Have you ever heard of ACLs? This is very important where computer security is concerned. In this article, we will discuss what ACLs are, along with the types of ACLs available right now.
What is Access Control List (ACL)?
For folks who want to learn what ACLs are, among other things, we suggest reading the information below as it contains everything you need to know.
- What does ACL stand for?
- What are ACLs, then?
- Why should we use ACLs?
- Where possible, can we place an ACL?
1] What does ACL stand for?
Many have been wondering what the acronym ACL stands for. Well, it means Access Control List, and it’s very important where network devices are concerned.
2] What are ACLs, then?
ACLs are basically a set of rules that watches traffic that is incoming and outgoing. From there, it will compare it with a set o defined statements. Now, we should also note that ACL is one of the most fundamental components in network security.
Additionally, an ACL and a Stateless Firewall are basically the same things in the sense that they only restrict, block, or allow all packets that flow from the source to the final destination.
When it comes down to where ACLs are usually found, we can say for certain that routers or firewalls. However, users can configure ACLs to run on devices that run in or on a network.
3] Why should we use ACLs?
The reason for using ACL is to provide security to a network. If ACL is not put into play, then any form of traffic is either allowed to enter or exit, and this is a bad thing because unwanted and dangerous traffic could siphon through.
When it comes down to improving security with ACL, users can choose to deny specific routing updates or deliver traffic flow control, for example.
Read: The Access Control List (ACL) structure is invalid
4] Where possible can we place an ACL?
Devices that are connected to the Internet need a way to filter traffic; therefore, one of the best places to configure ACLs is on-edge routers. From what we’ve come to understand, a routing device that supports ACL can be put in a position facing the Internet and also connecting to a form of buffer zone that divides the private network and the public Internet.
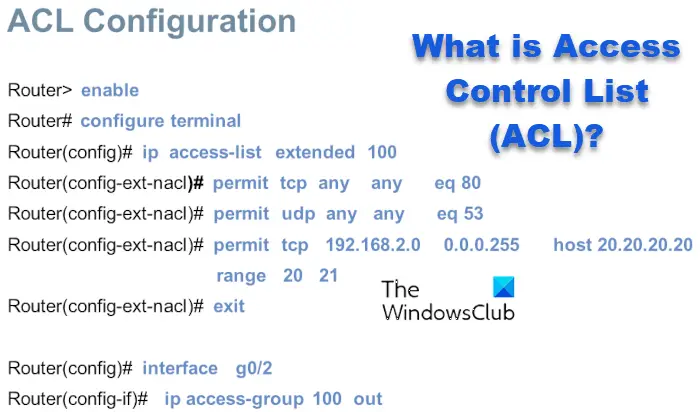
Furthermore, the option is there to configure an ACL to be able to protect against specific ports, for example, TCP or UDP.
What are the different types of ACLs?
There are two types of ACLs as far as we know, and they are Standard Access Lists and Extended Access Lists. Let us explains what these are about.
- Standard Access Lists
- Extended Access Lists
1] Standard Access Lists
When it comes down to the Standard Access Lists, it is only possible to source the IP address of a packet. We should point out that these types of Access Lists are not on the same power level when compared to Extended Access Lists, but the good news is, they do not require a lot of processor power from the router.
2] Extended Access Lists
If you choose to use Extended Access Lists, then expect more precise filtering when compared to the Standard Access Lists. Additionally, it is possible for users to evaluate destination and source IP addresses with ease, as also source and destination port, layer 3 protocol, and more.
Bear in mind that an Extended Access List is more difficult to configure and will consume more processor power than the Standard Access List. However, you are given a greater level of control.
Read: What is Data Science, and how do you become a Data Scientist?
What are ACLs used for?
Access Control List is a defined set of rules designed for controlling network traffic along with reducing network attacks from hackers. ACLs are also used to filter traffic that is also based on specific rules designated for outgoing and incoming of the computer network.
What are the benefits of Access Control List?
- Better security of internet-facing servers.
- More authority of access through entrance points.
- More control of access to and traffic between internal networks.
- More granular control of the user and group permissions.
I hope this helps.
Leave a Reply