Unlike other cosmetic changes introduced in Windows, Firewall & Network Protection has been the focus of attention. Network Protection, as you are aware helps reduce the attack surface of your devices from Internet-based events. It prevents employees from using any application to access malicious domains that may be hosting phishing scams or exploits on the Internet and expands the scope of SmartScreen to block all outbound HTTP(s) traffic that attempts to connect to low-reputation sources. Let us take a look at the Network Protection feature which is a part of Exploit Guard feature in Windows Defender.
Network Protection feature in Windows Defender
Network Protection is part of Windows Defender Exploit Guard which helps in offering protection against multiple host intrusion incidents. It has some unique built-in prevention capabilities that allow it to manage and minimize the attacks.
In the event where Network protection blocks a connection, a notification is displayed for your view in the Action Center, waiting for the action to be taken against it. If necessary, you can modify the notification with your company details and contact information. Also, you can switch to audit mode to evaluate how Network protection would impact your organization if it were enabled.
Currently, you can enable Network Protection feature in Windows 10 using-
- Group Policy
- PowerShell
You can use the following PowerShell command to enable or disable Network Protection on your computer:
To enable Network Protection, run:
Set-MpPreference -EnableNetworkProtection Enabled
To enable the feature in audit mode use the following cmdlet:
Set-MpPreference -EnableNetworkProtection AuditMode
To disable Network Protection, run:
Set-MpPreference -EnableNetworkProtection Disabled
You can review Network Protection events in Windows Event Viewer when Network Protection blocks (or audits) access to a malicious IP or domain. To do this, you will have to make use of the Exploit Guard Evaluation Package which you can download from Microsoft and extract the file np-events.xml to a readily accessible location on the system.
How do I enable network protection in Windows 11?
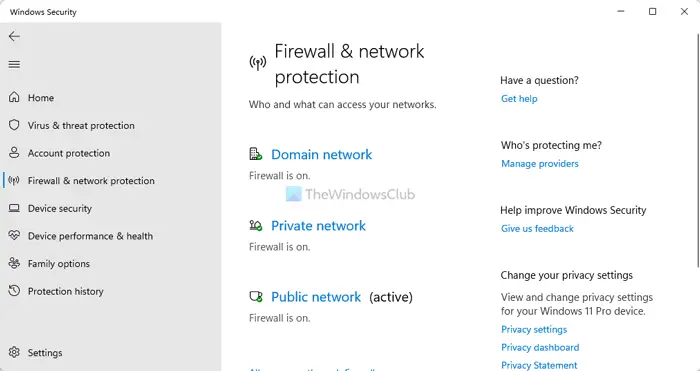
To enable or turn on Network protection in Windows 11, you can open Windows Security itself. You can search for windows security in the Taskbar search box and click on the individual search result to open the app. Then, switch to the Firewall & network protection tab on the left side. If it says Firewall is on, network protection is enabled on your computer.
Does Windows 11 support Windows Defender?
Yes, Windows 11 supports Windows Defender. However, Microsoft has renamed this security tool, and now it is called Windows Security. You do not need to download or install anything to get Windows Security on Windows 11. You can search for windows security in the Taskbar search bar and open the respective search result.
For full details, you may visit docs.microsoft.com.
