The Internet is not a secure place for exchanging information. There are many prying eyes on you trying to get a piece of your secret information. In this era of free-flowing data, most of us use the Internet connection and have access to information from all across the world at our fingertips. And the Tor Network works perfectly here, as it routes the user’s system’s Internet traffic over several places on the Internet. Thus, it hides the real source of the communication and secures the user’s personal identity. Here is a detailed analysis of Tor or The Onion Router network and how it is used.
Tor Network

What is Tor Network?
TOR, or the Onion Router, is a free software and open network which allows users to improve their privacy and security over the Internet. Putting in simple words, Tor is software that allows users to browse the Web anonymously.
Who Developed Tor Network?
The Tor Project has developed Tor Network. This is a non-profit organization that conducts research and development on online privacy and obscurity.
Why Was Tor Network Designed?
TOR is typically designed to stop people (including government agencies and corporations) from tracking a user’s identity, location or browsing habits.
Why Was Tor Network Called Onion Router?
Originally Tor was called The Onion Router; this is because this software uses a technique known as onion routing to conceal information about user activity.
Is Tor Used For Browsing The Web Only?
The Tor network entails Tor relays that route traffic. It is not just used for web browsing but can also be used by many applications which want to route traffic anonymously. Applications like Instant Messaging (IM), Internet Relay Chat (IRC), and web browsers can all use Tor effectively to route traffic across the Internet anonymously. You can access the Dark Web using the TOR browser.
How does Tor work
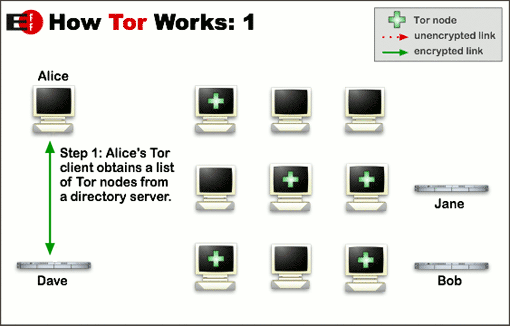
Tor routes the internet traffic through the Tor Network. We already mentioned earlier that Tor could be used by a number of applications, but here let’s take the web browser as an example to explain how Tor works.
- When a user tries to connect to a server using Tor, their browser launches an encrypted link with a Tor server. Further, it establishes a circuit or a path through the Tor network. This very path routes the traffic through several Tor servers. Note this path is random and changes every 10 minutes.
- Once the path is established through the network, the packets are routed from one server to the other. On the network chain, any given server knows only the server from where it has received the data and the next server to send that very data. None of the servers in this chain would actually know the entire path of the traffic that it takes through the network. This way Tor prevents in disclosing where the traffic came from and where it is going to.
- Tor encrypts the traffic using a layering scheme; this is where the Onion concept comes from. For instance, as the traffic passes through the nodes in the Tor network, a layer of encryption is stripped off at each of the nodes, this looks like layers of an onion.
- While using the Tor browser, the traffic is encrypted between the browser and the Tor network. It is sent anonymously through the network and the last node or the “exit node” uses an “Unencrypted” link to communicate with the destination server outside the Tor network. Note that this final hop is not encrypted.
Read: How to completely delete yourself from the internet
Who can use Tor network and for what purpose
Many people believe that their identity is properly protected under normal usage conditions. But that is a totally wrong concept as if you are not using a VPN software or Tor; there is a high chance for your identity to be traced. Tor can help users ensure that their entire online activity and personal information stays secret.
Typically Tor Network is being used to:
- Keep internet activities private from websites and advertisers
- Answer cyber-spying concerns
- Evade hostile government censorship
- Avoid surveillance
- Ensure maximum privacy over the Internet
The US Navy is a key user of the Tor Network. The primary audience for Tor includes journalists, legal activists, whistle-blowers, and people living in a country with censorship. Other key users include bloggers, business executives, IT professionals, and law enforcement officers. Also, the police is a users of Tor; they use this network when they need to mask their IP addresses while investigating doubtful websites and services.
Despite the good intentions of the Tor Project, Tor has unfortunately developed a bad reputation in the mainstream press. With the growth and prosperity of Tor and the massive advantage of the cover it provides, the Tor Network has actually become a shelter for nasty individuals.
How to get Tor
Tor is free-to-use software; you can simply download and install the Tor browser. It is a modified version of Firefox which is available for Windows, Mac OS X, and Linux. For mobile browsing, Orbot is an Android app available to download from Google Play.
Using Privoxy And Tor For Increased Anonymity
Tor Network has some major disadvantages:
- Long enough session
- Slow performance
- All the requests come through one node.
To conclude, in simple words, the Tor Network can be painfully slow. This is one major reason why we suggest using Privoxy with Tor.
What is Privoxy?
Privoxy is a non-caching web proxy with advanced filtering capabilities. It is used for enhancing privacy, modifying web page data and HTTP headers, controlling access, and removing ads and other obnoxious Internet junk. Privoxy and Tor together make a great team. They add two additional layers of protection to your anonymous VPN.
Tor is a perfect tool to protect your digital privacy, even while browsing the Internet, without revealing who you actually are!
Now read about the OONI or Open Observatory of Network Interference Project from TOR.



I guess using a VPN is far better than TOR. I have been using PureVPN and it works best for me.