Veracrypt entered the market within months after Truecrypt died. Veracrypt, a Truecrypt alternative, is also an open-source project and file encryption software, is built upon the code of Truecrypt, but with enhancements to further secure your data. You can use it to encrypt single files, folders or entire drives simultaneously. This Veracrypt review does not discuss its usage, as the usage of Veracrypt is not much different than Truecrypt. It is more about the advantages of Veracrypt over Truecrypt.
VeraCrypt disk encryption software for Windows PC
Encrypting and Using Veracrypt
The methods are the same as the Truecrypt: you can create individual file containers and mount them as drives so that you can keep your files encrypted. A container is actually a place that when mounted as a drive using the main screen of Veracrypt, offers encryption to the contents of the virtual drive. Suppose you create a file container using the application’s wizard to create a container and then use the main page of the app to mount it as a drive, you can copy or move files to that drive. As soon as you copy or move your files to that drive, they are encrypted.
You can also use Veracrypt for flash drives. You can encrypt entire flash drives or create a container on Flash drives. In the latter case, where you create a container, you have to mount it as a separate volume every time you connect the flash drive to your computer.
Encryption and Decryption in Veracrypt
You can use files from containers directly when you use Veracrypt. When the file is accessed by other apps, parts of the files are decrypted using the key you create while encrypting the drive or while creating the container. These files are not decrypted in whole at a time as it would appear. Rather, as said by Veracrypt on their website, only the portion of the file you are working on, is decrypted and placed in RAM for use by processor and user. When you move to another portion of the file, that particular portion is decrypted and later encrypted again after writing changes to the disk.
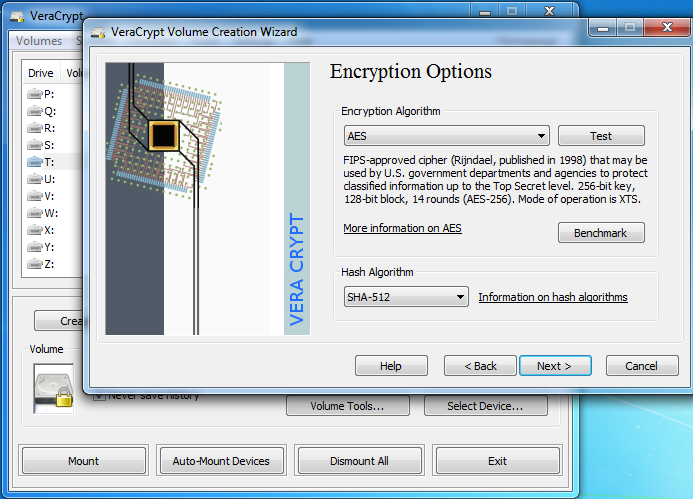
Encryption is many times stronger than Truecrypt and the makers of Veracrypt say that though built upon Truecrypt code, it has eliminated the negatives of Truecrypt to make a very powerful encrypting tool. Here is an excerpt from their homepage:
As an example, when the system partition is encrypted, TrueCrypt uses PBKDF2-RIPEMD160 with 1000 iterations whereas in VeraCrypt we use 327661. And for standard containers and other partitions, TrueCrypt uses at most 2000 iterations but VeraCrypt uses 655331 for RIPEMD160 and 500000 iterations for SHA-2 and Whirlpool.
This enhanced security adds some delay only to the opening of encrypted partitions without any performance impact to the application use phase. This is acceptable to the legitimate owner but it makes it much harder for an attacker to gain access to the encrypted data.”
Interface of Veracrypt
It would be hard for a first-time user to make out how to use the tool. The interface is neat but is not self-explanatory. One needs to read the online documentation if not already familiar with the technical terms used by the Veracrypt encryption tool in its interface. Especially, while creating a container, I got confused if hitting “Format” would create a container or format my drive. I had to consult the online documentation before proceeding. The Documentation is good with plenty of screenshots and things are explained in an easy-to-understand method.
Verdict
Veracrypt is easy to use for people with good knowledge of encryption tools. Otherwise, people have to refer to the documentation for help, which is ample and then, it is easy to use. The security provided by Veracrypt is good and many times higher than that of Truecrypt. It also lets you mount TrueCrypt volumes.
The tool is highly recommended over Truecrypt as the latter has its own weaknesses. I made a switch from Truecrypt to Veracrypt for two reasons: 1) The security is better and 2) the whole thing is free to use and can be verified as it is open source. Though I am not into coding, I can say it is safe as there have been no visible complaints by other coders as of the date of writing this article.
Download it from the Veracrypt homepage.
Check out some more free TrueCrypt alternatives like AESCrypt, FreeOTFE and DiskCryptor, and let us know which you think is the best.