A Cyber Attack is an attack initiated from a computer against another computer or a website to compromise the integrity, confidentiality, or availability of the target and the information stored in it. This article explains what cyber-attacks are, its definition, and types, and talks about how to prevent them and the course to take in the event of a cyber attack. Cyber Attacks, in a way, can be broadly considered to be a part of Cyber Crime. An attack to commit a Cyber Crime can be called as a Cyber Attack!
Cyber Attacks Definition
According to the Practical Law Company, Whitepaper on Cyber Attacks, conducted by hklaw.com, the definition of Cyber Attacks is as follows:
A Cyber Attack is an attack initiated from a computer against a website, computer system or individual computer (collectively, a computer) that compromises the confidentiality, integrity or availability of the computer or information stored on it.
The definition has three distinct factors: [1] Attack or an illegal attempt to [2] gain something from a [3] computer system. Generally speaking, a system is a collection of units that work collectively towards a common goal. Thus, whether it is a single or a collection of computers – offline or online (websites/intranets), it is a system as they work to facilitate something or the other. Even a single computer has many components that work together for a common goal and is called a computer system.
The main factor is illegal access to such a system. The second factor is the target system. The final factor is the gains to the attacker. It should be noted that illegal access must have the motive to compromise the target system in a way that the attacker gains something, such as information stored in the system or total control of the system.
Read: Why are websites hacked?
What are the types of Cyber Attacks?
There are many methods of Cyber Attacks, from malware injection to phishing to social engineering to the internal stealing of data. Other advanced but common forms are DDoS Attacks, Brute Force attacks, hacking, and holding a computer system (or a website) for ransom using direct hack or Ransomware.
Some of them have been listed below:
- Gaining, or attempting to gain, unauthorized access to a computer system or its data.
- Disruption or denial of service attacks (DDoS)
- Hacking a website or mal-facing the site
- Virus or malware installation
- Unauthorized use of a computer for processing data
- Inappropriate use of computers or applications by employees of a company in a way that harms the company.
The last one – employees’ inappropriate use of computers or apps – could be deliberate or due to a lack of knowledge. One has to figure out why an employee, for example, tried to enter the wrong data or access a particular data record that one was not authorized to change.
Social engineering could also be a cause whereby an employee deliberately tries to hack into the database – to help a friend! The employee was befriended by a criminal and is emotionally forced to obtain innocent data for the new friend.
While we are here, it is also advisable to teach the employees about the dangers of public WiFi and why they should not use it for office work.
Read: What are Honeypots, and how can they secure computer systems?
Cyber Attacks Response
Prevention is always better than cure. You must have heard this several times. The same applies to the field of IT when it comes to protection against Cyber Attacks. However, assuming that your computer(s) or website(s) were attacked, even after taking all the precautions, there are certain common general response steps laid down:
- Did the attack happened or is someone calling in to play a prank;
- If you still have access to your data, back it up;
- If you cannot access your data and the hacker demands a ransom, you may consider approaching the legal authorities.
- Negotiate with the hacker and regain the data
- In the case of social engineering and employees misusing their privileges, checks should be conducted to determine if the employee was innocent or acted deliberately.
- In the case of DDoS attacks, the load should be mitigated to other servers so that the website returns online as soon as possible. You may rent out servers for a while or use a cloud app to minimize costs.
Please read the whitepaper mentioned under the References section for exact and detailed information on responding the legal way.
Read: Why would someone want to hack my computer?
Prevention of Cyber Attacks
You might already know that there is no 100% foolproof method to counter cybercrime and cyber attacks, but still, you have to take as many precautions to protect your computers.
The primary things to be done are to use good security software that scans for viruses and looks for different types of malware, including but not limited to ransomware, and stops it from entering the computer. Mostly these malicious codes are injected into your computers by visiting or downloading things from non-reputed websites, Drive-by downloads, and compromised websites that display malicious advertisements, also known as Malvertising.
Along with the antivirus, you should use a good firewall. While the built-in firewall in Windows 10/8/7 is good, you can use third-party firewalls stronger than the default Windows Firewall.
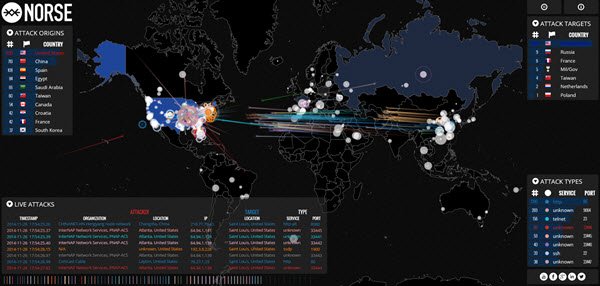
Read: Malware Tracker Maps that let you view Cyber Attacks in real-time.
If it is a corporate computer network, ensure no Plug and Play support exists in any of the user computers. Employees should not be able to plug in Flash drives or their Internet dongles into the USB. The company’s IT department should also keep a watch on all the network traffic. Using a good network traffic analyzer helps prompt attendance to strange behaviors arising out of any terminal (employee computer).
Read: Best Cybersecurity Practices for Small Business.
For protection against DDoS attacks, the website is better mitigated to different servers instead of being hosted simply on a single server. The best method would be to have a mirror constantly up using a cloud service. That will greatly reduce the chances of a DDoS being successful – at least not for a long time. Use a good firewall like Sucuri and take some basic steps to protect and secure your website.
Here are a few useful links that display real-time digital hack attack maps:
- ipviking.com
- digitalattackmap.com
- fireeye.com
- norsecorp.com
- honeynet.org.
Please have a look at them. They are pretty interesting!
Read: What is Buffer Overflow Attack?
If you have anything to add, please do share.
Read next:
Password Spray Attacks | Brute Force Attacks | Living Off The Land attacks | Surfing Attacks | Credential Stuffing attacks | Domain Fronting | Cold Boot Attacks | Command and Control Cyberattack | SSL Stripping attack.