What are Drive-by downloads? Drive-by download attacks occur when vulnerable computers get infected by just visiting a website. Findings from Microsoft Security Intelligence Report and many of its previous volumes reveal that Drive-by Exploits have become the top web security threat to worry about. Even the EU cybersecurity group, the European Network and Information Security Agency (ENISA) agrees.
Drive-by downloads
It’s accepted that Drive-by download attacks continue to be many attackers’ favorite type of attack. This is because the attack can be easily launched through the injection of malicious code into legitimate websites. Once injected, malicious code may exploit vulnerabilities in operating systems, web browsers, and web browser plugins such as Java, Adobe Reader, and Adobe Flash. The initial code that gets downloaded is usually small. But once it lands on your computer, it will contact another computer and pull the rest of the malicious coder to your system.
In short, vulnerable computers can be infected with malware simply by visiting such a website, without attempting to download anything. Such downloads happen without the person’s knowledge. These are called Drive-by downloads.
New data and findings have highlighted the relative prevalence of drive-by download sites, hosted on different web server platforms.
Certain representations made in the article via figures give a fair idea of the concentration of drive-by download pages in countries and regions throughout the world. Locations with relatively high concentrations of drive-by download URLs in both quarters include,
- Syria – 9.5 drive-by URLs for every 1,000 URLs
- Latvia – 6.6
- Belarus – 5.6.
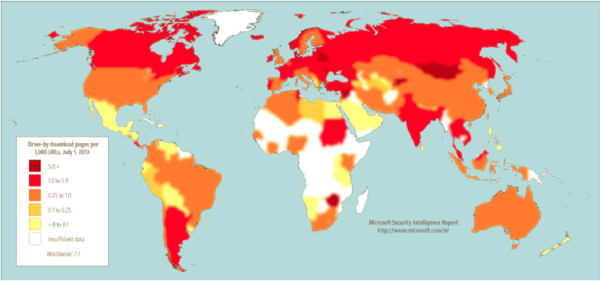
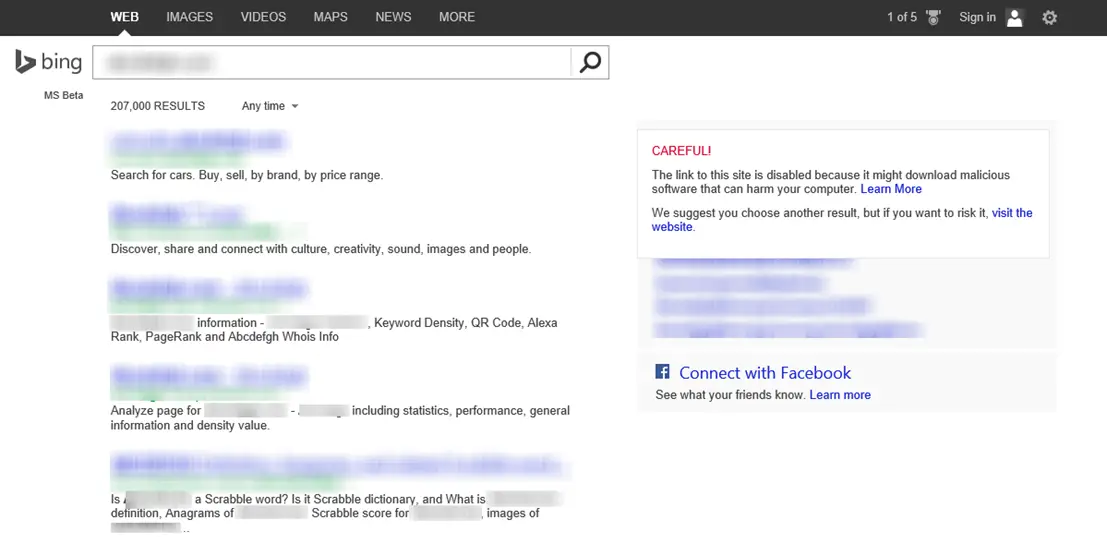
The Drive-by Download concentrations were tracked by Bing at the end of the second quarter of 2013. Accordingly, the measures taken by the search engine to help protect users from drive-by download attacks include analysis of websites for exploits when indexing them and displaying warning messages when listings for drive-by download pages appear in the list of search results.
Prevent Drive-by download attacks
A TechNet article features steps for developers and IT Professionals to be taken for managing the risk related to drive-by download attacks. Some of the measures include:
Preventing web servers from being compromised. Web servers can be compromised if they are not kept updated with the latest security updates. So,
- Keep the server’s operating system(s) up to date
- Software installed on these web servers up to date
- Check out SDL Quick Security Reference Guides for the latest updates
- Avoid browsing the Internet from web servers or using them to open email and email attachments.
- Register your site with Bing webmaster tools and Google Webmaster, so that search engines can proactively inform you if they detect something bad on your site.
As a user, you can take the following precautions:
- Make sure your Windows operating system and web browser is fully up-to-date.
- Use a good security software and again ensure that it has the latest definitions always
- Use minimum browser addons as they often get compromised
- Using a URL Scanner addons for your browser might also be an option you may want to consider
- If you are using Internet Explorer make sure your SmartScreen is turned on.
- And finally, develop a habit of safe browsing and be selective about which sites you browse regularly.
Do let us know if your computer has ever been infected with a drive-by download attack.
Now read: What is Malvertising?