If you prefer keeping your files and folder encrypted, you might have run into the EFS or Encryption File System algorithm. This inbuilt feature of Windows 11 and Windows 10 helps users secure their precious data. There is an alternate way of securing the user’s data on Windows 11/10. Still, the main advantage of EFS over BitLocker is that it can help users encrypt a particular folder rather than encrypting the whole hard drive partition.
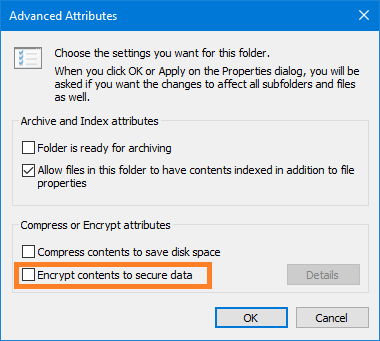
If you have a folder encrypted with Encrypting File System (EFS) and move a file inside that folder, it automatically gets encrypted. Some people like this feature being handy, but others would not. We will check out how to configure the settings for both choices.
Do not automatically encrypt files moved to encrypted folders
We will be trying the following methods to try to enable or disable automatic Encryption of files moved to Encrypted folders on Windows 11/10:
- Using the Register Editor Method.
- Using the Group Policy Editor Method.
I recommended you create a System Restore Point. This is because while doing these types of modifications, something may break on your computer’s software side. Or, if you do not have any habit of making a system restore point, I would encourage you to create one frequently.
1] Using the Registry Editor Method
Hit the WINKEY + R button to launch the Run utility, type in regedit, and hit Enter. Click on Yes for the UAC or User Account Control Prompt that you get.
Once Registry Editor opens, navigate to the following key location-
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer
Now, right-click on Explorer.
Select New > DWORD (32-bit) Value.
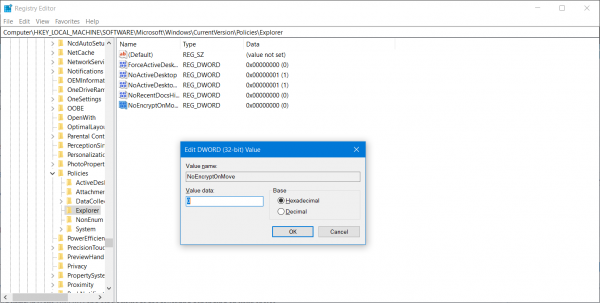
Name the newly created DWORD as NoEncryptOnMove and hit Enter to save it.
Double click on the NoEncryptOnMove DWORD and set its value to the following depending on your choice,
- 1: Disable Auto Encryption of files moved to Encrypted folders.
- 0: Enable Auto Encryption of files moved to Encrypted folders.
After setting a value, close the Registry Editor and Reboot your computer for the changes to take effect.
Read: A problem is preventing this folder from being encrypted
2] Using the Group Policy Editor Method
Open the Run box, type gpedit.msc, and hit Enter to open the Local Group Policy Editor. Navigate to the following path:
Computer Configuration\Administrative Templates\System
In the right-side pane, you will see Do not automatically encrypt files moved to encrypted folders. Double-click on it to set the policy.
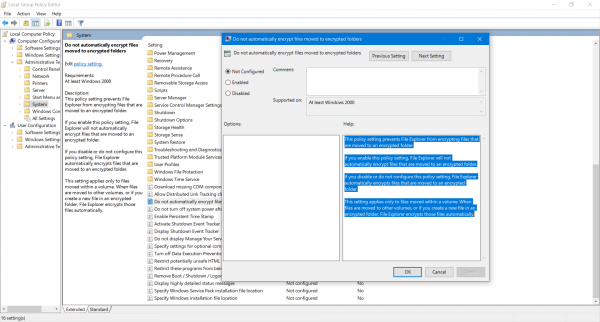
The description of the Group Policy entry says,
This policy setting prevents File Explorer from encrypting files that are moved to an encrypted folder. If you enable this policy setting, File Explorer will not automatically encrypt files that are moved to an encrypted folder. If you disable or do not configure this policy setting, File Explorer automatically encrypts files that are moved to an encrypted folder. This setting applies only to files moved within a volume. When files are moved to other volumes, or if you create a new file in an encrypted folder, File Explorer encrypts those files automatically.
Finally, select the following radio button as per your preferences:
- Not Configured or Disabled: Enable Auto Encrypt of files moved to EFS Encrypted folders.
- Enabled: Disable Auto Encrypt of files moved to EFS Encrypted folders.
Click on Apply and then click on OK.
Close the Group Policy Editor and Reboot your computer for the changes to take effect.
If you are new to this encryption technique on Windows 11/10, we have already covered some topics that will interest you:
- How to backup EFS encryption key in Windows.
- How to decrypt EFS encrypted Files and Folders in Windows.
- How to encrypt files with EFS Encryption on Windows.
That’s all.
What happens if you move encrypted files into an encrypted folder?
If a file is moved from an encrypted folder to another encrypted folder, it will remain encrypted. If an encrypted file is moved to a non-encrypted volume or folder, the state is changed to non-encrypted. So, it’s recommended first to decrypt, move the files, and then decrypt again. If the files were shared, the link would break, so you will need to share the link again.
Why does BitLocker turn on automatically?
If your Laptop or PC is part or registered with the Active Directory domain through Office 365 Azure AD, that is the reason. The feature is enabled by IT admins to ensure sensitive data is secured and cannot be decrypted without the key. Once the computer is removed from the domain, it will automatically decrypt everything.
Leave a Reply