Windows 11/10/8 includes a new security feature called Secure Boot, which protects the Windows boot configuration and components and loads an Early Launch Anti-malware (ELAM) driver. This driver starts before other boot-start drivers, enables the evaluation of those drivers, and helps the Windows kernel decide whether they should be initialized. By being launched first by the kernel, ELAM is ensured that it is launched before any other third-party software. It is, therefore, able to detect malware in the boot process itself and prevent it from loading or initializing.
What is Early Launch Anti-Malware protection?
Windows Defender takes advantage of Early-Launch Anti-Malware, and you, therefore, see that it no longer loads after the start-up process is complete, but early on during the boot process.
Third-party antivirus software too, is able to take advantage of the ELAM technology. To do so, they will have to integrate the same Early Launch Anti-Malware (ELAM) capability in their software. To help security software vendors get started, Microsoft has released a whitepaper that provides information about developing Early Launch Anti-Malware (ELAM) drivers for Windows operating systems. It provides guidelines for anti-malware developers to develop anti-malware drivers that are initialized before other boot-start drivers, and ensure that those subsequent drivers do not contain malware. Several antivirus companies, who have released their updated solutions for Windows already incorporate this technology.
Enable or Disable Early Launch Anti-Malware (ELAM) protection
The Early Launch Antimalware boot-start driver has classified the drivers as follows:
- Good: The driver has been signed and has not been tampered with.
- Bad: The driver has been identified as malware. It is recommended that you do not allow known bad drivers to be initialized.
- Bad, but required for boot: The driver has been identified as malware, but the computer cannot successfully boot without loading this driver.
- Unknown: This driver has not been attested to by your malware detection application and has not been classified by the Early Launch Antimalware boot-start driver.
By default, Windows loads those drivers classified as Good, Unknown, and Bad but Boot Critical: ie 1, 3, and 4 above. Bad drivers are not loaded.
To disable Early Launch Anti-Malware protection, you will have to ou must disable the Configure Boot-Start Driver Initialization Policy in Windows 11/10.
Configure Boot-Start Driver Initialization Policy using Group Policy Editor
While this setting is best left at its default value, if you wish, you can change this setting via your Group Policy Editor. To do so, open the WinX menu > Run > gpedit.msc > Hit Enter. Navigate to the following policy setting:
Computer Configuration > Administrative Templates > System > Early Launch Antimalware
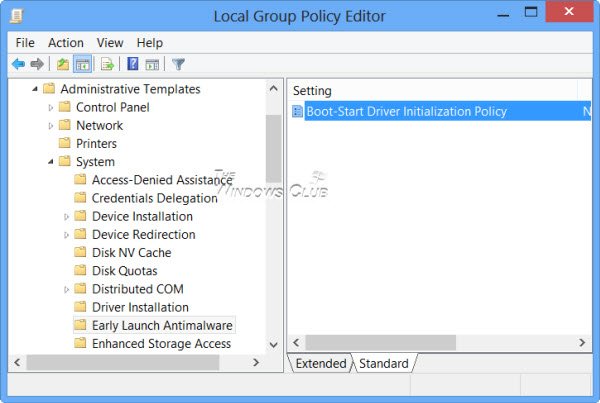
In the right pane, double-click on Boot-Start Driver Initialization Policy to configure it.
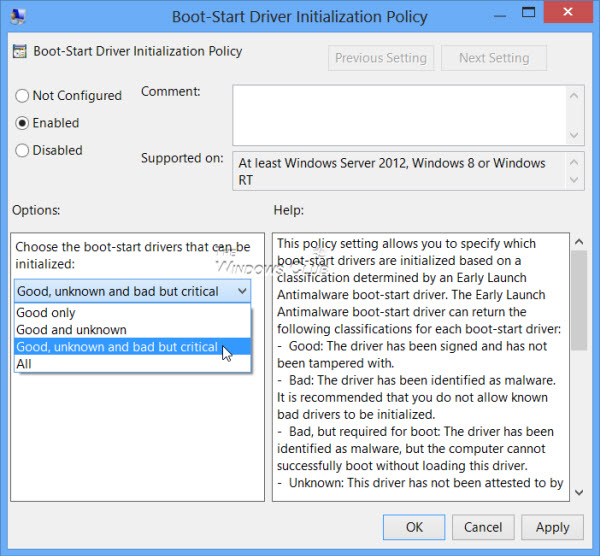
You will see the default configuration of Not Configured. If you disable or do not configure this policy setting, the boot-start drivers determined to be Good, Unknown or Bad but Boot Critical are initialized, and the initialization of drivers determined to be Bad is skipped.
If you Enable this policy setting, you will be able to choose which boot-start drivers to initialize the next time the computer is started.
If you are using Windows 11/10, check if your anti-malware software includes an Early Launch Antimalware boot-start driver. If it doesn’t, all boot-start drivers will be initialized, and you will not be able to take advantage of this new ELAM technology.
