Protecting sensitive data should always be an important aspect of every operating system, and this is something Microsoft knows very well. The company has done a wonderful job with Windows OS to address most concerns where security is concerned, and Windows Information Protection is a big part of it. We should point out that this protection suite contains the likes of Windows Information Protection, Azure Information Protection, and Microsoft Cloud App Security.
Here’s the thing, Windows Information Protection, otherwise known as WIP, is well endowed to protect automatically classified files via the sensitive information types feature. It takes full advantage of Windows Defender ATP, but bear in mind the latest improvements are only available in Windows 10 1903 and later.
Configure WIP
Before we go forward, wed like to talk about how to configure Windows Information Protection. It’s quite easy and straight to the point, so let’s get things up and running for your pleasure.
OK, so the first thing the user needs to do is to visit manage.microsoft.com via their web browser and log-in with a Windows Intune administrative account. After that, the user should see a navigation pane on the left and select the option that says Policies.
- Login to microsoft.com, and make sure to do it with your Windows Intune administrative account.
- From the left pane, select the option that says Policies.
- From within the window, users should see Add Policy. Please click on that to move forward.
- Folks should now see a dialog known as Create a New Policy, then move ahead to expand Windows, then make sure to select Windows Information Protection.
- Finally, click on Create and Deploy a Custom Policy.
- The next step, then, is to click on Create Policy
- Be sure to enter a name for the policy
- Enter the description and specify App Rules if that’s your thing.
That’s it right there for configuring WIP. As you can tell, the task is quite easy, especially for those who know their way around a computer.
Protect sensitivity labels with Endpoint Data Loss Prevention
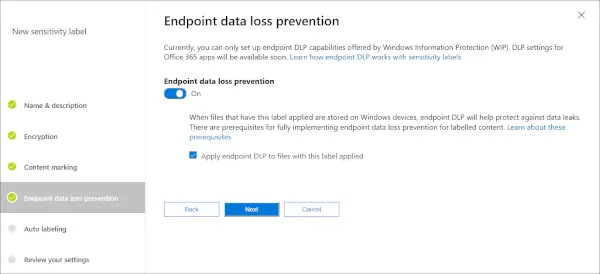
When it comes down to managing sensitivity labels, this can be done in the Microsoft 365 compliance center with relative ease.
For those who were not aware, Windows Defender is capable of extracting a file to check if it has been contaminated with a virus or malware. It can also check if a file contains sensitive information such as credit card numbers or other types of important data.
The default sensitive information types include credit card numbers, phone numbers, driver’s license numbers, and more. However, what’s interesting here is the ability for users to set custom sensitive information types should they wish to do so.
Windows Information Protection
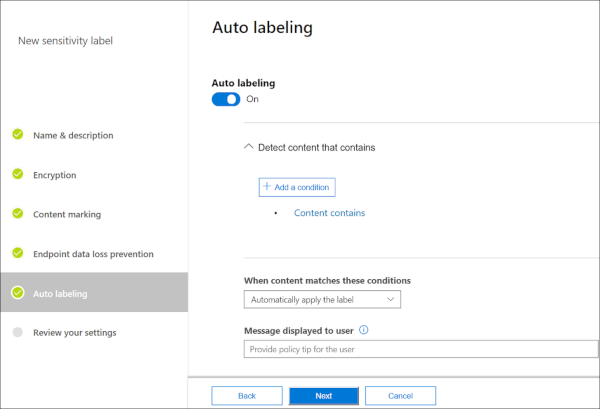
Whenever the user creates or edits a file on Windows 10 endpoint, the content is promptly extracted an evaluated by Windows Defender ATP. It will then check the files for any defined sensitive information types.
Now, if the files have a match, Windows Defender ATP will then proceed to apply endpoint data loss prevention.
It should be noted that Windows Defender ATP is integrated with Microsoft Azure Information Protection, a feature that was designed primarily for data discovery. It can also report sensitive data types that were recently discovered.
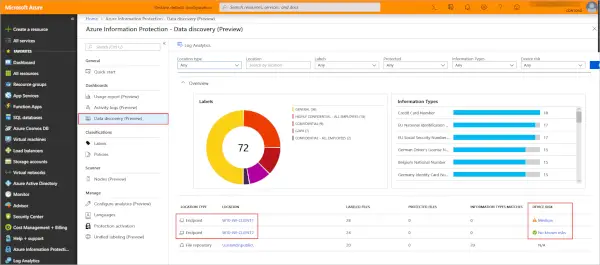
For those who want to see the sensitive information types, we suggest checking under Classifications via Microsoft Office 365 compliance. Bear in mind that all default sensitive information types have Microsoft as the publisher. When it comes down to custom types, they will be attached to the name of the tenant.
UPDATE: This has been retired now.
Windows Information Protection, previously known as Enterprise Data Protection (EDP), was originally released to help organizations protect enterprise apps and data against accidental data leaks without interfering with the employee experience on Windows. Over time, many of you have expressed a need for a data protection solution that works across heterogenous platforms, and that allows you to extend the same sensitive data protection controls on endpoints that you have for the various SaaS apps and services you rely upon every day. To address these needs, Microsoft has built Microsoft Purview Data Loss Prevention (DLP), which is deeply integrated with Microsoft Purview Information Protection to help your organization discover, classify, and protect sensitive information as it is used or shared.
Hope this helps.
