Protecting our data online will never be easy, especially nowadays when attackers are regularly inventing new techniques and exploits to steal your data. Sometimes their attacks will not be so harmful to individual users. But large-scale attacks on some popular websites or financial databases could be highly dangerous. In most cases, the attackers first try to push some malware onto the user’s machine. Sometimes this technique doesn’t work out, however.
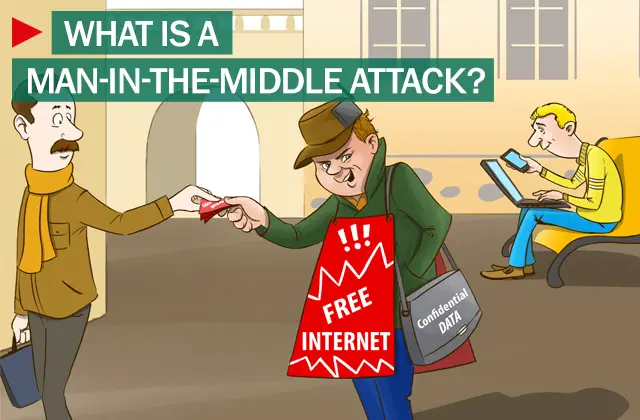
Image source: Kaspersky.
What is Man-In-The-Middle Attack
A popular method is Man-In-The-Middle attack. It is also known as a bucket brigade attack, or sometimes Janus attack in cryptography. As its name suggests, the attacker keeps himself/herself between two parties, making them believe that they are talking directly to each other over a private connection, when actually the entire conversation is being controlled by the attacker.
A man-in-the-middle attack can be successful only when the attacker forms a mutual authentication between two parties. Most cryptographic protocols always provide some form of endpoint authentication, specifically to block MITM attacks on users. Secure Sockets Layer (SSL) protocol is always being used to authenticate one or both parties using a mutually trusted certification authority.
What is the goal of a MITM attack?
The goal of a Man-in-the-Middle (MITM) attack is to eavesdrop on or alter communications between two parties to steal sensitive information, such as login credentials or banking details. Attackers may also manipulate the communication to redirect funds or convince victims to change security settings, posing significant security risks.
How MITM works
Let’s say this story has three characters: Mike, Rob, and Alex. Mike wants to communicate with Rob. Meanwhile, Alex (attacker) inhibits the conversation to eavesdrop and carries on a false conversation with Rob, on behalf of Mike. First, Mike asks Rob for his public key. If Rob provides his key to Mike, Alex intercepts, and this is how the “man-in-the-middle attack” begins. Alex then sends a forged message to Mike that claims to be from Rob but includes Alex’s public key. Mike easily believes that the received key does belong to Rob when that’s not true. Mike innocently encrypts his message with Alex’s key and sends the converted message back to Rob.
In the most common MITM attacks, the attacker mostly uses a WiFi router to intercept the user’s communication. This technique can be worked out by exploiting a router with some malicious programs to intercept users’ sessions on the router. Here, the attacker first configures his laptop as a WiFi hotspot, choosing a name commonly used in a public area, such as an airport or coffee shop. Once a user connects to that malicious router to reach websites such as online banking sites or commerce sites, the attacker then logs a user’s credentials for later use.
Read: What is Replay Attack and how do you prevent it?
Man-in-the-middle attack prevention & tools
Most of the effective defenses against MITM can be found only on the router or server side. You won’t be having any dedicated control over the security of your transaction. Instead, you can use strong encryption between the client and the server. In this case, the server authenticates the client’s request by presenting a digital certificate, and then the only connection could be established.
Another method to prevent such MITM attacks is, to never connect to open WiFi routers directly. If you wish to do so, you can use a browser plug-in such as HTTPS Everywhere or ForceTLS. These plug-ins will help you in establishing a secure connection whenever the option is available.
Which of the following are mitigation tools for MITM attacks?
Mitigation tools for Man-in-the-Middle (MITM) attacks include using encryption protocols like SSL/TLS, implementing VPNs for secure connections, employing strong authentication methods, and regular network monitoring. Additionally, keep software updated to address vulnerabilities, use intrusion detection systems, and educate employees about phishing attacks to enhance overall security.
What is the most effective protection against Man in the middle MITM attacks?
Using encryption protocols like Transport Layer Security (TLS) is the most effective protection against Man in the Middle (MitM) attacks. TLS ensures that data exchanges remain secure by providing confidentiality, integrity, and authenticity. Implementing TLS helps prevent unauthorized interception and alteration, significantly reducing the risk of MitM attacks on your communications.
Read next: What are Man-in-the-Browser attacks?
I am not a technical person but I use technology like facebook and other internet stuffs. Couple of days ago someone hacked into my facebook account and posted something terrible. Since then I am aware of hacking and I am trying to learn some technical stuffs to protect my personal data. This article is something great to read.
One has to be very
careful on Facebook having been hacked a few times myself going to your
settings normally fixes it, however I use my cell number as a login to get back
on. You cannot just use these social sites and expect to get away scot-free,
make it private I do as do most of my family we all learnt the hard way. You always
get one that spills the beans about you publicly though sadly, It happens on Gmail
as well so get a record of your contacts on Gmail as mine was all altered when I
got back on
Actually, your prevention tips do NOT prevent a Man-in-the-Middle attack. Plugins like HTTPS-Everywhere and ForceTLS only force the use of an HTTPS/SSL/TLS connection. All HTTPS/SSL/TLS connections use a certificate issued by a third-party “certificate authority”. A Man-in-the-Middle attacker could still set up a WiFi hotspot that other computers might unknowingly connect to instead of the legitimate hotspot. The attacker would also establish their own separate HTTPS/SSL/TLS connection to the Internet through the legitimate hotspot. The attacker’s computer is the user’s HTTPS/SSL/TLS endpoint, and all Internet traffic (including certificates) is proxied to and from the user through the attacker’s computer. But meanwhile, on its way through the attacker’s computer, all traffic (including passwords, account numbers, social security numbers, etc.) passes unencrypted, as clear text, where it can be viewed, recorded, and even altered along the way.
The only completely reliable defense against MITM attacks (unless you’re a sophisticated user who has other means) is to use some kind of locally installed client software that securely “tunnels” all traffic to a previously known and trusted server, which in turn proxies all the user’s traffic out to the Internet and back. Examples are corporate VPNs, anonymous Web browsing proxy services (if they use local client software), and SSH (secure shell) tunnels that only connect to already known, trusted servers.
Public WiFi can be safe. Now you know how. Happy surfing.
I have a hacker using local MITM attacks in a number of different ways. I’m still kinda letting him lurk around tho. ;)
can someone use man in the middle on windows 10?