Distributed Denial of Service or DDoS has a long history, and it became completely mainstream when the Anonymous group started its operations against any website against Wikileaks. Until then, the term and what it meant was known only to people with knowledge of Internet Security.
Distributed Denial of Service
I intend to cover some notable DDoS methods in this article before discussing methods to avoid or prevent DDoS attacks.
What are DDOS attacks?
I am sure all of you know its meaning. For those new to the term, it is “distributed” Denial of Service – caused by the way too many requests to the server than it can handle.
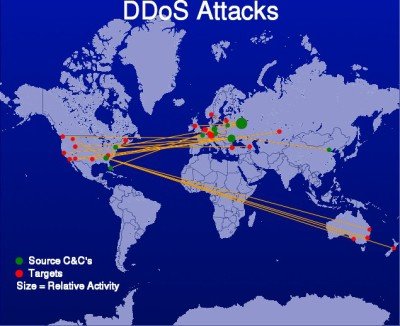
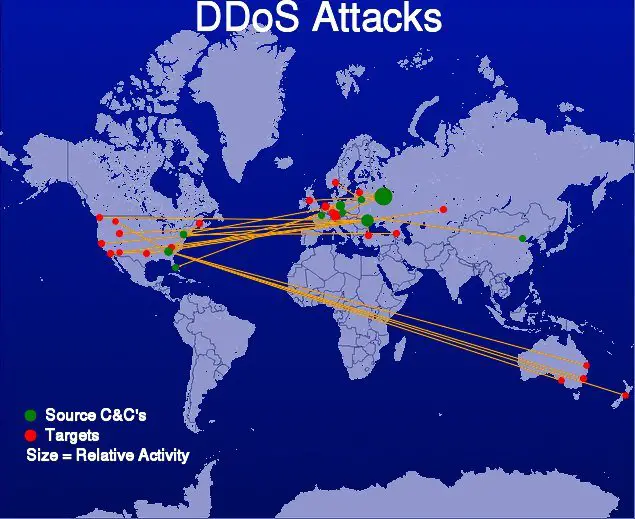
When unable to process requests in real-time due to high traffic that is intentionally being sent by a number of compromised computers, the site server hangs and stops responding to any more requests from different clients. The network of compromised computers is referred to as BOTNETS. Basically, all the computers and smart appliances in the network are controlled by hackers and the people owning those computers are not aware that they’ve been hacked.
Since the requests are many and come from different places (regions of hacked computers may vary), it is called a “Distributed Denial of Service” or DDoS for short. For a DDoS to happen, the number and intensity of connection attempts should be more than what the targeted Server can handle. If the bandwidth is high, any DDoS attacker will need more computers and more frequent requests to bring the server down.
TIP: Google Project Shield offers free DDoS protection yo select websites.
Popular DDoS Methods & Attack Tools
We just discussed one of the many DDoS methods in the above section. It is called “distributed denial” as the communication lines are opened by not one or two but hundreds of compromised computers. A hacker who has access to many computers can anytime start sending requests to the server he wants to bring down. Since it is not one or two but many computers placed across the planet, it is “distributed”. The server can no longer cater to incoming requests and crashes.
Among other methods is the Handshake method. In a normal scenario, your computer opens a TCP line with the server. The server responds and waits for you to complete the handshake. A handshake is a set of actions between your computer and server before actual data transfer begins. In the case of an attack, the hacker opens TCP but never completes the handshake – thus keeping the server waiting. Another website down?!
A quick DDoS method is the UDP method. It employs DNS (Domain Name Service) Servers for initiating a DDoS attack. For normal URL resolutions, your computers employ User Datagram Protocol (UDP) as they are faster than the standard TCP packets. UDP, in short, is not much reliable as there is no way to check dropped packets and things like that. But it is used wherever speed is a major concern. Even online gaming sites use UDP. Hackers use the weaknesses of UDP packets to create a flood of messages to a server. They can create fake packets that appear as coming from the targeted server. The query would be something that would send large amounts of data to the targeted server. Because there are multiple DNS resolvers, it becomes easier for the hacker to target a server that brings down the site. In this case, too, the targeted server receives more queries/responses than it can handle.
Read: What is Ransom Denial of Service?
There are many third-party tools that act like a botnet if the hacker does not have many computers. I remember one of the many hacking groups asking people on Twitter to fill in random data in some web page form and hit Send. I did not do it but was curious how it worked. Probably, it too sent repeated spam to servers until the saturation was crossed and the server went down. You can search for such tools on the Internet. But remember that hacking is a crime, and we do not endorse any Cyber Crimes. This is just for your information.
Having talked about methods of DDoS attacks, let us see if we can avoid or prevent DDoS attacks.
Read: What is Black Hat, Grey Hat or White Hat Hacker?
DDoS protection & prevention
There is not much you can do but still, you can reduce DDoS chances by taking some precautions. One of the most used methods by such attacks is to clog your server bandwidth with fake requests from botnets. Buying a little more bandwidth will reduce or even prevent DDoS attacks, but it can be a costly method. More bandwidth means paying up more money to your hosting provider.
It is also good to use a distributed data movement method. That is, instead of just one server, you have different datacenters that respond to requests in parts. It would have been very costly in the older days when you had to buy more servers. These days, data centers can be applied to the cloud – thus reducing your load and distributing it from across servers instead of just one server.
Read: What is Buffer Overflow Attack?
You may even use mirroring in case of an attack. A mirror server contains the most recent (static) copy of the items on the main server. Instead of using the original servers, you might want to use mirrors so that the traffic coming in can be diverted, and thus, a DDoS can be failed/prevented.
In order to close the original server and start using mirrors, you need to have information about incoming and outgoing traffic on the network. Use some monitor that keeps displays you the true state of traffic and if it alarms, closes the main server, and diverts traffic to mirrors. Alternatively, if you are keeping a tab on traffic, you may use other methods to deal with the traffic, without having to shut it down.
You can also consider using services like Sucuri Cloudproxy or Cloudflare as they offer protection against DDoS attacks.
These are some methods I could think of, to prevent and reduce DDoS attacks, based on their nature. If you have had any experiences with DDoS, please share it with us.
Also read: How to prepare for and deal with a DDoS attack.