There are a number of things that make up a browser. It is not just about surfing the Internet but surfing it safely. Security is one of the most important aspects of any browser, and you need to know if your browser offers you enough protection. There are many aspects to browsing that you need to know exist, and that your browser does not compromise on security to let you surf the Internet.
Is my Browser secure?
If you are wondering if your browser is secure, here are some websites that are designed to test browsers. You can simply visit these websites and see where your browser stands in terms of security. Some of these websites allow you to share and thereby compare data gathered by running tests on two or more browsers.
- BrowserScope
- BrowserSpy
- PCFlank
- Qualys BrowserCheck
- Panopticlick
- Browsing Experience Security Check.
Let us take a look at these Browser Security Tests.
1] BrowserScope
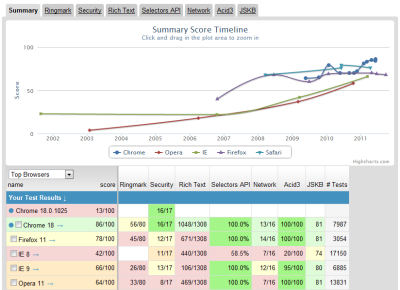
Browserscope.org is a website that offers a number of tests to determine the security of your browser. In addition to security, it also hosts a number of tests to let you know how it deals with scripts etc. The names of tests are listed on the upper tab.
Click on “About” under each test to see the number of tests and what the tests do. Click on “Results” to view the results of previous tests run by other users. Click on “Tests” to run the tests on your own browser. You can choose to share the results of your test with others by selecting “Share” on the “Tests” page.
2] BrowserSpy
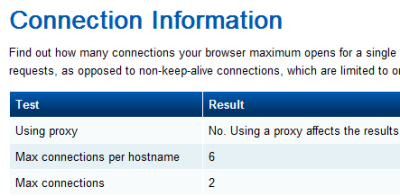
When you are browsing on the Internet, your browser leaves Digital Footprints. This allows other websites to gather information about you. This includes the applications installed on your computer and your surfing activity.
To know what all information your browser shares with other websites, log on – using the browser – to browserspy.dk. There are some 64+ tests available that let you know all the information your browser shares with the websites you visit.
3] PCFlank
PCFlank.com offers a number of tests that allow you to test your computer firewall, browser and more. Since we are talking about the browsers in this article, PCFlank does a good job of finding out what all information does your browser share with websites you are visiting. If any vulnerability is found, PCFlank will recommend steps to fix the problem(s).
4] Qualys BrowserCheck
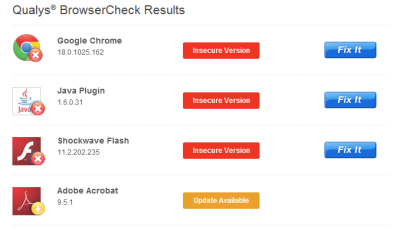
BrowserCheck shows you the browser you are using and gives you two options – 1) run a quick scan or 2) install a plug-in – to know if the browser has any security issues. In my case, I found three issues when performing the test with Google Chrome 18.0.1025.162. Check the image to see the issues and the recommendations I got from BrowserCheck.
Read: Browser Leak, Privacy, IP and Security test to test your web browser.
5] Panopticlick
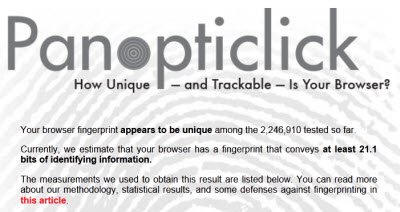
Panopticlick is another website that will check if your browser’s configuration is unique and then give you a uniqueness score. The more rare or unique your browser configuration, the less other websites will be able to track you, even if you limit or disable cookies. You may read about Browser Fingerprinting here.
6] Browsing Experience Security Check
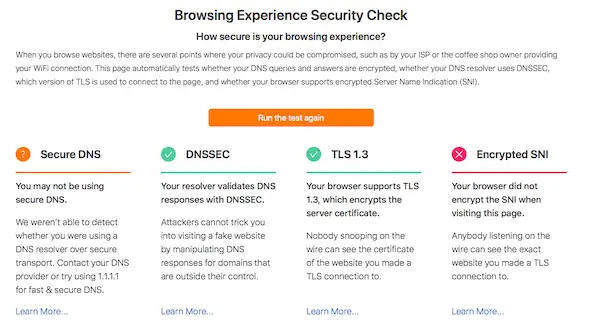
Cloudflare has developed an ESNI checker or Encrypted Server Name Indication tool. This service can check if your browsing experience is safe and the DNS queries are encrypted. That said, let’s understand one thing clearly. Don’t expect good results if you connect to Public WiFi or open networks. This tool can help you know the legitimacy of a tool you are using or any service that claims to be secure.
Cloudflare ESNI checker automatically test:
- Whether your DNS queries and answers are encrypted
- If DNS resolver uses DNSSEC,
- The version of TLS is used to connect to the page
- and whether your browser supports encrypted Server Name Indication (SNI).
Any failure indicates that browsing data could be vulnerable, i.e., anybody spoofing the network might tap into your data, including servers you are visiting or the certificate you are using. If the DNS response is fraudulent, you could also end up visiting and providing data to an unintended party.
Once you run this test, you will get information about each, if they failed, and what do they mean. It also suggests solutions to help you resolve. That said, let’s get to understand what each of these terms means:
- Secure DNS: Cloudflare DNS or Google DNS are examples of secure DNS. They make sure the data is encrypted when they leave DNS. Most of the ISPs don’t manage secure DNS. So if possible, make sure to change this on your computer or router.
- DNSSEC: If you pass this, it means websites sending data is actually sent by them, and not anybody else.
- TLS 1.3: It is the latest version of the TLS protocol and contains many improvements for performance & privacy.
- Encrypted SNI: This feature makes sure to keep the hostname private when you are visiting an Encrypted SNI-enabled site.
So if your browser supports it, does it make you secure?
Sadly, No. It is a two-way path. Support for ESNI should be available on the domain you are visiting. If the domain you visit doesn’t support DNSSEC, TLS 1.3, and Encrypted SNI, you are still potentially vulnerable.
These are some websites I know that answer the question – Is my browser safe. If you know of any other website or have a favorite, do share with us – and yes, let us know how your browser performed!
Now take a look at some of these tips to best secure your browsers.