mine Cryptocurrencies on a user’s computer using their CPU resources in the background without their knowledge. Typically, the cybercriminal loads a script into the victim’s web browser, which contains a unique site key to force the user to enrich them.
If you are struggling with a slow PC or internet connection, do not just blame the vendor or service provider because you may be a victim of a new trick used by hackers called Browser Cryptojacking.
The evolution of Cryptojacking is attributed to the soaring interest in Cryptocurrencies for the past few months. Look at Bitcoin for the past few months or so, and its value has gone up by more than 1,000%. This has attracted attention from hackers as well and so has given birth to dangerous practices such as Crytptojacking.
What is Cryptojacking
Emergence
Before we understand what Cryptojacking is, first let us know about Cryptomining.
Cryptomining or Cryptocurrency Mining is the process by which a cryptocurrency comes into existence using blockchain technology. Cryptomining also lets new cryptocurrency coins get released on the market. Mining is carried out by certain peers of the cryptocurrency network who compete (individually or in groups) in solving a difficult mathematical problem called proof-of-work
In September 2017, Coinhive debuted in the market, offering to mine the cryptocurrency called Monero (XMR). Coinhive offers a piece of code written in JavaScript, which website owners can simply embed on their website. Coinhive introduced a new business model for its website, claiming that website owners can remove ads from their websites and load Coinhive instead.
When users access a website with Coinhive embedded, Coinhive initiates the process of crypto mining on behalf of the website owner by using user system resources (that is why PCs often become slow). The visitors to the website represent the group of nodes doing intensive computational work to solve the mathematical problem. However, instead of them receiving the reward when solving the challenge, the website owner receives it. Hence, website owners can supposedly still make a profit and support their businesses, without supposedly bothering their visitors with advertisements.
Although Coinhive was meant to be legitimate, its concept led to the emergence of similar software, which is now used by cyber criminals for Cryptomining abuse or Cryptojacking.
In short, Cryptojacking is the technique of hijacking browsers for mining cryptocurrency without user consent. Delivering cryptocurrency miners through malware is a known fact, but mining cryptocurrency when accessing a webpage is new and has led to attackers abusing for personal gains.
Cryptojacking is not a traditional malware
Cryptojacking does not harm your PC like traditional malware or ransomware act. Neither does it store or lock down anything on the hard drive. Hence, it in itself is not malware as such, but it can certainly be introduced into your system using malware.
Cryptojacking, similar to malware, uses your PC resources without your permission. It can cause the PC and browsers to work extremely sluggish, drain the battery and raise the electricity bills without you even realizing the same.
Consequences of Cryptojacking
Cryptojacking can affect Windows OS as well as Mac OSX & Android. There have been numerous cases of Cryptojacking reported recently. Some of the common types include the following:
Websites using Coinhive deliberately
Pirates Bay was one of the first major player guilty of using Coinhive deliberately. The issue was that it was done transparently, without the visitors’ consent. Once the crypto mining script was discovered, Pirate Bay issued a statement mentioning that it was testing this solution as an alternative revenue source. Researchers fear that there are many such websites which are already using Coinhive without visitor’s consent.
Coinhive injected into compromised websites
Researchers identified compromised WordPress and Magento websites that had Coinhive or a similar JavaScript-based miner injected into them.
Read: What to do if Coinhive crypto-mining script infects your website.
Cryptojacking using browser extensions
In-browser cryptojacking uses JavaScript on a web page to mine for cryptocurrencies. JavaScript runs on just about every website you visit, so the JavaScript code responsible for in-browser mining does not need to be installed. As soon as you load the page, and the in-browser mining code just runs.
There are cases of web browser extensions embedding Coinhive where cryptomining software run in the background and mined “Monero” while the browser was running -and not only when visiting a specific website.
Cryptojacking with malware
This is another type of abuse where Coinhive is being deployed alongside malware through a fake Java update.
