Multi-user functionality in Windows has enabled us to use it conveniently in public places like schools, colleges, offices, etc. At these places, there is generally an administrator, who manages to keep an eye on the activities of users working therein. Sometimes, users go beyond their limits and modify accounts configured in Workgroup mode. This can have security repercussions, and thus we should configure Windows to track down user activities.
By configuring Windows for monitoring user activities, we can increase the security of the administration and can also punish the victim users by observing their records in case of an offense. In this article, we’ll tell you the way to track user activities in Windows 11/10/8.1/8/7 using Audit Policy. Here is how:
Track User Activity using Audit Policy in WorkGroup Mode
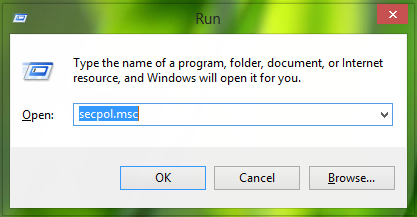
1. Press Windows Key + R combination, type put secpol.msc in Run dialog box and hit Enter to open the Local Security Policy.
2. In the Local Security Policy window, expand Security Settings > Local Policies > Audit Policy. Now you should get your window resembled with this one:
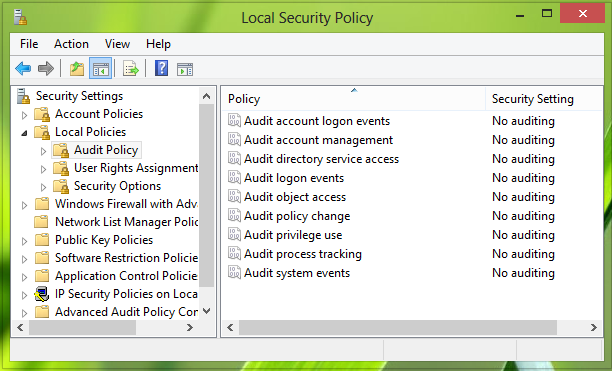
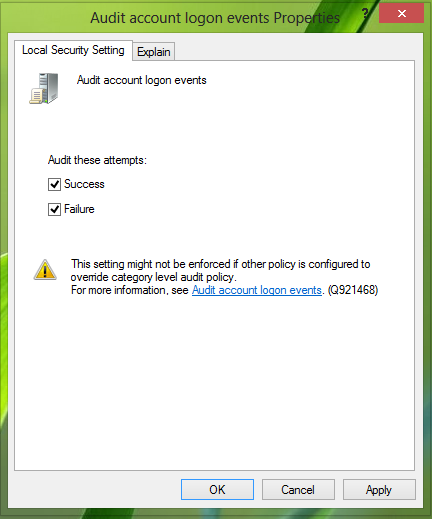
3. In the right pane, you can see 9 Audit…[] policies have No auditing as pre-defined security setting. Click one by one all the policies and make the selection to Success and Failure, click Apply followed by OK for each policy.
In this way, we will have configured Windows to track down user activity.
Follow these steps to get the traced records:
Trace User Activity Using Event Viewer
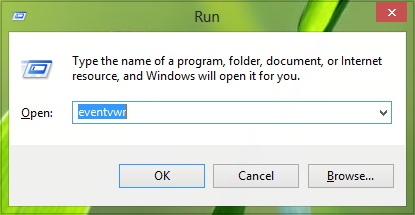
1. Press Windows Key + R combination, type put eventvwr in Run dialog box and hit Enter to open the Event Viewer.
2. Now, in the Event Viewer window, from the left pane, select Windows Logs > Security. Here Windows keeps a record of every event concerning security.
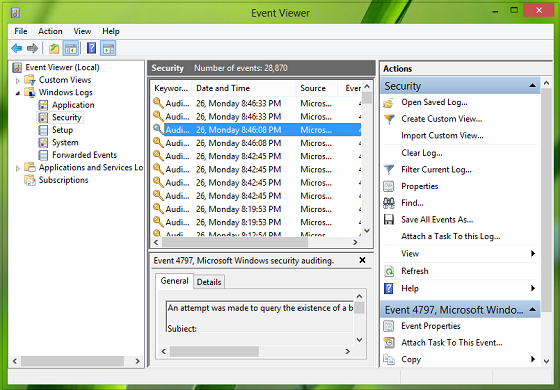
3. From the center pane, click any event to get its info:
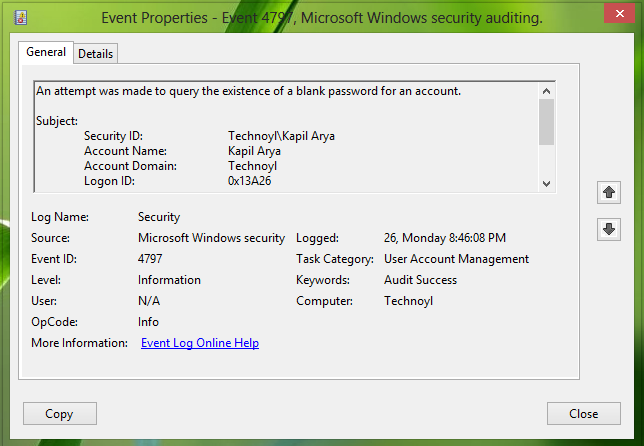
Now, here is the list of the event IDs which covers the user activities for the accounts in the workgroup mode:
