In an earlier post, we have seen how to bypass login screen in Windows 7 and older versions by taking advantage of AutoLogon tool offered by Microsoft. It was also mentioned that major benefit of using AutoLogon tool is that your password is not stored in plain text form as is done when you manually add the registry entries. It is first encrypted and then stored so that even the PC Administrator does not have access to the same. In today’s post, we’ll talk about how to decrypt the DefaultPassword value saved in Registry editor by using AutoLogon tool.
First things first, you’d still need to have Administrator privileges in order to decrypt the DefaultPassword value. The reason behind this obvious restriction is that such encrypted system and user data are governed by a special security policy, knows as Local Security Authority (LSA) which grants the access only to the system administrator. So, before we make our move on decrypting the passwords, let’s take a look at this security policy and it’s co-related know-hows.
LSA – What it is and how it stores data
LSA is used by Windows to manage the system’s local security policy and perform the auditing and authentication process on the users logging into the system while saving their private data to a special storage location. This storage location is called LSA Secrets where important data used by LSA policy is saved and protected. This data is stored in an encrypted form in the registry editor, in the HKEY_LOCAL_MACHINE/ Security/ Policy/ Secrets key, which is not visible to general user accounts due to restricted Access Control Lists (ACL). If you have the local administrative privileges and know your way around LSA Secrets, you can get access to the RAS/VPN passwords, Autologon passwords, and other system passwords/keys. Below is a list to name a few.
- $MACHINE.ACC: Related to Domain Authentication
- DefaultPassword: Encrypted password value if AutoLogon is enabled
- NL$KM: Secret key used to encrypt cached domain passwords
- L$RTMTIMEBOMB: To store the last date value for Windows activation
In order to create or edit the secrets, there is a special set of APIs available for software developers. Any application can get access to the LSA Secrets location but only in the context of the current user account.
How to decrypt the AutoLogon password
Now, in order to decrypt and uproot the DefaultPassword value stored in LSA Secrets, one can simply issue a Win32 API call. There is a simple executable program available for getting the decrypted value of DefaultPassword value. Follow the below steps to do so:
- Download the executable file from OneDrive.com – it’s just 2 KB in size. It is a privately hosted file so get it scanned with your antivirus.
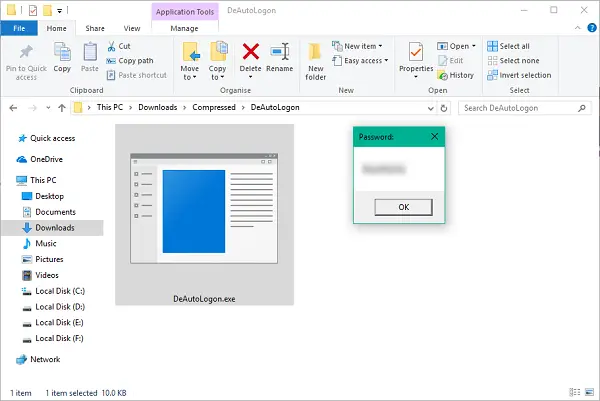
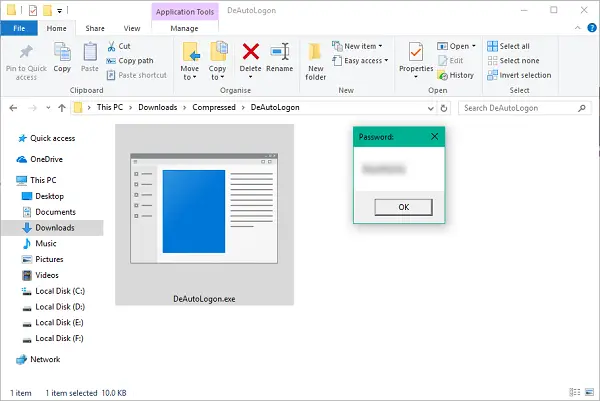
- Extract the contents of DeAutoLogon.zip file.
- Right-click DeAutoLogon.exe file and run it as Administrator.
- If you have the AutoLogon feature enabled, DefaultPassword value should be right there in front of you.
If you try to run the program without Administrator privileges, you’d run into an error. Hence, make sure to acquire local administrator privileges before running the tool. Hope this helps!
Where is the Autologon password stored?
The Autologon password is stored in the Registry Editor. You need to navigate to this path to find the same: HKEY_LOCAL_MACHINE/ Security/ Policy/ Secrets. Here you can find a value named DefaultPassword. You need to go through this value to find the password on your computer.
Where are credentials stored in the registry?
If you are talking about the cached credentials on Windows 11 or Windows 10, you need to head to the HKEY_LOCAL_MACHINE\Security\Cache location. However, if you want to find the same in the File Explorer, you need to navigate to this path: %systemroot%\System32\config\SECURITY. For that, press Win+R to open the Run prompt and enter the aforementioned text.
Shout out in the comments section below in case you’ve got any questions.