If you want to set various policies to use a password for fixed data drives of BitLocker in Windows 11 or Windows 10, here is how you can do that. You can configure the use of passwords for BitLocker fixed data drives using Local Group Policy Editor and Registry Editor. It is possible to enable or disable passwords for fixed data drives, password complexity, and minimum password length using this guide.
How to configure use of Passwords for Fixed Data Drives in BitLocker
To configure use of passwords for fixed data drives, follow these steps:
- Search for gpedit in the Taskbar search box.
- Click on the search result.
- Go to BitLocker Drive Encryption > Fixed Data Drives in Computer Configuration.
- Double-click on the Configure use of passwords for fixed data drives setting.
- Choose the Enabled option.
- Tick the Require password for fixed data drive
- Set the password complexity.
- Choose the minimum length of password for fixed data drive.
- Click the OK button.
Let’s delve into these steps in detail.
To get started, search for gpedit or gpedit.msc in the Taskbar search box and click on the individual search result to open the Local Group Policy Editor on your computer. Then, navigate to this path:
Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption > Fixed Data Drives
On the right-hand side, you can see a setting named Configure use of passwords for fixes data drives. You need to double-click on this setting and choose the Enabled option.
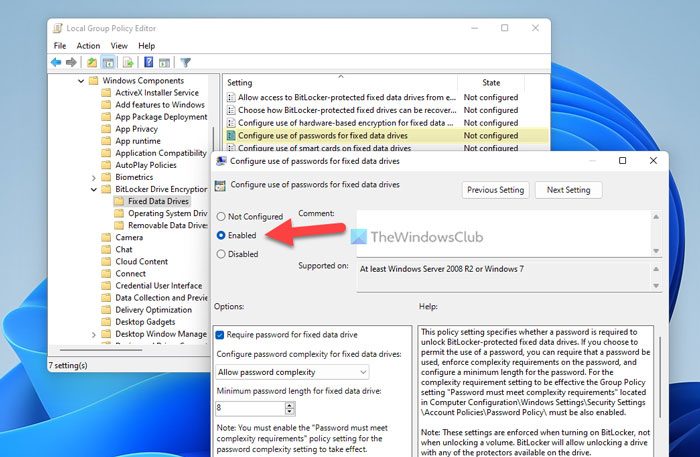
Next, you have three options to set up:
- Require password for fixed data drive: You can tick the checkbox to enable.
- Choose a password complexity setting.
- Select the minimum password length.
Finally, click the OK button to save the change.
How to configure use of passwords for fixed data drives using Registry
To configure use of passwords for fixed data drives using Registry, follow these steps:
- Press Win+R > type regedit and click the OK button.
- Click the Yes button.
- Go to Microsoft in HKLM.
- Right-click on Microsoft > New > Key and name it FVE.
- Right-click on FVE > New > DWORD (32-bit) Value.
- Set the name as FDVPassphrase.
- Double-click on it to set the Value data as 1.
- Repeat these steps to create three more REG_DWORD values.
- Name them as FDVEnforcePassphrase, FDVPassphraseComplexity, and FDVPassphraseLength.
- Set the Value data of FDVPassphrase as 1.
- Set the Value data of FDVPassphraseLength anything from 6 to 20.
- Set the Value data of FDVPassphraseComplexity as 0, 1, or 2.
- Restart your computer.
Let’s find out more about these steps.
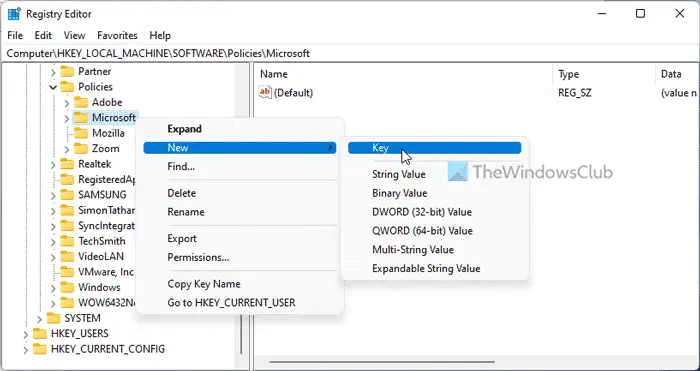
First, press Win+R to open the Run prompt, type regedit, click the OK button, and click on the Yes option to open the Registry Editor. Then, go to this path:
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft
Right-click on Microsoft > New > Key and set the name as FVE.
Right-click on FVE > New > DWORD (32-bit) Value and name it as FDVPassphrase.
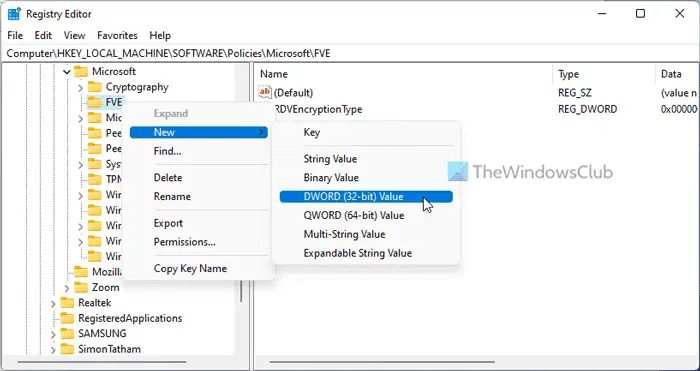
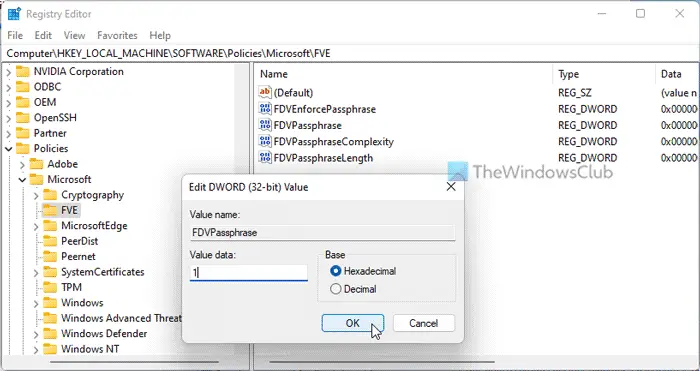
Double-click on it and set the Value data as 1.
Then, you need three more REG_DWORD values:
- FDVEnforcePassphrase: 1 to enable
- FDVPassphraseComplexity: 0/1/2
- FDVPassphraseLength: 6 to 20
Then, double-click on each REG_DWORD value and set the Value data as mentioned above.
Finally, close all windows and restart your computer.
Read: How to change BitLocker PIN in Windows 11/10
How can we enforce BitLocker encryption?
To enforce BitLocker encryption in Windows 11/10, you need to use a PIN or password for the protected drive. For that, you can use Control Panel, Command Prompt, Windows PowerShell, or Windows Terminal. In the Windows Terminal, you need to use this command: manage-bde -changepin C:.
How do I enable Require additional authentication at startup?
To enable the Require additional authentication at startup for BitLocker, you need to use the Local Group Policy Editor. For that, go to the BitLocker Drive Encryption > Operating System Drives. Double-click on the Require additional authentication at startup setting and choose the Enabled option. Then, expand the drop-down menu and choose Require start PIN with TPM option. Click the OK button to save the change.
That’s all! Hope it helped.
Read: Specify Minimum Length for BitLocker Startup PIN in Windows 11/10.
Leave a Reply