1. Create User: Below are the Event IDs that get logged when the user is created.
- Event ID: 4728 | Type: Audit Success | Category: Security Group Management | Description: A member was added to a Security-enabled global group.
- Event ID: 4720 | Type: Audit Success | Category: User Account Management | Description: A User account was created.
- Event ID: 4722 | Type: Audit Success | Category: User Account Management | Description: A User account was enabled.
- Event ID: 4738 | Type: Success Audit | Category: User Account Management | Description: A User account was changed.
- Event ID: 4732 | Type: Success Audit | Category: Security Group Management | Description: A member was added to a Security-enabled local group.
2. Delete User: Below are the Event IDs that get logged when the user is deleted.
- Event ID: 4733 | Type: Success Audit | Category: Security Group Management | Description: A member was removed from a Security-enabled local group.
- Event ID: 4729 | Type: Success Audit | Category: Security Group Management | Description: A member was added to a Security-enabled global group.
- Event ID: 4726 | Type: Success Audit | Category: User Account Management | Description: A User account was deleted.
3. User Account Disabled: Below are the Event IDs that get logged when the user is disabled.
- Event ID: 4725 | Type: Success Audit | Category: User Account Management | Description: A User account was disabled.
- Event ID: 4738 | Type: Success Audit | Category: User Account Management | Description: A User account was changed.
4. User Account Enabled: Below are the Event IDs that get logged when the user is enabled.
- Event ID: 4722 | Type: Success Audit | Category: User Account Management | Description: A User account was enabled.
- Event ID: 4738 | Type: Success Audit | Category: User Account Management | Description: A User account was changed.
5. User Account Password Reset: Below are the Event IDs that get logged when the User Account Password gets reset.
- Event ID: 4738 | Type: Success Audit | Category: User Account Management | Description: A User account was changed.
- Event ID: 4724 | Type: Success Audit | Category: User Account Management | Description: An attempt was made to reset an account’s password.
6. User Account Profile Path Set: Below is the Event ID that gets logged when Profile Path gets set for a user account.
- Event ID: 4738 | Type: Success Audit | Category: User Account Management | Description: A User account was changed.
7. User Account Rename: Below are the Event IDs that get logged when the User Account is renamed.
- Event ID: 4781 | Type: Success Audit | Category: User Account Management | Description: The name of an account was changed.
- Event ID: 4738 | Type: Success Audit | Category: User Account Management | Description: A User Account was changed.
8. Create Local Group: Below are the Event IDs that get logged when the Local Group is created.
- Event ID: 4731 | Type: Success Audit | Category: Security Group Management | Description: A Security-enabled local group was created
- Event ID: 4735 | Type: Success Audit | Category: Security Group Management | Description: A Security-enabled local group was changed
9. Add User to Local Group: Below is the Event ID that gets logged when the user gets added to the Local group.
- Event ID: 4732 | Type: Success Audit | Category: Security Group Management | Description: A member was added to a Security-enabled local group
10. Remove User from Local Group: Below is the Event ID that gets logged when the user is removed from the Local group.
- Event ID: 4733 | Type: Success Audit | Category: Security Group Management | Description: A member was removed from a Security-enabled local group
11. Delete Local Group: Below is the Event ID that gets logged when the Local Group is deleted.
- Event ID: 4734 | Type: Success Audit | Category: Security Group Management | Description: A Security-enabled local group was deleted
12. Rename Local Group: Below are the Event IDs that get logged when the Local Group is renamed.
- Event ID: 4781 | Type: Success Audit | Category: User Account Management | Description: A name of an account was changed
- Event ID: 4735 | Type: Success Audit | Category: Security Group Management | Description: A Security-enabled local group was changed
In this way, you can trace users with their activities. This article is applicable for Windows 11/10/8.1 in Workgroup Mode. For Active Directory Domain, the procedure will be different.
Also read: How to enable Local Administrator Account in WorkGroup Mode.