Cryptojacking in Android devices
An Android variant of Coinhive has been detected targeting Russian users. This trend suggests that Cryptojacking is expanding to mobile applications as well.
Typosquatted domains embedding Coinhive
Someone registered the “twitter.com.com” domain and loaded Coinhive to it. Essentially, users who mistyped Twitter’s URL and landed on that webpage would mine Monero for the domain owner for as long as they remained at the webpage.
Cryptojacking through cloud services
Cybercriminals are hijacking unsecured Cloud platforms and using them to mine cryptocurrency.
Microsoft has notified of variations of Coinhive being spotted in the wild. Such a development indicates that Coinhive’s success has motivated the emergence of similar software by other parties that want to join this market.
Minr – A Coinhive alternative emerges
The use of Coinhive by legitimate users has, in general, been on decline owing to the unpopularity that it has been receiving since its launch. Coinhive is also easily traceable, which is another fact that its prospective admirers are not using it on their website.
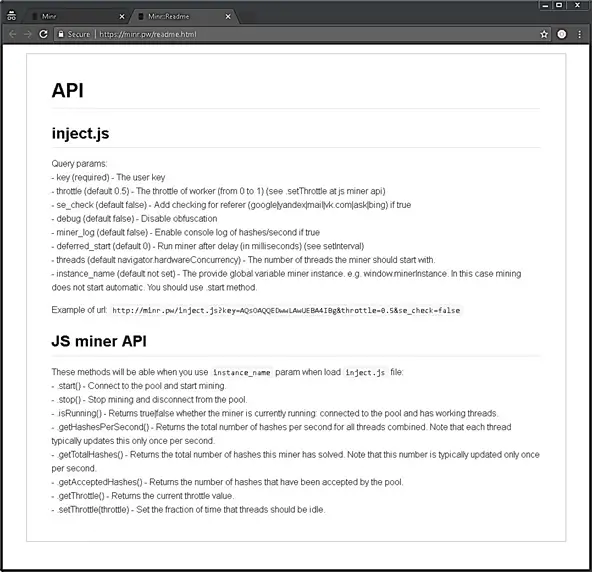
So, as an alternative, the team Minr, has developed an option of “obfuscation”, which makes it much more difficult to track the miner. This facilitates the hidden use of the tool. This feature is so effective that it hides the code even for the popular anti-malware tool Malwarebytes.
How to stay protected from Cryptojacking
Cryptocurrencies & Blockchain technology is taking over the world. It is impacting the global economy and causing technology disruptions as well. Everyone has started focusing on such a lucrative market – and this includes website hackers too. As returns increase, we should expect that such technologies will be misused.
Being observant while browsing is something that you have to practice regularly if you want to stay away from Cryptojacking frauds. You are on a compromised website if you see a sudden spike in memory usage and sluggish performance on your PC. The best action here is to stop the process by exiting the website and not visiting it again.
You should also install a good security software and keep it updated, as well as turn on firewalls and not click on suspicious links while browsing.
You can use Anti-WebMiner programs as one of the precautions.
Use a browser extension that blocks websites from using your CPU for crypto mining. If you use Chrome browser, then Install minerBlock extension. It is a useful extension for the Chrome browser to block web-based cryptocurrency miners all over the web. Apart from CoinHive it even blocks Minr.
Another necessary precaution is to update your Hosts file to block coinhive.com and other domains that are known to enable unauthorized mining. Remember, Cryptojacking is still growing, with more and more people drawing towards Cryptocurrencies, so your blocklists will have to be regularly updated.
Prevent CoinHive from infecting your website
- Don’t use any NULL templates or plugins on your website/forum.
- Keep your CMS updated to the latest version.
- Update your hosting software regularly (PHP, Database, etc.).
- Secure your website with web security providers like Sucuri, Cloudflare, Wordfence, etc.
- Take basic precautions to secure your blog.
Stay alert, stay safe!
