Windows systems are routinely updated with the latest patches to improve the performance of a system. Microsoft releases the service and patches as part of the free update service to enhance the Windows computing experience. These updates are automatically installed based on the system settings and rarely need input from the end-users. The free updates are a part of Windows maintenance and support that releases software to fix errors effectively. In order to ensure secure computing, the Windows Update assures that the system is up to date with the latest security patches, hotfixes, and bug fixes.
Users can check the update history using PowerShell or the command line, or they can also check the update history via the Windows settings User interface. In this article, we discuss how to list all the history of Windows Update events using a task automation and configuration management tool such as PowerShell. One can also obtain information about all the current hotfixes or quick fix engineering updates that are downloaded as part of the software patches.
Check Windows Update History using PowerShell
Go to the Start menu and search for Windows PowerShell. Right-click on it and click on Run as administrator.
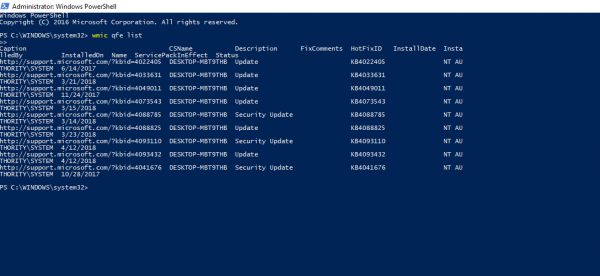
In the command line write the following command that lists the Hotfixes that are installed along with their ID, information on Installed on, description, etc.
wmic qfe list
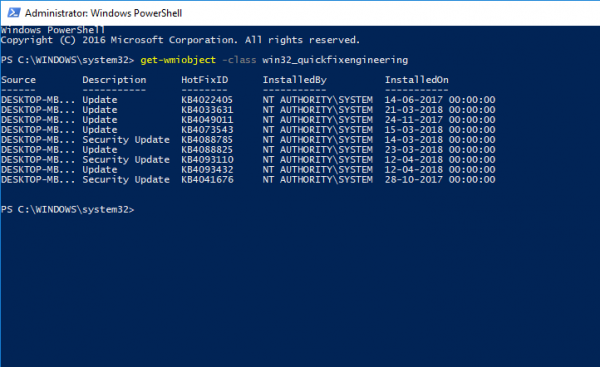
You can also type the following command to list the hotfixes and its associated description.
get-wmiobject -class win32_quickfixengineering
Additionally, one can also write a query to the computer for Update history and return a pointer to a list of matching records on the Windows system. The queries are written to list the WUA history in a PowerShell by defining a few functions to convert WUA history events of result code to a Name and get the last and latest 50 WUA history. You can modify the objects to list any number of past History of updated events.
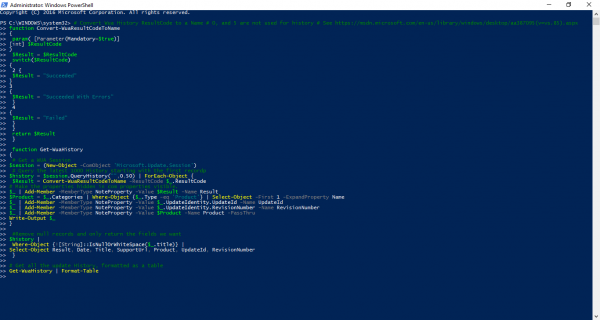
# Convert Wua History ResultCode to a Name # 0, and 5 are not used for history # See https://msdn.microsoft.com/en-us/library/windows/desktop/aa387095(v=vs.85).aspx
function Convert-WuaResultCodeToName
{
param( [Parameter(Mandatory=$true)]
[int] $ResultCode
)
$Result = $ResultCode
switch($ResultCode)
{
2
{
$Result = "Succeeded"
}
3
{
$Result = "Succeeded With Errors"
}
4
{
$Result = "Failed"
}
}
return $Result
}
function Get-WuaHistory
{
# Get a WUA Session
$session = (New-Object -ComObject 'Microsoft.Update.Session')
# Query the latest 1000 History starting with the first recordp
$history = $session.QueryHistory("",0,50) | ForEach-Object {
$Result = Convert-WuaResultCodeToName -ResultCode $_.ResultCode
# Make the properties hidden in com properties visible.
$_ | Add-Member -MemberType NoteProperty -Value $Result -Name Result
$Product = $_.Categories | Where-Object {$_.Type -eq 'Product'} | Select-Object -First 1 -ExpandProperty Name
$_ | Add-Member -MemberType NoteProperty -Value $_.UpdateIdentity.UpdateId -Name UpdateId
$_ | Add-Member -MemberType NoteProperty -Value $_.UpdateIdentity.RevisionNumber -Name RevisionNumber
$_ | Add-Member -MemberType NoteProperty -Value $Product -Name Product -PassThru
Write-Output $_
}
#Remove null records and only return the fields we want
$history |
Where-Object {![String]::IsNullOrWhiteSpace($_.title)} |
Select-Object Result, Date, Title, SupportUrl, Product, UpdateId, RevisionNumber
}
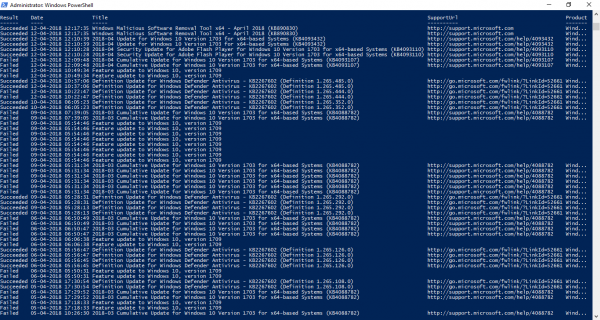
Then now, type the following command to get the updated history events with result date, update title, support URL, and update ID.
# Get all the update History, formatted as a table Get-WuaHistory | Format-Table
That’s all.
Sourced from stackoverflow.com.
Check Windows Update History using Command Prompt
In an elevated CMD execute the following command:
wmic qfe list
To find a specific update, you can use the KB number, eg for KB1234567, use:
wmic qfe | find "1234567"
How do I list Windows Update in PowerShell?
Open Windows Search using Win + S and type PowerShell. Once you find it, launch it. Done that, execute the following command. You can use this on the Windows terminal as well.
wmic qfe list
Do I need PowerShell in Windows 11?
PowerShell is a powerful cross-platform tool, and if you want to use script commands to change system settings and automate tasks, you need PowerShell in Windows 11. An advantage with Windows 11 is that you can execute the PowerShell command in Windows Terminal as well.